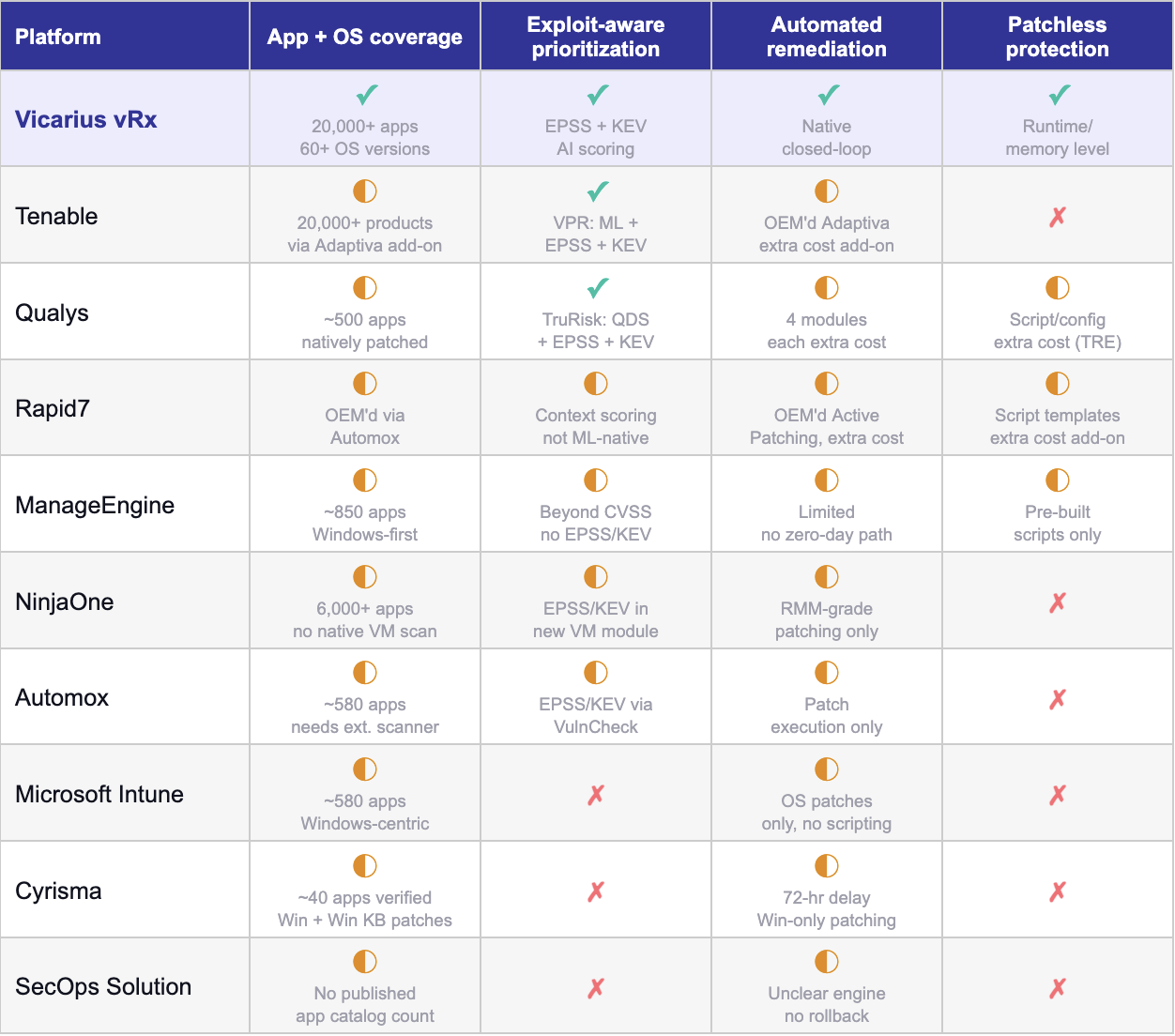
A criteria-led comparison of app and OS coverage, exploit-aware prioritization, automated remediation, and patchless protection.
Key takeaways
- Most vulnerability management platforms find vulnerabilities. Few fix them. Consolidated platforms close the loop in one workflow.
- Four criteria separate remediation platforms from scanners: native app and OS coverage, exploit-aware prioritization, automated patching, and patchless protection for zero-days.
- Mid-market teams need all four in one product. Module-based enterprise tools require 2 to 4 separate purchases to match what a unified platform does natively.
What is a vulnerability management platform?
A vulnerability management platform is a security tool that identifies, prioritizes, and remediates software vulnerabilities across an organization's endpoints, operating systems, and applications. Modern platforms go beyond scanning to include risk-based prioritization, automated patch deployment, and compensating controls for vulnerabilities that cannot be patched immediately.
The category sits at the intersection of IT operations and security operations. Older tools treated these as separate workflows: scan with one product, patch with another, report with a third. Consolidated platforms collapse that into a single agent, a single console, and a single remediation workflow.
For mid-market security and IT teams without a large headcount, consolidation is not just a convenience. It is the difference between a 1-hour MTTR and a 9-hour one.
Why security and IT teams need a consolidated platform
The vulnerability management market has a sprawl problem. Enterprise platforms like Tenable and Qualys were built for organizations with dedicated security teams who can manage multiple modules, integrate separate patching tools, and manually triage thousands of alerts. Mid-market companies rarely have that luxury.
The result is a predictable pattern: teams buy a scanner, get a list of CVEs, and spend more time figuring out how to patch them than fixing anything. The scanner found 2,000 vulnerabilities. The team has capacity to close 40 a week. The backlog grows faster than it shrinks.
A consolidated platform changes that equation by automating the steps between detection and closure. The right platform covers 20,000+ applications natively, ranks findings by real-world exploitability rather than CVSS severity scores, deploys patches without manual approval chains, and protects systems the moment a zero-day drops, before any vendor patch exists.
What to look for: 4 criteria that separate platforms from scanners
Before reviewing any vendor, understand what the four criteria measure and why each matters. Note especially the distinction in patchless protection: script-based mitigations (config changes, port blocks) reduce risk but leave the vulnerability present. Runtime/memory-level protection eliminates exploitation entirely.

How we scored each platform
Each platform is rated across the four criteria. Partial scores show a short explainer directly below the symbol so you know exactly what the limitation is.

Platform comparison at a glance
1. Vicarius vRx
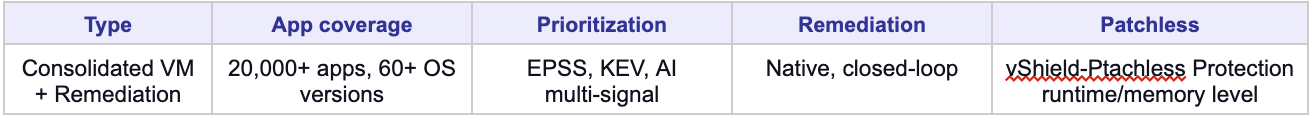
vRx is built around one argument: detection without remediation is just a longer to-do list. Where most platforms in this list stop at scanning or require add-on modules for patching, vRx closes the loop natively. Continuous scanning, exploit-aware prioritization using EPSS and KEV signals, automated patching across 20,000+ applications across 60+ OS versions, and patchless protection (vShield) that operates at the memory and runtime level, deploying within minutes when no vendor patch exists.
Coverage spans 60+ flavors of Windows, macOS, and Linux without meaningful degradation across OS types. Average MTTR for a critical vulnerability across 100 devices runs 1 to 2 hours with 1 to 2 FTEs, compared to 7 to 12 hours and 5 to 8 FTEs for legacy scanner platforms. There are no OEM'd components: the patching engine, the prioritization logic, and the patchless protection layer are all built and maintained natively.
The patchless protection distinction matters. vShield operates at the memory and process level, blocking exploitation attempts against a vulnerable application without modifying the application itself and without waiting for a configuration change to propagate. When a zero-day drops, vRx protects affected systems in minutes. That is meaningfully different from script-based mitigations that disable a service or block a port.
For mid-market teams that cannot staff a six-person remediation operation or afford the module sprawl of enterprise platforms, vRx delivers detection, prioritization, patching, and zero-day protection in a single product with three remediation paths: automated patching for 20,000+ apps, patchless protection for zero-days, and a scripting engine for custom fixes.
2. Tenable
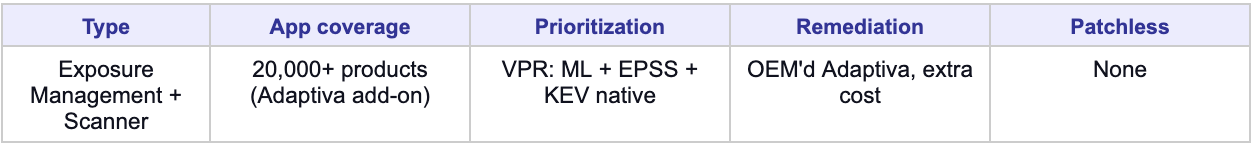
Tenable's App + OS coverage number needs context. The 20,000+ products figure comes from Tenable Patch Management, which is powered by Adaptiva, a separate company whose patch catalog and P2P content distribution engine Tenable licenses and surfaces as a paid add-on module. Tenable's native scanning platform does not carry that catalog: it is available only to customers who purchase the Patch Management add-on on top of Tenable One or Vulnerability Management. The covered OS list includes Windows (plus BIOS, drivers, Dell/HP/Lenovo hardware), macOS Ventura through Tahoe (third-party app patching only, no OS patching on Mac), and Linux: RHEL, Oracle, Alma, Rocky (versions 8/9/10), Debian (11/12/13), and CentOS Stream (9/10).
That caveat aside, Tenable Patch Management is genuinely broad once deployed. And Tenable's Vulnerability Priority Rating (VPR) is a proprietary ML-based scoring system that incorporates EPSS, CISA KEV, threat intelligence, and exploit prediction data. It is not just CVSS. VPR has been shown to reduce the remediation workload from ~160,000 CVEs (CVSS-based) to ~4,000 (VPR-based) while maintaining strong exploit coverage. That is real prioritization strength.
The structural gaps remain. Patching is a separate paid add-on on Adaptiva's tech stack, not Tenable's. No patchless protection exists on any Tenable tier. When a zero-day drops and no vendor patch exists, Tenable identifies affected assets and prioritizes risk. It cannot shield those assets.
3. Qualys

Qualys has two genuine strengths. Its TruRisk prioritization combines Qualys Detection Score (QDS), EPSS, and CISA KEV data into a strong, exploit-aware scoring system. And TruRisk Mitigate, part of the TruRisk Eliminate bundle launched in September 2024, does provide protection when no patch exists.
However, TruRisk Mitigate is script and configuration-based mitigation: it disables services, blocks ports, modifies registry keys, and applies configuration changes based on CISA and vendor recommendations. The vulnerability remains present; its exploitability is reduced by removing or restricting the attack surface. Vicarius vShield operates at the memory level, blocking the exploit itself. Both reduce risk; only one eliminates the exposure window.
The module sprawl is the bigger practical problem for mid-market teams. Full remediation requires VMDR, Patch Management, TruRisk Eliminate, and CAR, each priced separately. Native third-party app patching covers around 500 apps. Qualys launched Agent Val in March 2026 as agentic AI for remediation, but it requires all four modules to function: four products to close one vulnerability.
4. Rapid7

Rapid7 launched Active Patching in July 2025, powered by Automox, as a paid add-on to Exposure Command. The announcement specifically mentions 'virtual patching templates for systems without fixes,' which is a form of script-based workaround when no patch exists. Worth acknowledging as a partial capability, though like Qualys's TruRisk Mitigate it is configuration and script-based rather than runtime protection.
The core structural issues remain: Active Patching is OEM'd from Automox. Rapid7 does not own the patching engine, roadmap, or release cycle. InsightVM's prioritization uses contextual scoring but relies more on integrations and manual setup than Tenable's native VPR or Qualys's TruRisk. Rapid7's acquisition of Kenzo Security in 2026 signals continued pivot toward MDR, with VM as a declining roadmap priority.
For mid-market teams the practical reality is a fragmented stack: InsightVM for scanning, Exposure Command for correlation, Active Patching for remediation, each separately priced and managed.
5. ManageEngine
ManageEngine Vulnerability Manager Plus goes beyond pure CVSS scoring. It factors in exploitability, patch availability, age, and asset context to prioritize vulnerabilities. That is meaningfully better than raw CVSS. However, it does not natively integrate EPSS scores or CISA KEV data the way Tenable VPR, Qualys TruRisk, or Vicarius vRx do.
On zero-day mitigation, Vulnerability Manager Plus has a dedicated feature that deploys pre-built scripts as workarounds before patches arrive, including disabling vulnerable services and modifying configurations. Real capability, but script-based only, not runtime protection.
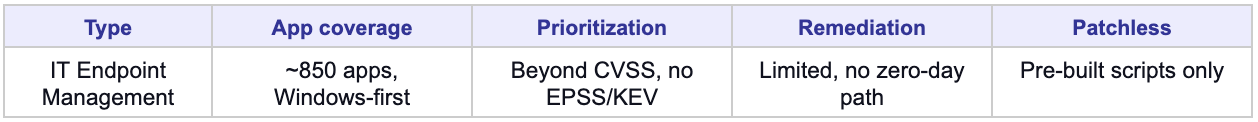
ManageEngine is fundamentally an IT operations platform. It patches Windows well, has solid coverage at ~850 apps, and serves its 180,000 customers effectively for basic endpoint management. Security teams with sophisticated exploit-detection and zero-day requirements will hit limits quickly.
6. NinjaOne

NinjaOne launched its Vulnerability Management module in March 2026, and the new product is more capable than its previous patch-only offering. It uses AI-driven real-time vulnerability assessment and includes EPSS and KEV data for prioritization, a genuine upgrade. NinjaOne also became a 2026 Gartner Magic Quadrant Leader in Endpoint Management, reflecting real market credibility.
The limitations are structural. The VM module is first-generation with no patchless protection. NinjaOne has a zero-day mitigation documentation page, but it provides guidance rather than a deployed protective control. NinjaOne also lacks a native vulnerability scanning engine: the VM module correlates endpoint telemetry with CVE intelligence from external sources rather than running its own agent-based scans.
For IT operations and MSP workflows, NinjaOne is excellent. For security-first vulnerability management with zero-day coverage, the platform was not built for that job.
7. Automox

Automox added EPSS and KEV prioritization via a VulnCheck integration, a real improvement over pure CVSS scoring. It does cloud-native patch deployment well, runs without on-premise infrastructure, and covers Windows, macOS, and Linux across around 580 third-party applications.
The fundamental limitation is that Automox is a patch execution platform, not a vulnerability management platform. It does not do full CVE-level vulnerability assessment natively: you need an external scanner to feed it discovery data via its Vulnerability Sync feature. You are paying for two vendors to do what a unified platform does with one. There is also no patchless protection when no patch exists.
8. Microsoft Intune

Intune's reach is enormous: 500 million devices, 250,000 organizations, mostly bundled into Microsoft 365 E3 and E5 licenses. For Windows-first environments with Azure investment, it handles MDM and OS-level patching reasonably well.
The security gap is significant. Intune has no native exploit-aware prioritization: no EPSS, no KEV integration, no ML-based risk scoring. Remediation for anything beyond standard OS updates requires manual scripting or API work. Third-party app coverage sits at around 580 applications. Linux support is weak. There is no patchless protection on any tier.
The full Microsoft remediation stack (Intune plus Defender plus Azure infrastructure) runs $300,000 to $350,000 per year for 1,000 endpoints, for a platform that cannot autonomously deploy a patch when a zero-day hits.
9. Cyrisma

Cyrisma targets MSPs and SMBs with a consolidated platform bundling vulnerability scanning, data discovery, and compliance reporting. For small teams needing basic visibility and low-friction deployment, it serves a real need.
The app coverage figure requires context. Cyrisma's own published patchable applications list (from their help documentation) contains approximately 40 named third-party applications across categories including browsers, compression tools, remote tools, communication tools, and development tools. All are Windows-based. Cyrisma added Windows KB (OS patch) deployment in February 2025, which broadens OS patching but does not change the third-party app count.
The platform uses CVSS scoring only with no EPSS or KEV integration. Auto-patching carries a 72-hour delay. No patchless protection exists on any tier. Sensor communication requires cloud connectivity, creating blind spots in constrained networks.
10. SecOps Solution

SecOps Solution is a small vendor (roughly six employees, approximately $660,000 ARR as of 2025, roughly 50 customers) marketing itself as an all-in-one agentless scanner and patcher for SMBs and MSSPs. The appeal is simplicity, fast deployment, and price point.
The platform supports Windows, macOS, and Linux scanning plus third-party application patching. However, SecOps does not publish a numbered app catalog on their website or in any documentation. No independently verifiable app count is available, so no specific figure can be stated with confidence. Their Patch Astra tool provides individual patch lookup but does not indicate total catalog size.
Additional concerns: the patching engine has no public documentation on test-before-deploy procedures, staged rollouts, or rollback capabilities. Agentless scanning relies on WinRM and SSH, leaving offline, segmented, or credential-restricted endpoints blind. With only a handful of Gartner Peer Insights reviews, independent enterprise-scale validation is limited. There is no patchless protection.
How to evaluate which platform fits your environment
Before committing to any platform, run these four questions against each vendor in your shortlist.
What happens when a zero-day drops and no patch exists? If the answer is “wait for a vendor patch”, your exposure window could be weeks. Ask specifically whether the protection is runtime/memory-level or script-based. Both reduce risk. Only one eliminates the exposure window.
How many of your third-party applications are covered natively? Ask whether the app coverage figure is native to the platform or comes from a separately purchased OEM module. A platform covering 500 apps natively leaves thousands of endpoints with unmanaged software risk.
What is the MTTR benchmark for a critical CVE across 100 mixed-OS devices? This separates scanning tools from remediation platforms. Sub-2-hour MTTR requires native automation. Manual triage and patching workflows rarely get below 7 hours.
What does full deployment actually cost? Module-based pricing from enterprise vendors routinely runs 1.5 to 2.5x the headline license price once remediation, compliance, and OS support are included. Get a total cost of ownership number, not just a per-seat figure.
The good ol' days of quarterly scan cycles and manual patch tickets are gone. AI-assisted discovery is accelerating the pace at which vulnerabilities surface, and the teams that close them fastest are the ones that don't hand off between tools to do it.