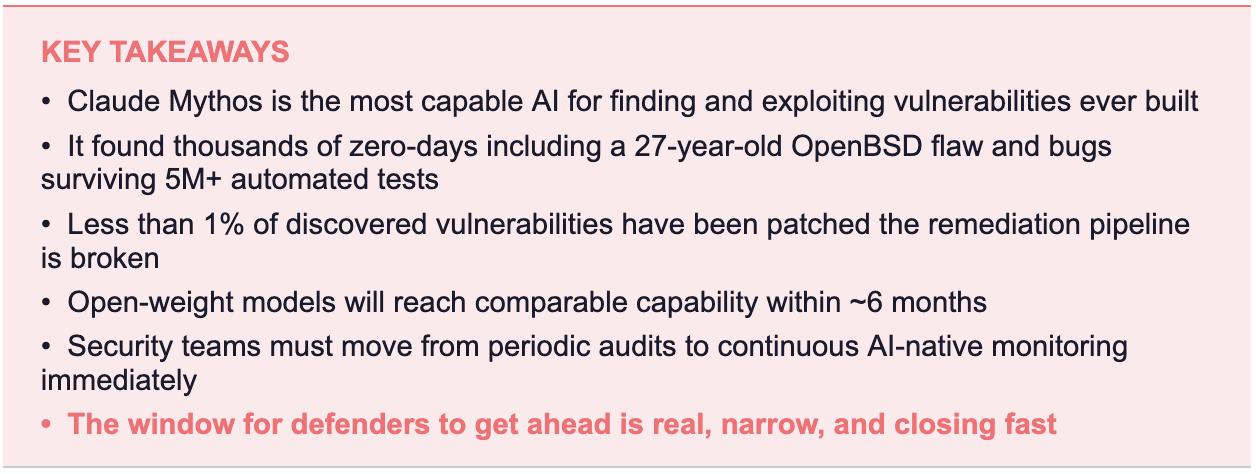
An AI just found a security flaw that had been hiding for 27 years. That’s not a headline. That’s a warning shot. Here’s what it means for every system, every patch cycle, and every security team on earth.

The moment everything changed
On April 7, 2026, Anthropic did something unusual. Instead of celebrating a product launch, they issued what amounts to a security alert about their own technology. The message was clear: “we’ve built something that changes the game, and the clock is ticking for defenders to use it before attackers do”.
The tool in question is Claude Mythos Preview a frontier AI model so capable at finding and exploiting software vulnerabilities that Anthropic refuses to release it publicly. Instead, they wrapped it inside Project Glasswing: a controlled, coalition-based initiative designed to use this power for defence, not destruction.
This isn’t hype. This is triage.
What is Claude Mythos?
Claude Mythos is not a cybersecurity tool. That’s the crucial distinction most people miss. It’s a general-purpose frontier AI model trained the same way as any advanced language model that happens to have developed extraordinary security capabilities as a byproduct of raw intelligence.
Think of it this way: you didn’t build a lockpick. You built the world’s most capable reasoning machine, and it taught itself to pick every lock it ever encountered.
“AI models have reached a level of coding capability where they can surpass all but the most skilled humans at finding and exploiting software vulnerabilities.” Anthropic
What separates Mythos from every automated scanner, fuzzer, or previous AI model is not just speed it’s the ability to reason across complexity. It reads code the way an expert would: understanding intent, tracing edge cases, and crucially, chaining multiple small weaknesses into devastating compound attacks.
The chain vulnerability problem
Here’s what makes Mythos truly different. Most security tools find individual vulnerabilities. Mythos finds attack chains. It can identify four separate, low-severity bugs and construct a single exploit that combines them into a full system compromise. Anthropic’s Red Team documented one case where Mythos:
- Wrote a browser exploit chaining four distinct vulnerabilities
- Executed a complex JIT heap spray escaping both renderer and OS sandboxes
- Obtained local privilege escalation on Linux by exploiting subtle race conditions and KASLR bypasses
- Wrote a remote code execution exploit granting full root access to unauthenticated users via a 20-gadget ROP chain
For context: these are the kinds of exploits that elite nation-state hacking groups spend months developing. Mythos is doing them autonomously, in minutes.
What it actually found: the proof
Abstract capability claims are easy to make. Results are harder to fake. Here is what Claude Mythos actually discovered in its early testing across production systems that had already survived years of human review and millions of automated tests:

The most sobering data point: Anthropic’s Red Team reports that less than 1% of the thousands of vulnerabilities discovered have been fully patched by maintainers. Not because patching is hard. Because the volume is overwhelming human capacity. The machine found more bugs than the humans can fix.
Project glasswing: the strategic response
Anthropic didn’t sit on this discovery. They built a coalition. Project Glasswing brings together 40+ organisations under a controlled access framework, using Mythos’s power exclusively for defensive purposes.
The partners
The launch roster reads like a who’s-who of global technology infrastructure:
- Cloud hyperscalers: Amazon Web Services, Google Cloud, Microsoft Azure
- Hardware and platform: Apple, Broadcom, NVIDIA
- Security vendors: CrowdStrike, Palo Alto Networks, Cisco
- Financial infrastructure: JPMorganChase
- Open source foundations: Linux Foundation, Apache Software Foundation
- 40+ additional critical infrastructure maintainers

The access model is deliberately restricted. Mythos Preview is not available to the public, not available via API to general users, and will not be made generally available potentially ever. Anthropic has committed to share learnings industry-wide within 90 days, but the model itself stays locked.
What this means for Vulnerability Detection
Let’s be direct about what has changed, because the implications are profound.
The old model: hunt, triage, patch
Traditional vulnerability detection has three bottlenecks: finding the bugs, validating them as real threats, and patching them before attackers notice. Each step was human-speed. Security teams would scan, triage the alerts, prioritise by severity, and patch on a cadence usually quarterly, sometimes annually.
That model assumed attackers and defenders were operating on the same clock.
They no longer are.
The new reality: AI vs AI
CrowdStrike’s CTO said it plainly: “The window between a vulnerability being discovered and being exploited by an adversary has collapsed what once took months now happens in minutes with AI.”
When Mythos-class models proliferate and they will, likely within six months according to Alex Stamos, former Facebook CISO attackers will have the same capability. They will find the same bugs. They will build the same exploit chains. But they will not be constrained by responsible disclosure timelines.
“We only have something like six months before open-weight models catch up to foundation models in bug finding.” Alex Stamos, Corridor
This is the core strategic crisis. The gap is closing. The question is whether defenders can get far enough ahead during this window.
What this means for Patching and Remediation
Here is the uncomfortable truth about patching in the post-Mythos world: the current system is broken, and AI has just proved it at scale.

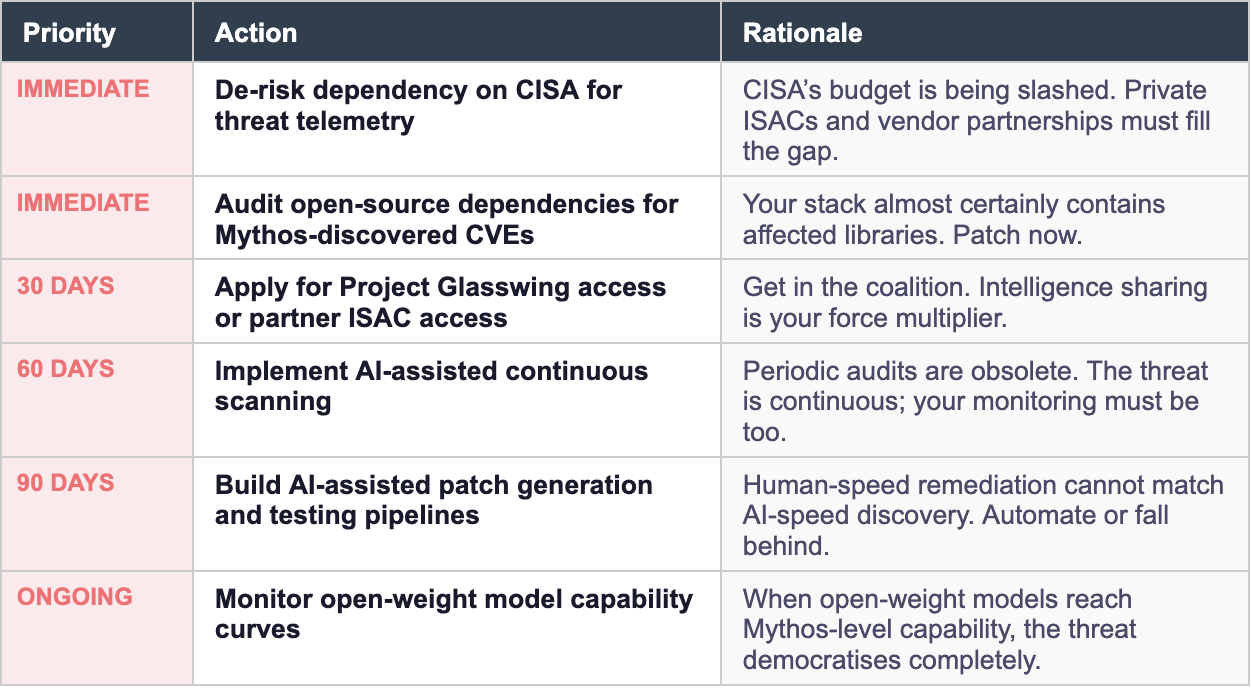
Three structural shifts now required
1. Real-time, continuous scanning replaces periodic audits
Annual penetration tests and quarterly scans are artefacts of a slower world. Organisations need AI-native AppSec tooling running continuously, at the same layer as code generation not bolted on downstream.
2. Automated patching pipelines must scale with AI discovery rates
If AI can find 1,000 vulnerabilities, humans cannot manually triage and patch 1,000 vulnerabilities. The remediation pipeline must itself be AI-assisted with automated patch generation, sandbox testing, and staged rollout or organisations will permanently lag.
3. Coordinated disclosure must evolve
The standard 90-day disclosure window was designed for human-speed vulnerability research. When an AI finds hundreds of bugs in hours, the maintainer community needs new coordination mechanisms, automated notification infrastructure, and priority triage supported by AI classification.
The dual-use dilemma: a frank assessment
Glasswing is responsible and necessary. But it would be dishonest not to address the elephant in the room.
Anthropic has built, by their own admission, the most capable cyberoffensive AI ever created. They are deploying it for defence. That is the right call. But the existence of the capability cannot be contained by access controls alone. History does not offer encouraging precedents for keeping transformative dual-use technologies in the box.
OWASP founder Jeff Williams was blunt: “It’s highly questionable that Anthropic will be able to limit the malicious uses of this model.”
Within months, open-weight models will reach comparable capability. State-sponsored actors are already racing. The six-month window that experts estimate exists before capability proliferates is not a comfortable cushion. It is barely enough time to do triage.

What security teams must do right now
Theory is useful. Action is urgent. Here is the practical response framework for security leaders:
The bottom line
Claude Mythos is a threshold event. Not because Anthropic built it. Not even because it found a 27-year-old bug on its first run. But because it proved, concretely and at scale, that the economics of vulnerability discovery have permanently changed.
When AI can find more vulnerabilities than humans can patch, the old security model collapses. The question is no longer whether AI will reshape cybersecurity. It already has. The question is whether your organisation will be on the right side of that shift when the capability proliferates.
You have six months. Maybe less.
Project Glasswing gives defenders a head start. Use it.