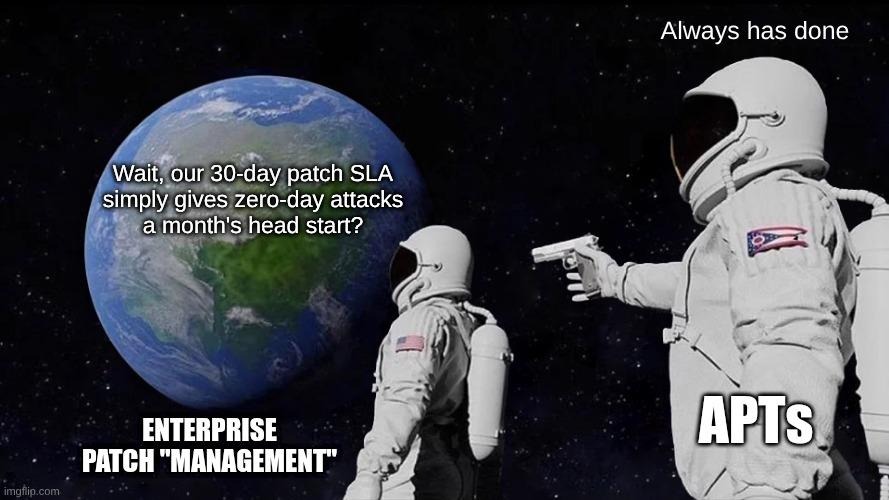
The traditional 30-day patch window has fundamentally collapsed, making the "monthly maintenance" mindset an immediate and critical liability. For decades, enterprise IT teams operated on a predictable rhythm, deploying security updates weeks after vendor release, assuming threat actors required substantial time to develop functional exploits. That era is over forever.
Today, maintaining a 30-day remediation cycle does not represent prudent risk management; it guarantees all-too-well-documented windows of exposure that sophisticated adversaries can easily exploit. This sobering reality underscores the need for a dramatic shift in cyber resilience, moving away from relying primarily on anti-phishing training towards active defense against software exploits.
This "structural gap" between disclosure and remediation has escalated into a strategic business risk demanding immediate resource and attention reallocation from the board on down. Organizations can no longer afford to treat patching as a background administrative task. Fixing vulnerabilities quickly is now the baseline for enterprise survival.
The new speed of exploitation
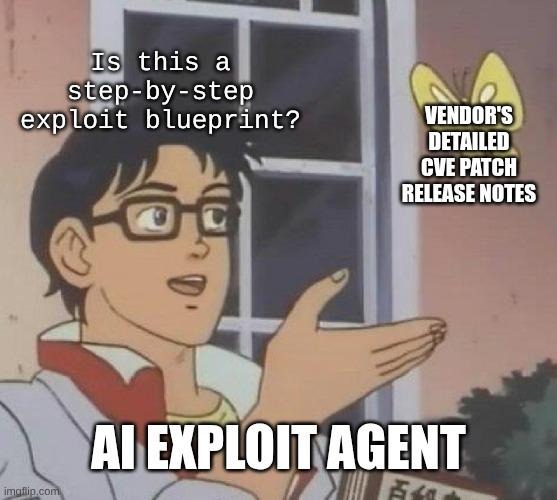
A profound technological shift has occurred: AI-driven automated patch-diffing has successfully reduced exploit development timelines from weeks down to a mere 24–48 hour window (if you’re lucky). As AI agents and large language models increasingly interact with software environments, the timeframe adversaries need to identify and act on code defects has compressed significantly. Traditional remediation schedules are clearly obsolete. When a software vendor releases a critical security update, automated tools can rapidly compare the newly patched code against the vulnerable version, automatically identifying the precise nature of the flaw. Academic research from the University of Illinois already demonstrated in 2024 that AI agents can autonomously build and execute working exploits for 87% of critical vulnerabilities in a matter of minutes, requiring nothing more than the public CVE description to guide their attacks.
For technical and non-technical stakeholders alike, understanding this "weaponization timeline" is critical: attackers are effectively using vendors’ own security fixes to reverse-engineer roadmaps for the intrusions to exploit them. By releasing a patch, vendors inadvertently publish the exact blueprints needed to compromise unpatched systems. Adversaries immediately feed this data into automated exploitation frameworks, drastically compressing the time organizations have to defend themselves before active attacks begin.
Furthermore, attackers have executed a strategic pivot toward targeting edge infrastructure such as VPNs, firewalls, and routers, as well as undocumented "shadow IT". These frequently forgotten assets routinely bypass standard enterprise patch management protocols, essentially offering low-friction unmonitored entry into the corporate network. Because these devices often lack traditional endpoint detection agents, compromises can remain undetected for months, making rapid remediation at the edge an absolute necessity.
The structural gap: Mechanics of the attack window
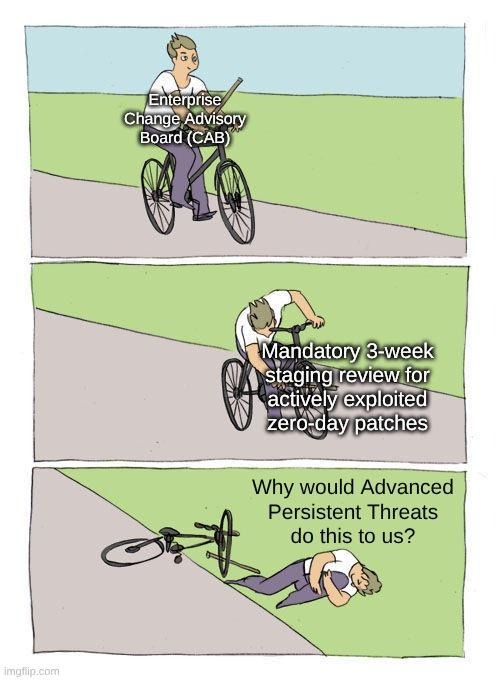
The structural gap here is the critical delay between a vendor's patch release and the actual enterprise deployment. This specific period of exposure has now become the primary entry point for global threat actors, a fact heavily supported by the stark recent shift where public-facing application exploits officially overtook phishing as the primary initial attack vector across global breaches. Threat actors recognize that enterprise bureaucracy is their greatest ally, intentionally targeting organizations trapped in lengthy change advisory board (CAB) review cycles.
Near-realtime exploitation
To clearly see this near-realtime exploitation cycle, one need look no further than the February 2026 surge of zero-days, where attackers leveraged six actively exploited zero-day vulnerabilities in a single Patch Tuesday cycle. Once a vulnerability is announced, malicious scanners immediately map the internet for vulnerable fingerprints. This highlights a severe resource and "asymmetry" problem: an attacker only needs to succeed once via an automated script, while security teams must successfully patch thousands of diverse assets without breaking operations.
The stability vs. security paradox
To close this gap, engineering teams must address the "Stability vs. Security" paradox directly. The deep-seated fear of "breaking the environment" with a fast patch of uncertain riskiness often predictably creates far larger, more expensive, and crucially intrusive business risk than a potential temporary system outage caused by the patch itself; temporary downtime is still merely downtime, whereas the ramifications of a bad intrusion event can ruin both companies and lives.
Deployment illusions
Further complicating this dynamic is the danger of "deployment illusions" and silent patching failures. Attackers actively hunt for and capitalize on specific systems that enterprise IT dashboards had already falsely reported as securely updated. Teams cannot assume a vulnerability is remediated simply because a mass-deployment tool fired a command; actual verification is essential.
Key mechanical failures that widen the attack window:
- Missing asset visibility: Unmonitored edge devices remain permanently vulnerable because security teams cannot patch what they cannot see.
- Bureaucratic testing cycles: Mandatory multi-week testing phases ensure that exploits are weaponized long before patches are approved for production.
- Flawed reporting mechanisms: Dashboard deployment illusions leave critical systems exposed while providing executives with a false sense of security.
Strategic and legal considerations
The compliance and regulatory landscape is rapidly evolving, fundamentally changing how both executive leadership and hands-on security teams must operate. The legal concept of "reasonable security" is being explicitly redefined by regulators to require a rapid response to known critical vulnerabilities, with federal agencies like CISA establishing aggressive remediation timelines for known exploited flaws. Standard monthly patching cycles are no longer accepted as an adequate defense for highly critical infrastructure. While executive leadership faces direct legal accountability if an organization falls victim to a well-documented vulnerability, the intense operational pressure to prevent this falls squarely on the security and engineering teams tasked with executing these accelerated timelines.
Key operational ramifications for security teams:
- This shift directly impacts organizational risk transfer strategies, particularly concerning cyber insurance premiums and claims. A documented 30-day lag in patching critical bugs is increasingly viewed as gross negligence by underwriters in the event of a breach, potentially voiding coverage entirely. Insurers are actively tightening underwriting standards, meaning security teams are now routinely required to provide concrete telemetry and proof of high-velocity vulnerability remediation capabilities before policies are issued or renewed.
- Moreover, security operations and architecture teams must assess the extended risk of third-party vendor integrations and supply chain vulnerabilities. A rigorous internal 24-hour patch cycle is rendered completely useless if a trusted, deeply integrated partner operates on a legacy 30-day window. Organizations must actively audit the remediation timelines of their critical vendors to ensure security teams are not inheriting unacceptable levels of risk through trusted API connections and network tunnels.
- Finally, there are severe brand reputation and operational risks associated with "preventable" breaches caused by N-day vulnerabilities. For security professionals, there is nothing more frustrating than an incident where the fix was publicly available, but internal CAB delays or organizational bureaucracy prevented it from being applied in time. The public and the market are highly unforgiving of organizations that suffer massive data loss simply because they failed to install a known update, making it critical that security teams are empowered to bypass legacy roadblocks for emergency fixes.
Focusing on active exploitability
To combat modern threats, engineering teams must develop a strategic prioritization framework that moves away from attempting to "patch everything equally". Instead, they must adopt a risk-based model focused strictly on "Active Exploitability" and "Business Criticality". Not all vulnerabilities require immediate action, but those actively exploited in the wild must be remediated without delay.
Emergency patch lanes
To modernize operations, teams must upgrade their CI/CD pipelines to support "emergency" patch lanes. These lanes are designed to safely bypass standard non-critical testing cycles specifically for high-threat vulnerabilities.
Continuous validation
Furthermore, organizations must formulate a strategy for continuous validation and automated post-patch scanning. Executives must understand that applying a fix is meaningless unless there is a concrete mechanism to verify that the exploit pathway has actually been eliminated across the entire environment.
Core remediation initiatives
- Remediation-first architecture: Ensure that vulnerability management programs prioritize actual fixing over endless scanning, recognizing that knowing about a problem is not enough.
- Integrated ecosystem leveraging: Adopt a "Better Together" initiative that enables seamless integration with existing systems, allowing you to remediate vulnerabilities regardless of where they were detected.
- Emergency deployment lanes: Configure CI/CD pipelines to allow critical security updates to bypass standard, time-consuming testing phases.
Vulnerability remediation with vRx
Achieving this requires investing heavily in automated patch orchestration and "virtual patching" (such as WAF or IPS rules) as a critical stop-gap measure. This buys valuable time for full deployment without leaving the network door wide open. This is where vRx by Vicarius provides substantial, measurable value. vRx is purpose-built to lead in vulnerability remediation. While many platforms focus heavily on detection or prioritization, vRx addresses the most critical part of the vulnerability lifecycle: remediation. By combining proprietary, automation-first technology for remediation with extensive integrations that plug into existing detection tools, teams can move from awareness to action - from "now we know" to "now it's fixed" - more quickly and efficiently than ever before.
Operational velocity is the only effective defense against AI-accelerated exploitation
Maintaining a legacy 30-day patch window is equivalent to leaving the corporate network unguarded. Survival requires an immediate shift to a "Security-First" culture where rapid remediation is viewed not as an IT burden, but as a competitive business enabler. From executives on down, the ownership and management of any enterprise with plans to survive the coming flood of AI-boosted attacks must immediately and aggressively secure the buy-in needed to empower their engineering teams to dismantle bureaucratic roadblocks that are actively delaying critical deployments.
The tools to detect threats are abundant, but the capacity to fix them rapidly is what will ultimately secure the organization. Close the structural gap in your infrastructure by moving from continuous detection to automated, decisive resolution. Book a demo of vRx today to see high-velocity patching in action and secure your network against modern exploit timelines.