Security teams today face a paradox. They have more tools than ever scanners, SIEMs, endpoint agents, cloud monitors yet they feel less in control than ever. Alerts pile up faster than teams can triage them. Vulnerabilities that get flagged on Monday may sit unpatched for weeks while analysts wade through thousands of false positives. Meanwhile, attackers exploiting AI tools can weaponize a newly disclosed vulnerability in hours, not months.
This is the gap that vIntelligence was built to close.
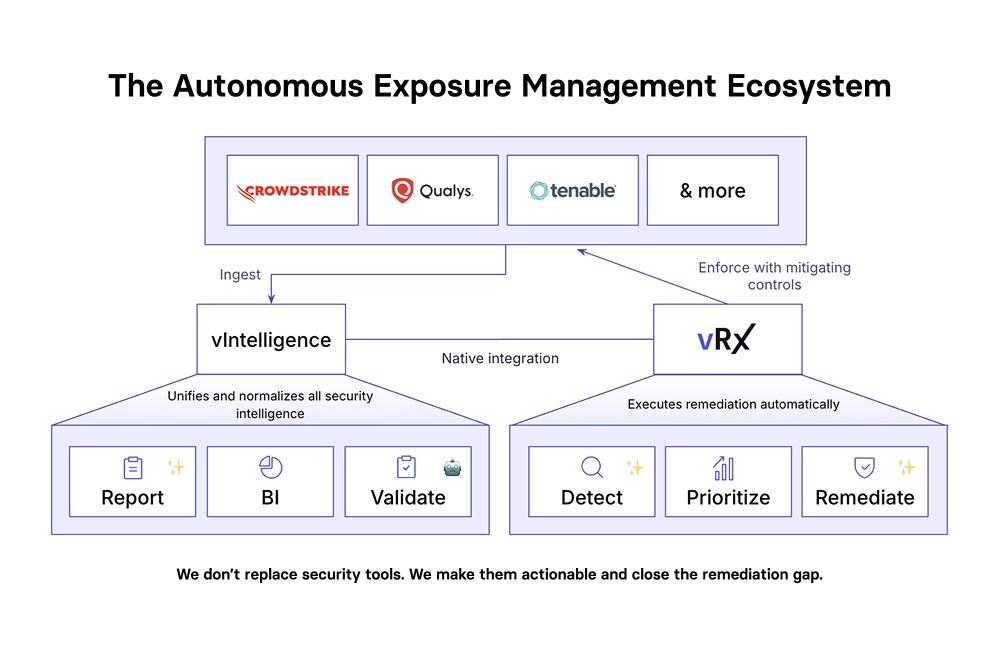
Vicarius, the company behind vRx a platform used by security teams worldwide to remediate vulnerabilities at scale has launched vIntelligence, a next-generation intelligence and validation layer that continuously ingests, normalizes, validates, and prioritizes vulnerability data across the entire enterprise security stack. Together, vRx and vIntelligence form a closed-loop exposure management platform: from detection to validated fix, with proof of closure at every step.
The Problem: Traditional Vulnerability Management is Broken
Before understanding why vIntelligence matters, it helps to understand what's broken with the status quo. Most enterprises today operate a fragmented security stack: a vulnerability scanner here, an endpoint detection tool there, a cloud security posture manager somewhere else. Each of these tools produces its own data, its own severity scores, its own alert queue and none of them talk to each other in a meaningful way.
The result is four compounding crises that security leaders recognize immediately:
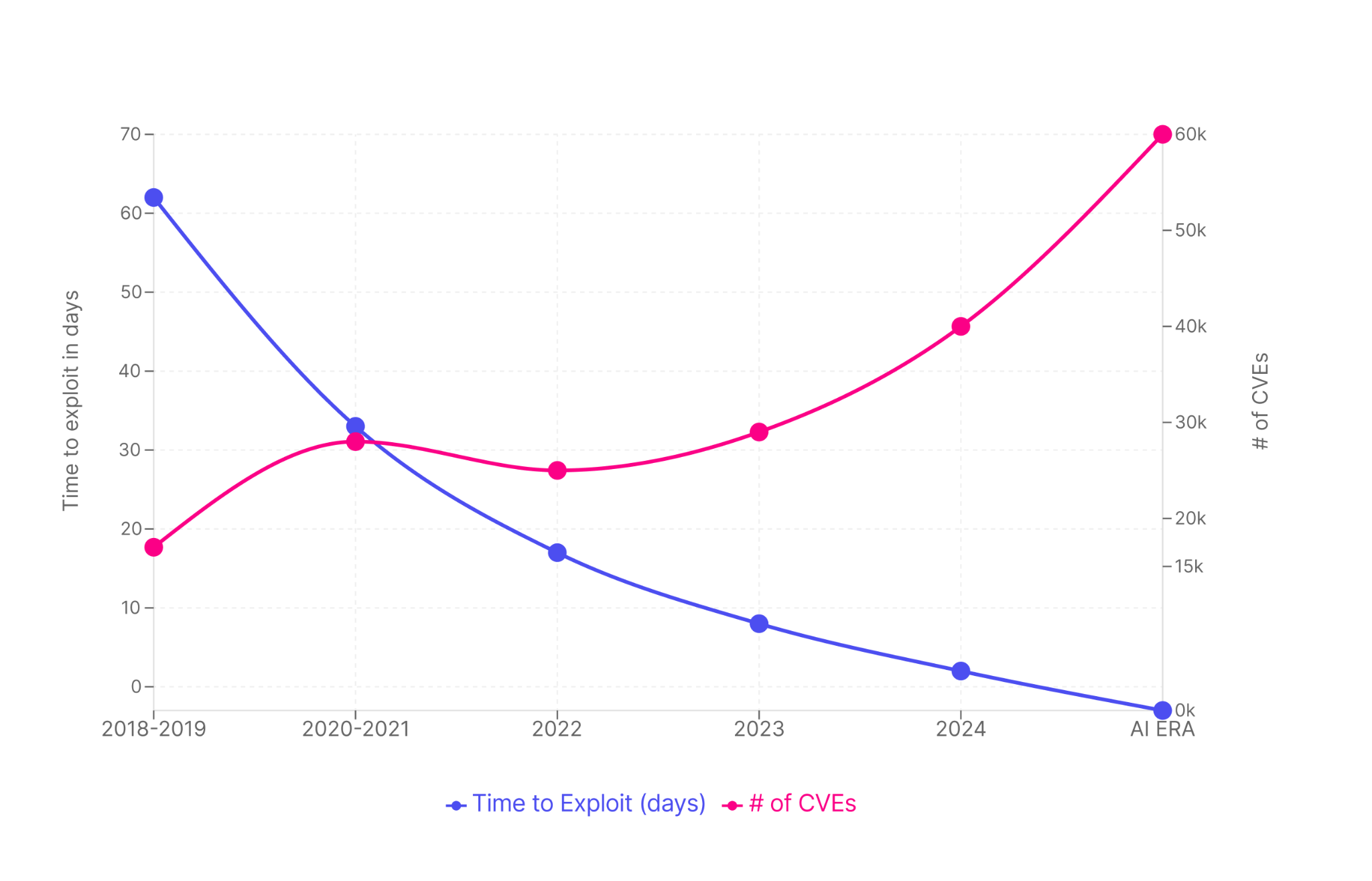
- Speed Crisis: Vulnerabilities are now exploited within hours or even minutes of disclosure, yet most organizations still scan monthly or quarterly. The window of exposure is enormous.
- Accuracy Crisis: Over 95% of vulnerability alerts are false positives. Teams spend enormous energy triaging noise instead of fixing real risks.
- Remediation Crisis: Most platforms stop at detection. There is no automated path from identifying a vulnerability to deploying a validated fix leaving 70% of security team time stuck in triage mode.
- Cost Crisis: The average data breach now costs $4.45 million, and 60% of breaches involve vulnerabilities that were known but unpatched. The financial stakes of slow or inaccurate remediation have never been higher.
What's compounding all of this is the AI-powered threat acceleration happening on the attacker side. What once required sophisticated nation-state resources automated exploit generation, rapid discovery of unpatched systems, rapid deployment of ransomware is now accessible to a much wider threat actor landscape. More than 130 new vulnerabilities are introduced every day, and critically, 80% of exploits are published before a CVE is even formally assigned. That means defenders are operating with a 23-day blind spot before official tracking even begins.
Time to Exploit: From Months to Minutes
Introducing vIntelligence: The Intelligence and Validation Layer
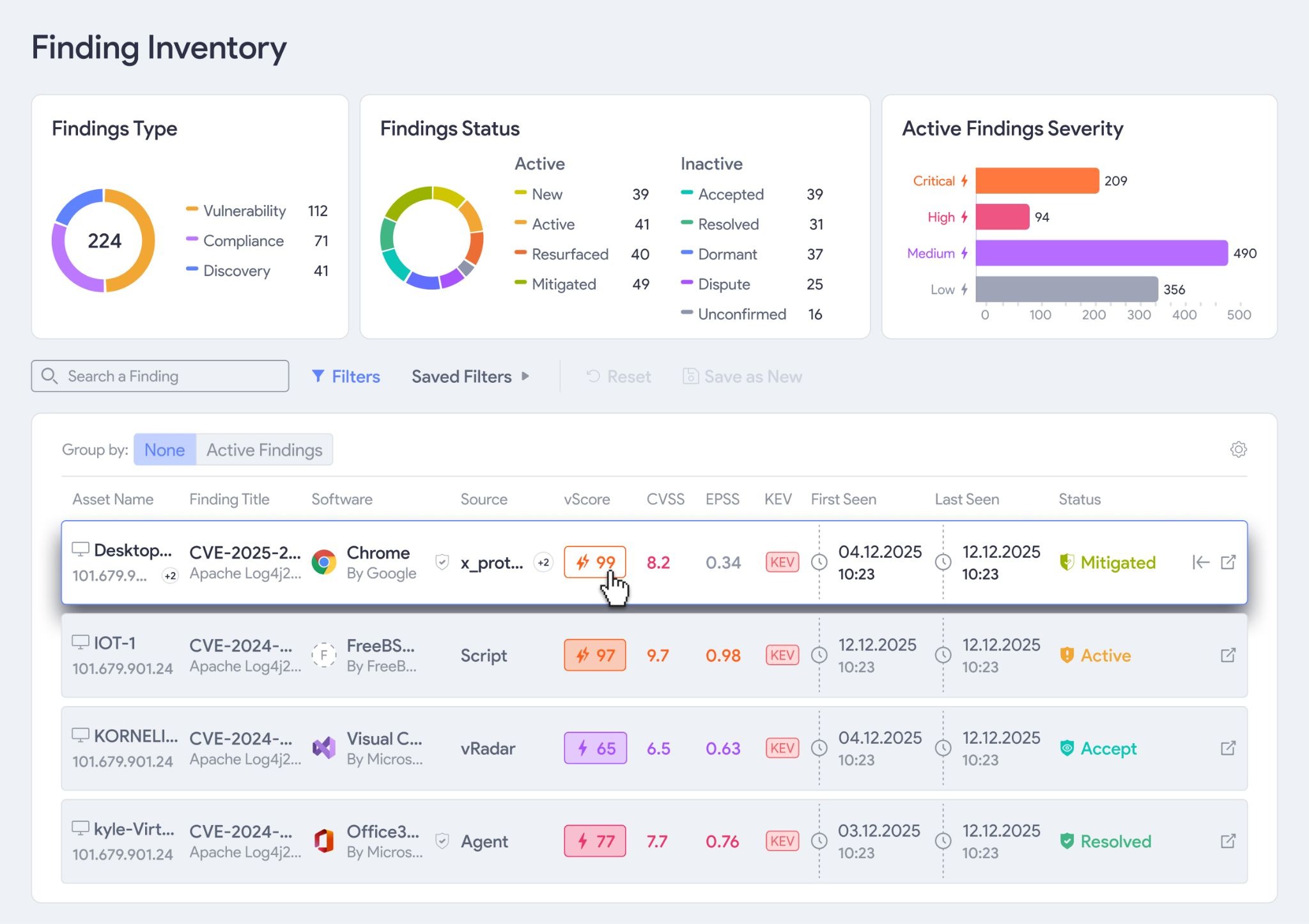
vIntelligence is Vicarius's second flagship product, a standalone intelligence platform designed to do what no traditional vulnerability management tool does: continuously validate, prioritize, and prepare vulnerabilities for remediation across your entire security stack in real time.
Where vRx solves the remediation problem patching, scripting, and configuration-based fixes at scale vIntelligence solves the upstream challenge: how do you know which vulnerabilities are real, which actually matter to your environment, and what to do about them first?
vIntelligence ingests data from the security tools you already have CrowdStrike, Qualys, Tenable, and many more normalizes that data into a unified, continuously-updated risk view, then layers on AI-powered validation to separate real exposures from noise. The result: security teams spend their time on the vulnerabilities that genuinely matter, not the 95% that don't.

Universal Intelligence Normalization
Accuracy at Scale, Powered by vAnalyzer
One of the most persistent pain points in enterprise security is data fragmentation. The average mid-enterprise runs between 5 and 20 security tools, each producing data in its own proprietary format with its own severity framework. A critical finding in one tool might be rated medium in another. There is no unified view, no shared language, no way to compare apples to apples.
vIntelligence solves this through its Universal Intelligence Normalization engine. The platform connects to any security vendor, ingests their data, and runs it through a five-stage pipeline: Ingest → Normalize → Enrich → Analyze → Prioritize.
Enrichment is where vIntelligence goes beyond simple aggregation. Every vulnerability is cross-referenced against leading threat intelligence sources and and cross matched with the MITRE ATT&CK framework mappings. This means your risk scores aren't just based on theoretical severity they reflect real-world exploitability, active threat actor activity, and whether a vulnerability is already being weaponized in the wild.
The output is a single, accurate, continuously-updated view of your true exposure not what your tools think might be a problem, but what is actually at risk in your specific environment right now.
The AI Red Team Agentic Validation Without Disruption
Knowing a vulnerability exists is one thing. Knowing it's actually exploitable in your specific environment is an entirely different challenge and it's the challenge that traditional tools consistently fail to address.
vIntelligence's AI Red Team capability is an agentic validation engine that automatically tests whether vulnerabilities can truly be exploited in your environment without risking production stability. This is not a BAS (Breach and Attack Simulation) tool running predefined scenarios against a limited set of attack vectors. It's something fundamentally different.
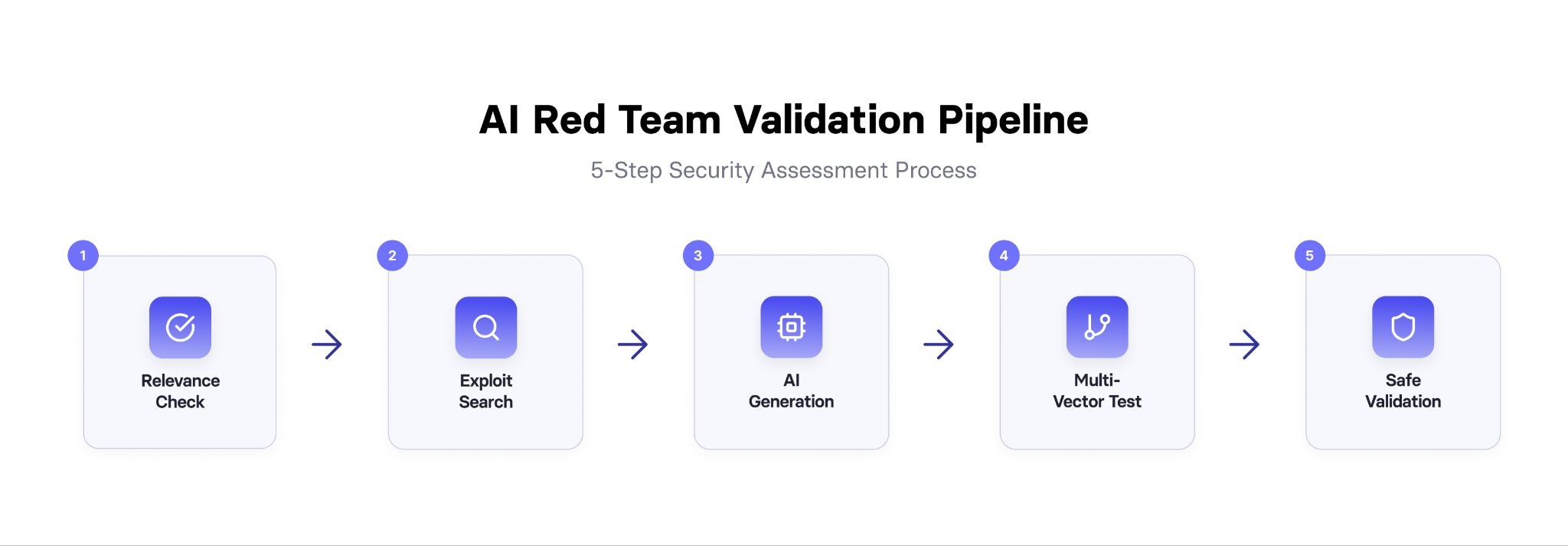
For each prioritized vulnerability, the AI Red Team runs through a five-step process:
- Relevance Check: Is this vulnerability actually applicable to your environment and configuration?
- Exploit Search: Are there known public exploits or proof-of-concept code available?
- AI Generation: When no existing exploit fits, vIntelligence's AI generates a custom validation script on demand.
- Multi-Vector Test: The vulnerability is tested across multiple attack vectors for a complete picture.
- Safe Validation: All testing is conducted in a way that produces zero production downtime or disruption.
The practical impact is striking. Traditional BAS platforms validate a limited set of predefined scenarios and can't tell you whether a specific CVE in your specific environment is exploitable. vIntelligence's AI Red Team validates vulnerabilities in minutes, at unlimited scale, with 95% of false positives eliminated through actual exploit testing rather than theoretical risk scoring.
Closing the Loop: From Intelligence to Remediation
Most security platforms are excellent at generating alerts. Very few are excellent at closing them. This is the fundamental gap that the vRx + vIntelligence combination addresses.
vIntelligence handles the intelligence side: continuous ingestion, normalization, enrichment, AI-powered validation, and prioritization. vRx handles the remediation side: automated patching, script-based fixes, configuration controls, and workflow integration with ITSM systems. The two products connect natively, creating a full closed-loop workflow:
Detect → Analyze → Validate → Remediate → Re-Validate → Monitor
Critically, every step includes proof of closure. After a fix is deployed, vIntelligence re-runs validation to confirm the vulnerability is actually resolved not just that a patch was applied, but that the exploit no longer works. This gives security teams and leadership auditable evidence that exposure has been eliminated, which matters enormously for compliance with regulations like SEC cybersecurity disclosure rules, NIS2, and DORA.
The measurable results speak for themselves: 81% reduction in mean time to remediation, 95% reduction in alert volume, and a mean remediation time of just 4.3 hours.
Who vIntelligence Is Built For
vIntelligence is designed for mid-enterprise and above organizations those with 1,000+ employees, multi-vendor security infrastructure, hybrid cloud environments, and dedicated security teams (not just IT generalists managing security on the side).
It's particularly valuable for:
- Security Operations teams drowning in alert volume who need to cut through noise and focus on real risks
- Vulnerability management teams who have scanners and data but no way to continuously validate or prioritize across tools
- CISOs and security leadership who need board-level reporting on exposure posture, compliance status, and remediation progress with evidence
- Organizations subject to regulatory requirements SEC, NIS2, DORA, cyber insurance mandates who need continuous monitoring and documented proof of remediation
Importantly, vIntelligence is not a rip-and-replace solution. It doesn't ask you to abandon CrowdStrike, Qualys, Tenable, or any other tool in your stack. It makes those tools more valuable by unifying their data, cutting their noise, and activating their insights into actual remediation workflows.
How vIntelligence Compares
The vulnerability management market has several established players Tenable, Qualys, Rapid7, and BAS platforms like AttackIQ, SafeBreach, and Cymulate. Each addresses part of the problem. None address all of it.
Traditional VM tools (Tenable, Qualys, Rapid7) excel at scanning and CVSS-based scoring but are blind between scans, produce enormous false positive rates, and offer no automated remediation. BAS platforms test security controls but don't integrate threat intelligence into prioritization, don't normalize data across vendors, and don't close the loop to remediation. Penetration testing provides point-in-time snapshots that are manual, slow, expensive, and inherently limited in coverage.
vIntelligence is the only platform that combines continuous multi-vendor intelligence normalization, AI-powered exploit validation, and native integration with automated remediation in a single unified platform rated 4.7/5 on Gartner and built with three proprietary moats that compound over time: a technology moat (proprietary AI script generation and multi-vendor normalization IP), network effects (each customer trains the AI models, improving script libraries and threat intelligence for all), and platform lock-in (replacing 3-5 point tools with deep workflow integration).
The Bottom Line
Vulnerabilities are being exploited in hours. Traditional security tools respond in weeks. That gap is where breaches happen and it's costing organizations an average of $5.7 million per AI-powered breach.
vIntelligence closes that gap. By continuously ingesting and normalizing intelligence from your existing tools, applying AI-powered agentic validation to confirm real exploitability, and connecting to vRx for automated remediation and proof of closure, vIntelligence transforms vulnerability management from a reactive triage exercise into a proactive, closed-loop security operation.
It won't replace the security tools you've invested in. It will finally make them work together and make your exposure management strategy match the speed of the threats you're facing.