Continuous Exposure Assessment and Validation
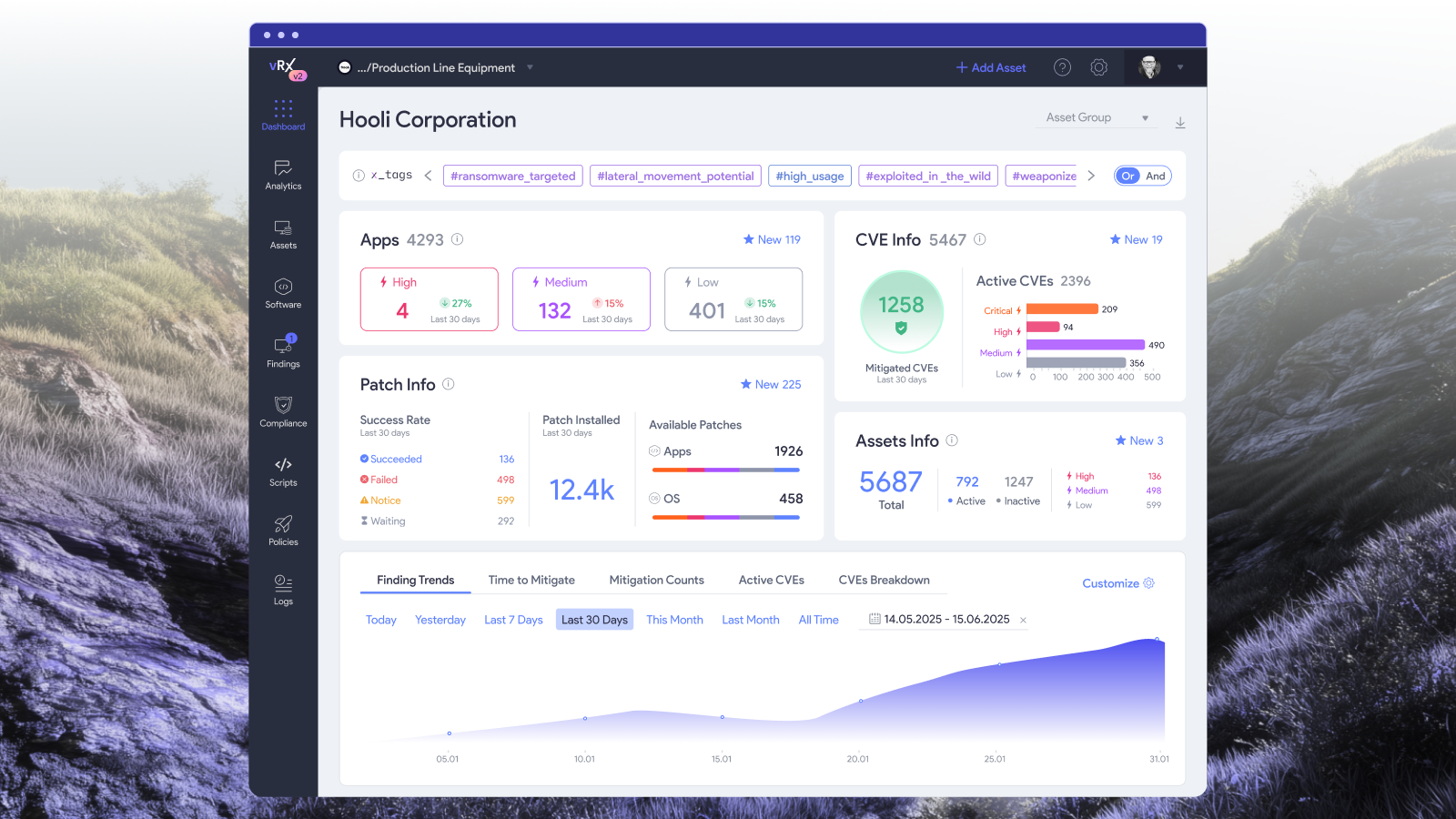
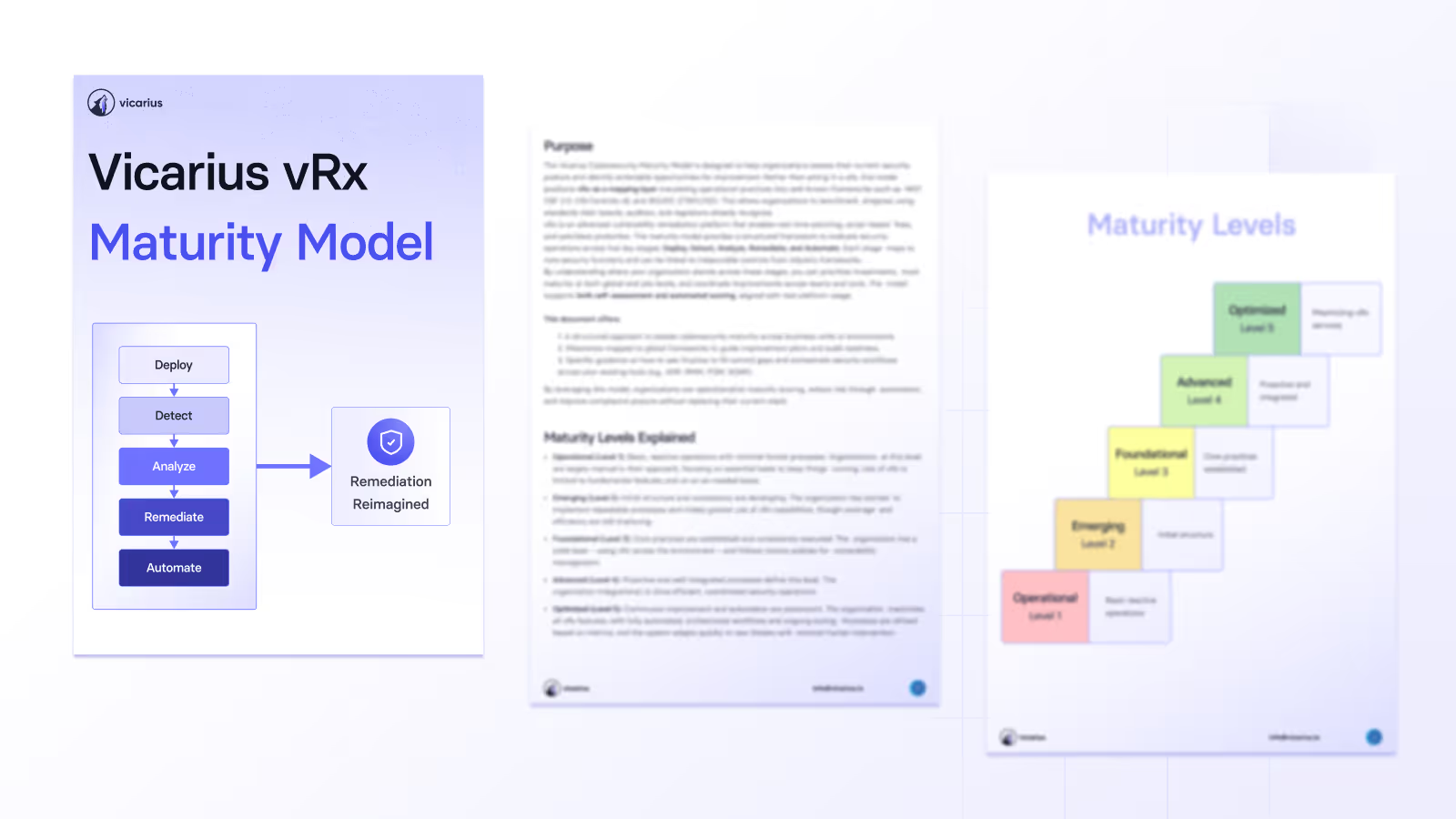
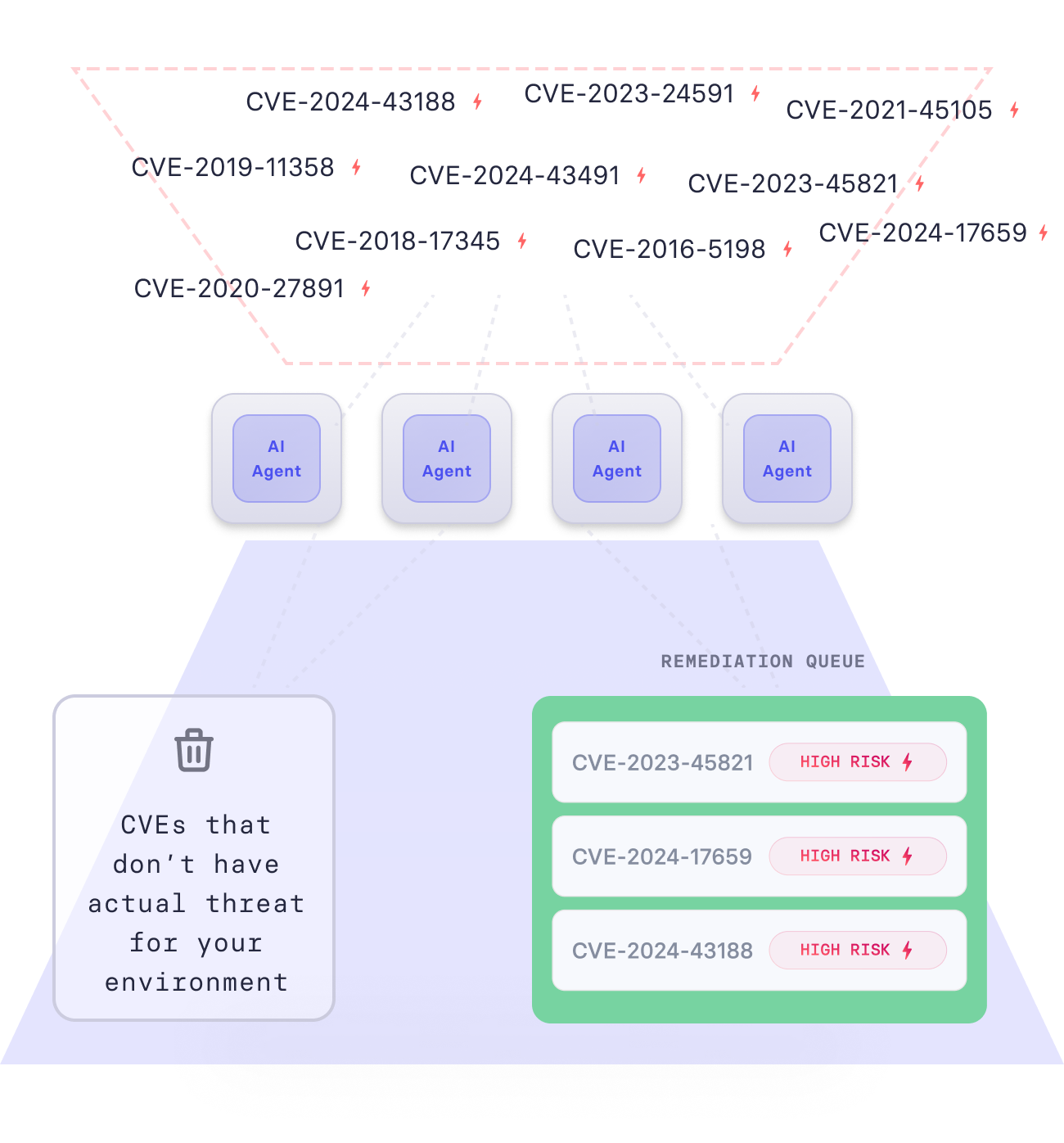
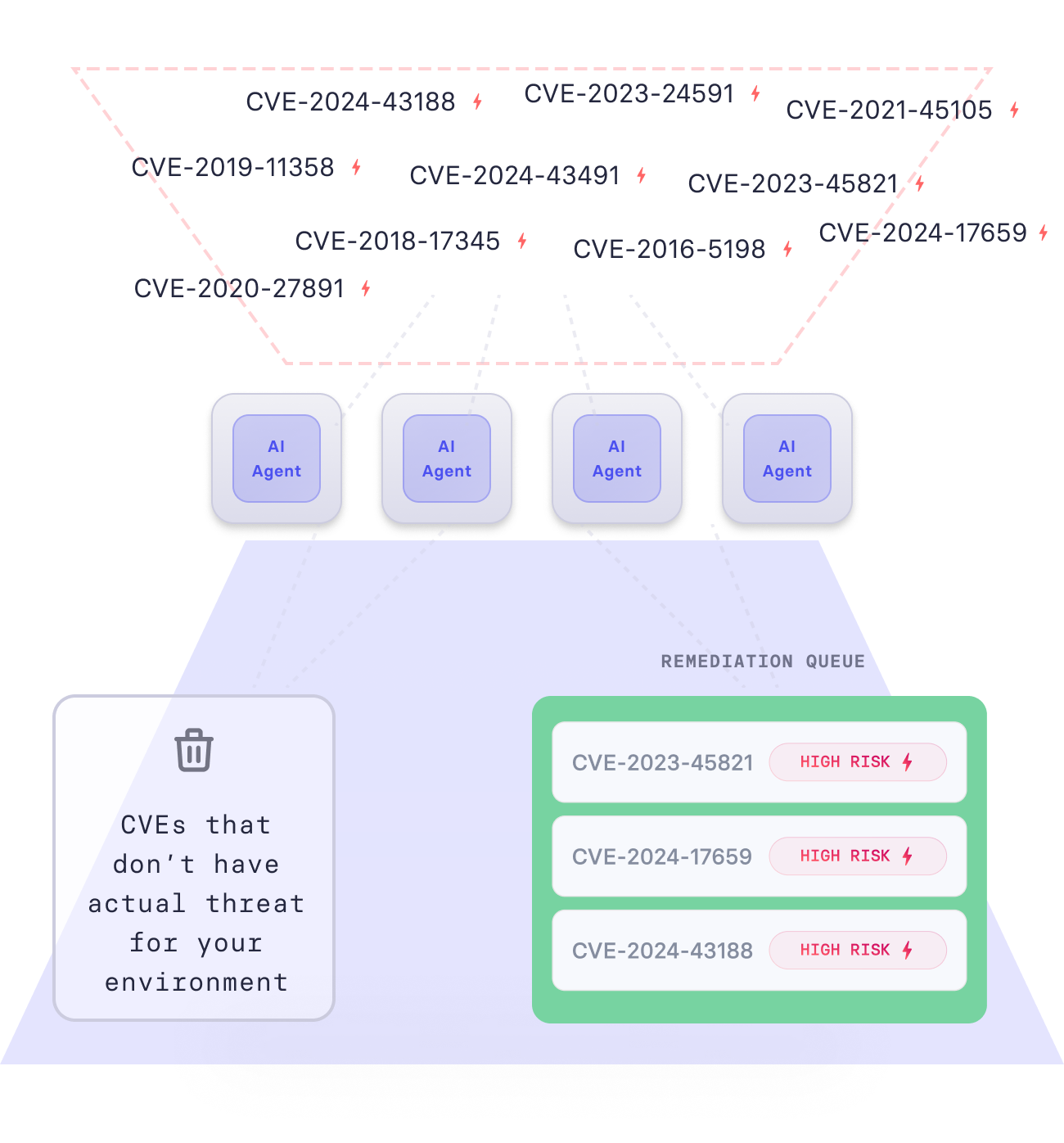
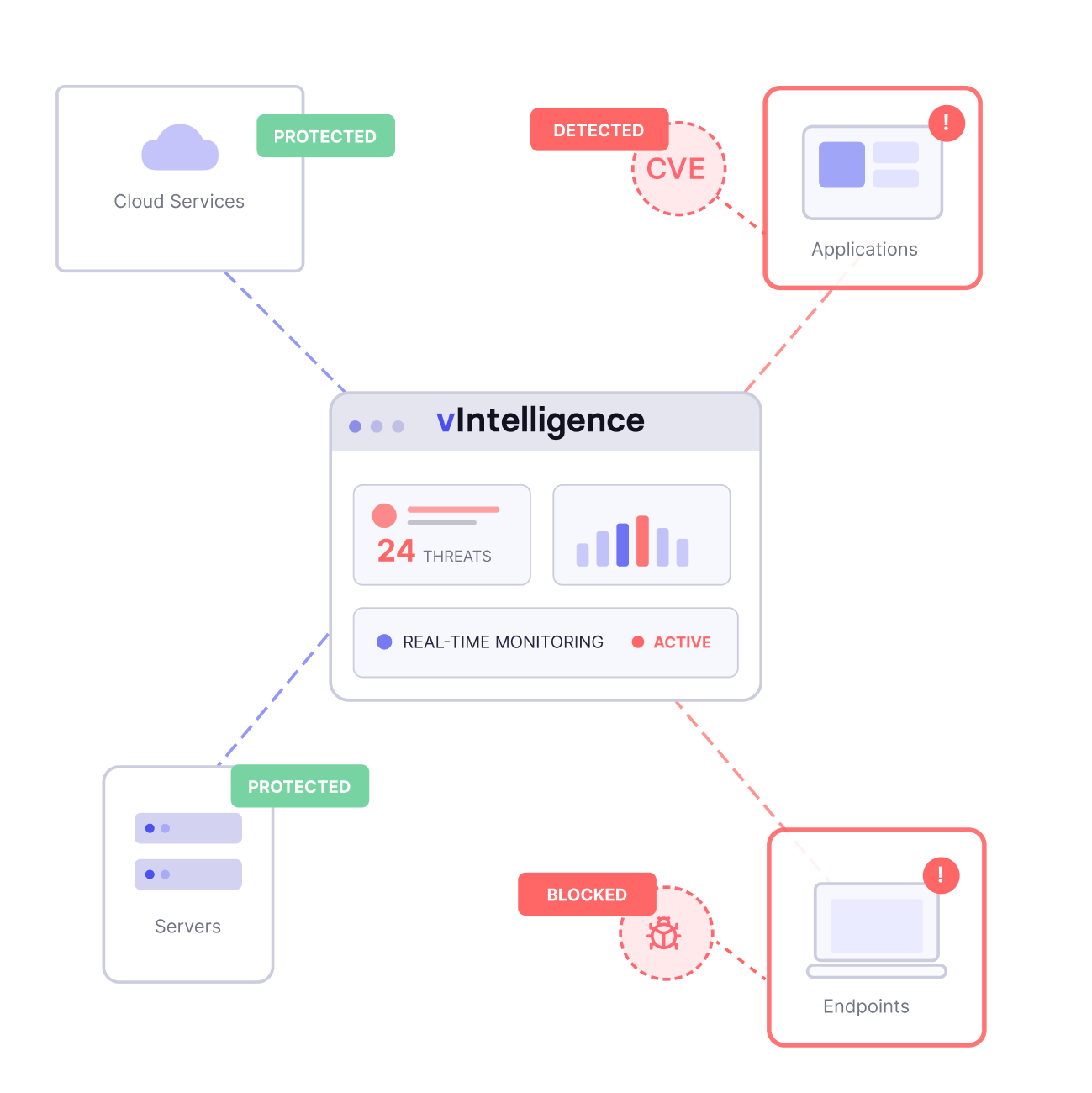
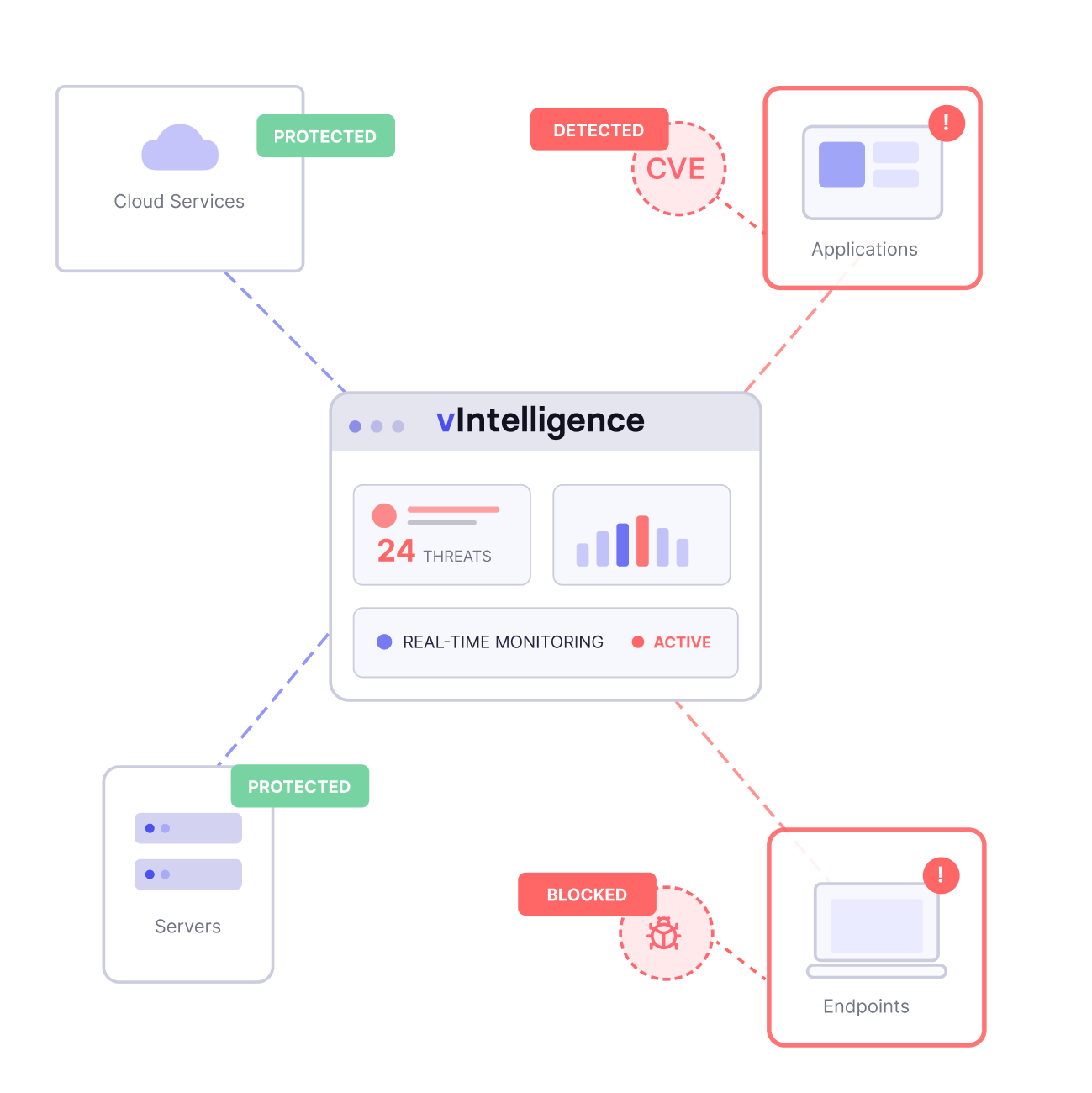
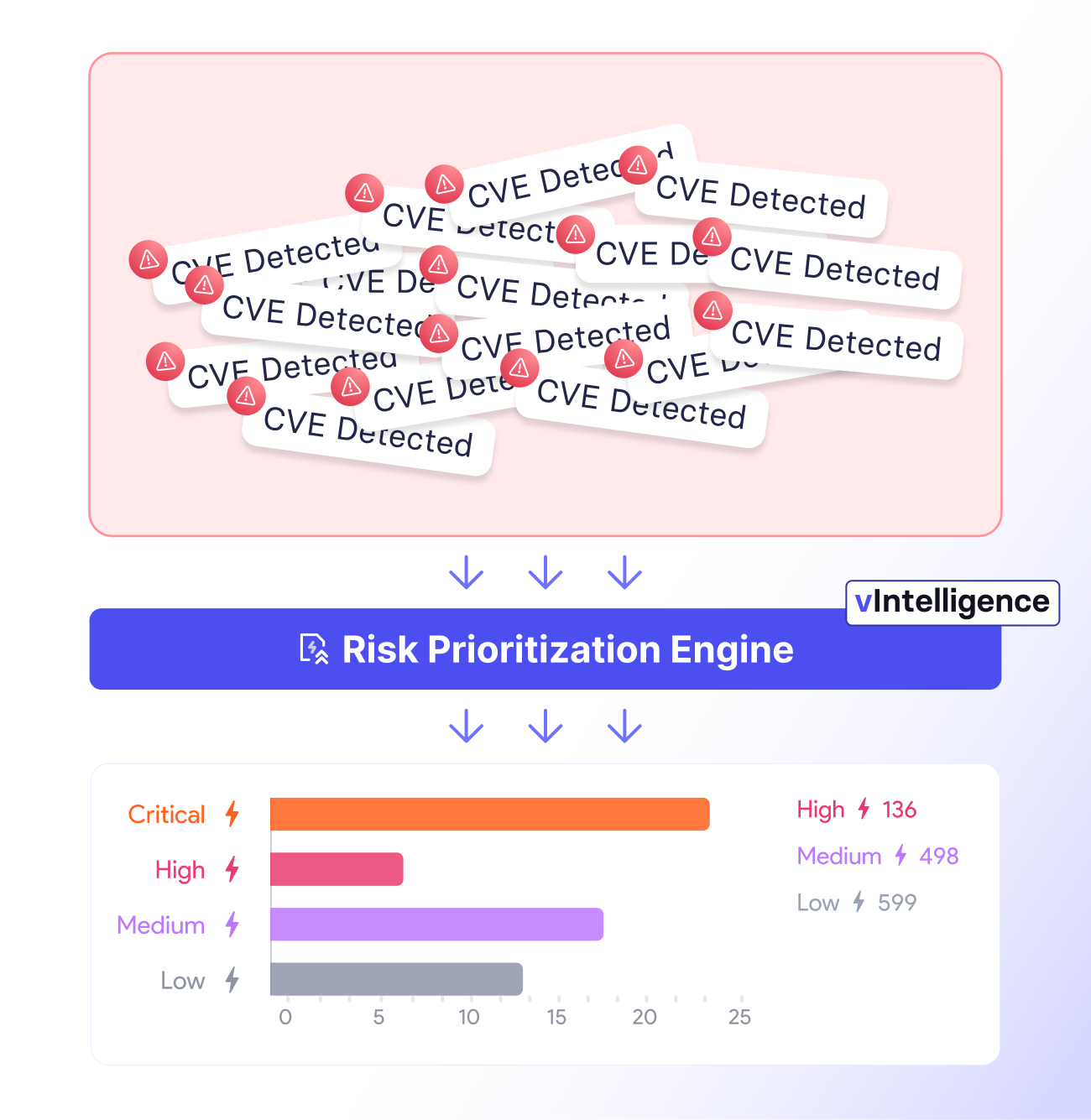
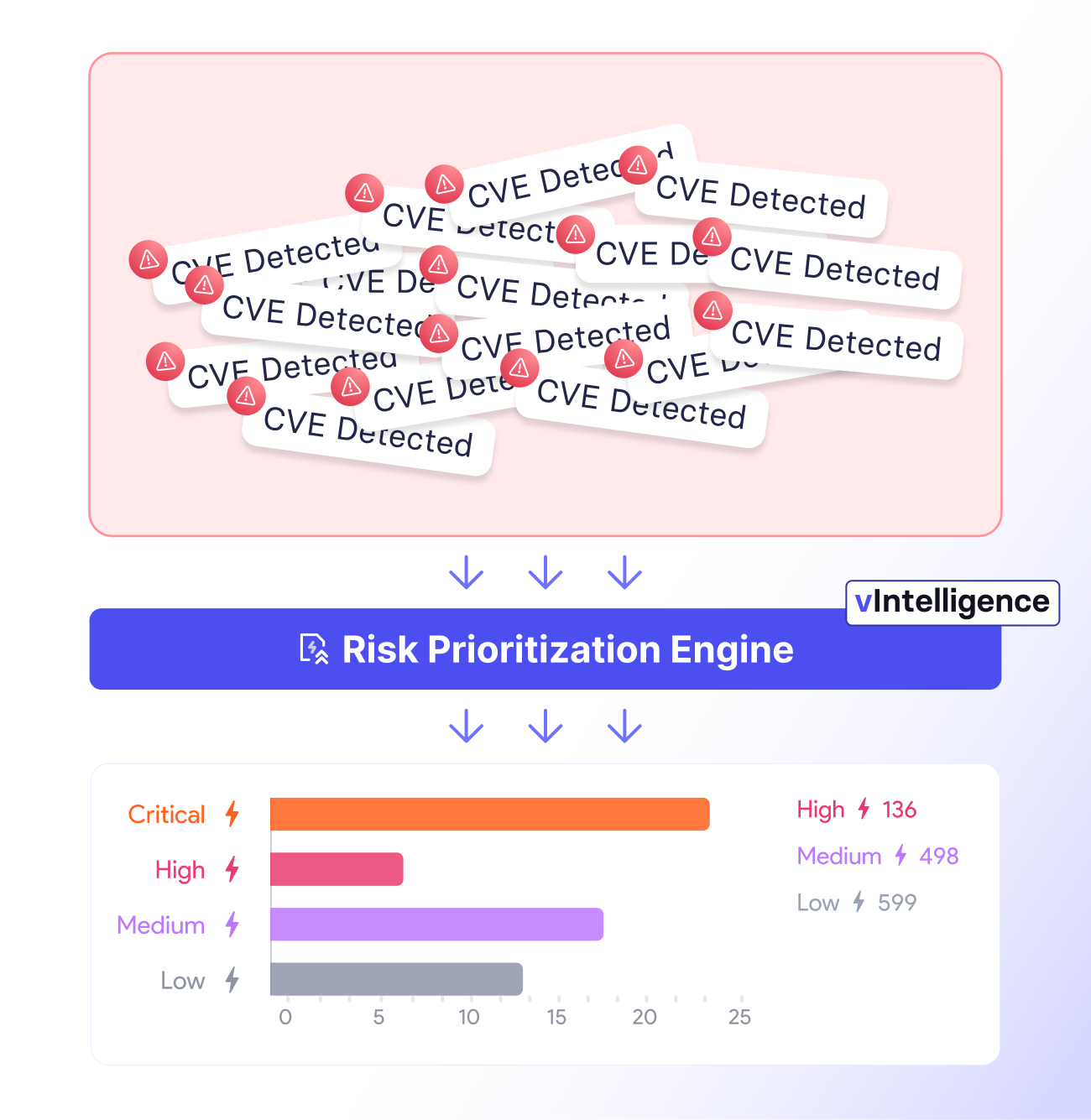
vIntelligence continuously ingests vulnerability data from every tool in your stack, eliminates false positives through AI-powered exploit validation, and delivers automated remediation with proof of closure, so your team fixes real risks fast, at enterprise scale.

New Vulnerabilities per day
CVE assignment gap
In savings by consolidating tools

























































































Give your security team the upper hand.
vIntelligence shifts your security posture from reactive to preemptive. Validate real risks, eliminate noise, and fix vulnerabilities before attackers ever get the chance to exploit them.
No more blind spots
Stop drowning in alerts
Test without breaking things
Close tickets with confidence
One truth, not ten dashboards
Prove it to the board




Features
In order to maintain a secure environment, Vicarius has achieved SOC II compliance without exceptions.






Everything you need to know

What is vIntelligence and how is it different from a vulnerability scanner?
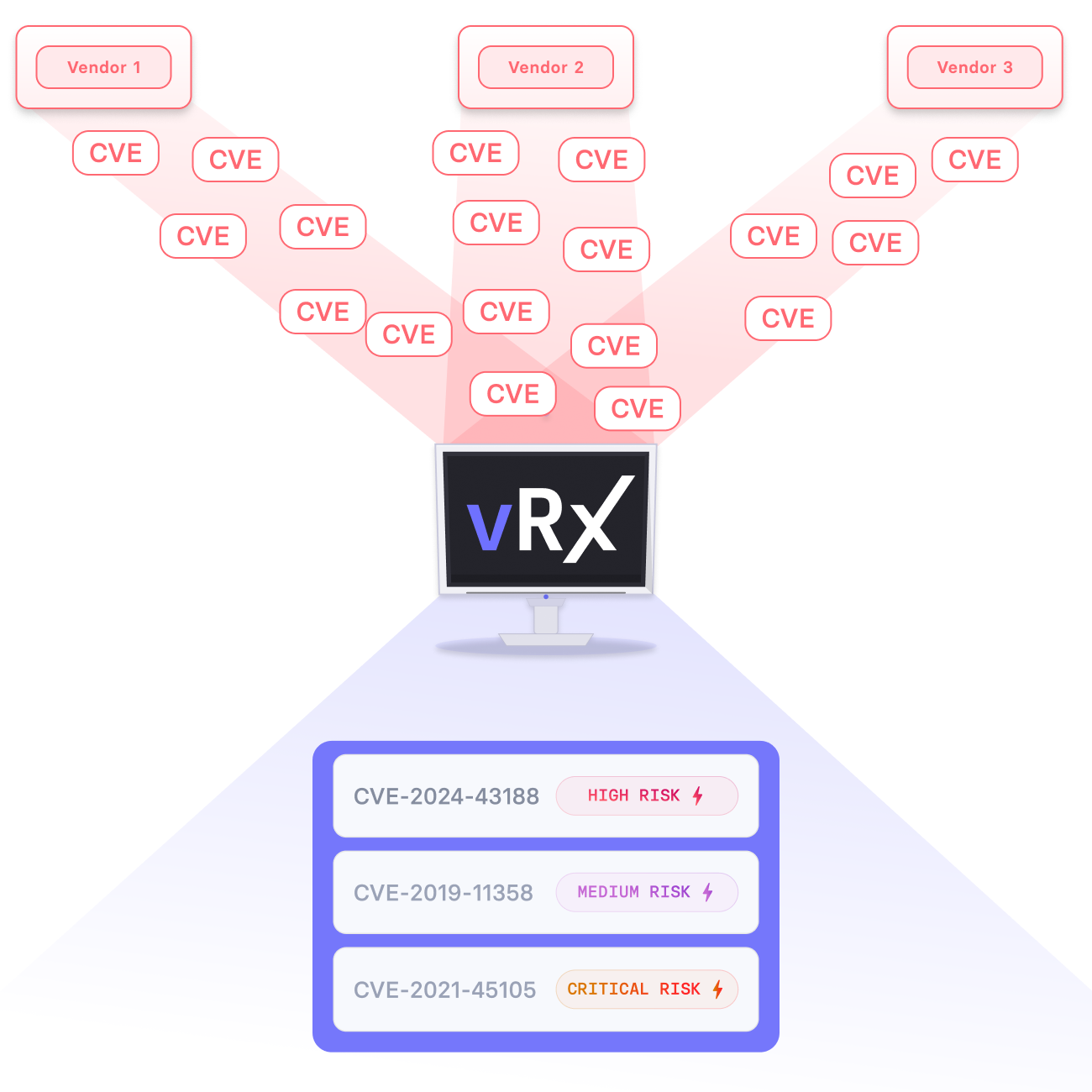
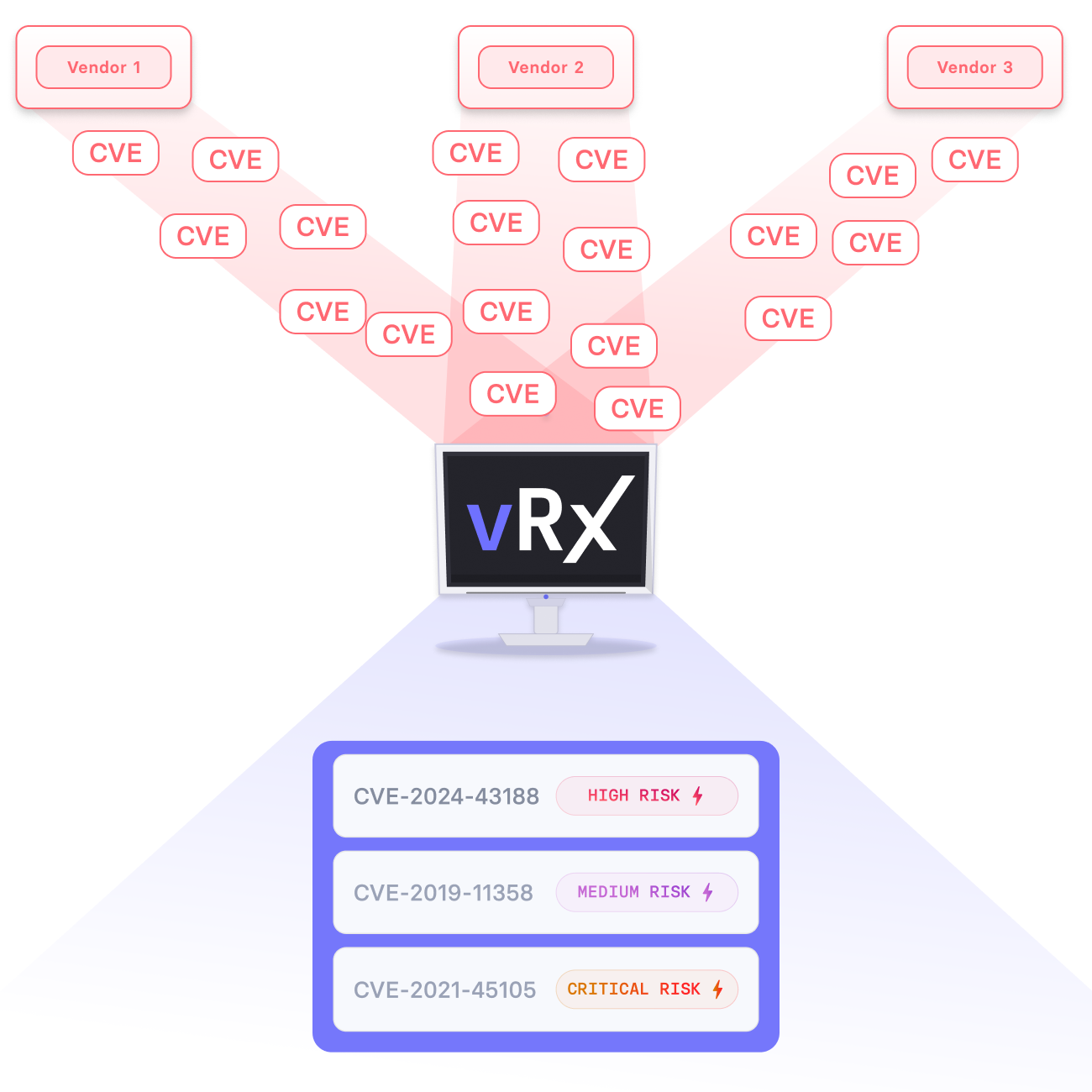
Traditional scanners find vulnerabilities periodically and stop there. vIntelligence continuously ingests data from all your existing security tools, validates which vulnerabilities are actually exploitable in your environment, and closes the loop with automated remediation, all in one platform.
Does vIntelligence replace my existing security tools?
No. vIntelligence connects to the tools you already have, CrowdStrike, Qualys, Tenable, and more, and makes them work together. You get one unified, accurate risk view without ripping anything out.
How does the AI Red Team work without disrupting production?
vIntelligence's AI agents generate and execute custom validation scripts that test exploitability safely inside your environment. The process is designed to produce zero production downtime while delivering real confirmation of whether a vulnerability can be exploited.
How does vIntelligence support compliance requirements?
Every remediation is re-validated and documented with auditable proof of closure. This gives your security and legal teams the evidence they need for SEC cybersecurity disclosures, NIS2, DORA, and cyber insurance requirements.
How quickly can we get started?
vIntelligence connects natively to your existing security stack with no complex deployment. Most teams are ingesting and normalizing data from their first vendor integrations within hours of setup.