The traditional enterprise perimeter has dissolved, shifting the primary cybersecurity battlespace from hardware endpoints to the web browser. As organizations migrate critical workflows to the cloud, the browser has become the modern “common” operating system: a centralized, user-platform-agnostic hub where employees access high-value administrative controls like Meta Business Manager and corporate ad accounts. Despite acting as the ultimate gateway to these assets, the browser remains astonishingly under-protected. This oversight creates a dangerous visibility gap that threat actors now exploit using malicious browser extensions.
While traditional Endpoint Detection and Response (EDR) solutions excel at the OS level, they frequently go blind inside a browser tab. Operating as silent insiders within this trusted environment, malicious extensions easily bypass multi-factor authentication and scrape authenticated platforms, turning the very productivity tools your teams rely on into devastating weapons against the enterprise.
The CL suite case study: How productivity extensions hide malicious payloads
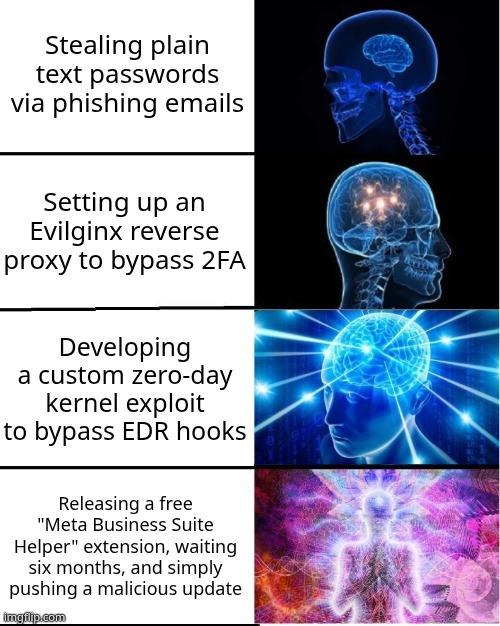
The recent discovery of the "CL Suite" Chrome extension provides a chilling masterclass in how modern threat actors disguise malicious payloads within seemingly helpful utilities. Marketed directly to digital marketing professionals as an indispensable productivity tool for Meta Business Suite, CL Suite successfully masked its true intentions behind legitimate functionality. Behind the scenes, however, it functioned as a sophisticated data exfiltration engine. Instead of merely scraping public-facing data, the extension specifically targeted high-value assets, quietly siphoning off Time-Based One-Time Password (TOTP) seeds, proprietary Business Manager contact lists, and sensitive advertising analytics data straight to attacker-controlled infrastructure.
This successful infiltration was largely due to the developers' use of the "sleeper agent" deployment tactic. By keeping the initial versions of the extension completely benign, the tool easily bypassed the Chrome Web Store's initial security vetting. It sat quietly for months, building a large, trusting user base and accumulating positive reviews from marketing teams. Only after establishing this massive footprint did the developers push a routine update that contained the malicious payload, instantly weaponizing the extension across thousands of corporate endpoints before security teams had any reason to suspect a breach.
Why Meta/Facebook Business accounts are high-value targets
Threat actors are strategically pivoting away from standard credential theft, realizing that compromising individual user accounts yields a relatively low return on investment. Instead, they are setting their sights on high-privilege administrative roles, specifically targeting personnel who manage Meta Business Manager and corporate ad accounts. Specialized extensions like CL Suite are explicitly built to navigate, scrape, and exploit these complex, dynamic interfaces, contrasting sharply with standard "infostealers" that indiscriminately grab saved passwords and local files.
Several key factors make Meta Business Manager and similar corporate accounts highly lucrative targets for modern threat actors:
- Unrestricted financial access: A single hijacked advertising session can grant an attacker instantaneous access to massive corporate marketing budgets, allowing them to run fraudulent campaigns and rapidly drain funds.
- High-value data harvesting: These administrative platforms house proprietary partner data, sensitive analytics, and extensive contact lists that can be leveraged for secondary attacks or sold on the dark web.
- Bypassing traditional defenses: Since attackers piggyback on active, authenticated sessions, traditional multi-factor authentication (MFA) is rendered completely useless; the extension simply intercepts TOTP codes and session tokens in real-time.
To execute these targeted attacks and maintain their foothold, malicious extensions employ advanced technical capabilities specifically designed to manipulate the Document Object Model (DOM) on authenticated Meta platforms. By directly interacting with the underlying page structure, these extensions can silently suppress security popups, scrape active sessions for valuable data, and inject bidirectional cookies that establish persistent, unauthorized access long after the user has navigated away from the page.
How broad extension permissions enable data theft
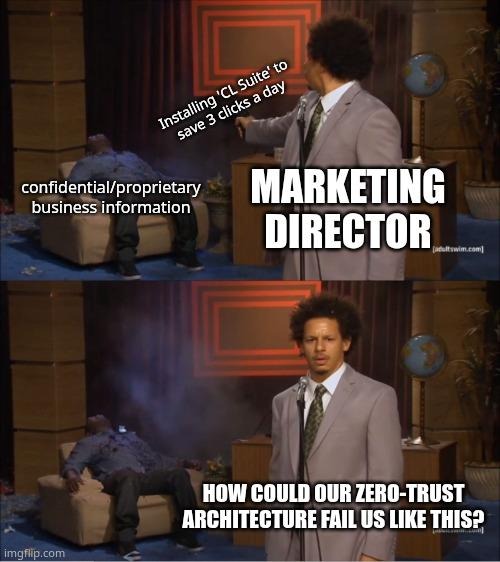
The foundational enabler of this massive data theft lies in the inherently flawed permission models utilized by modern web browsers, combined with the sophisticated methods attackers use to exploit trusted enterprise environments. When employees install new productivity tools to streamline their workflows, they often inadvertently hand over the keys to the corporate kingdom without triggering a single security alert.
The danger of broad access permissions
When marketing or HR personnel install a new productivity tool, they are frequently greeted with a prompt requesting permission to read and change data on all websites, often represented in the codebase as <all_urls>. Conditioned by years of software installations and eager to access the tool's basic functionality, these non-technical users habitually click "Accept All." This single action inadvertently grants the extension unrestricted rights to read, modify, and exfiltrate every piece of data rendered on their active Meta or corporate tabs.
Evolving evasion techniques
The threat landscape has only grown more complex in 2026, with attacker tradecraft evolving to easily bypass traditional defenses. Extension developers are now routinely deploying heavily obfuscated code and leveraging AI-generated scripts that perfectly mimic legitimate Facebook and Meta API traffic. This sophisticated camouflage allows malicious activity to blend in seamlessly with normal administrative tasks, effortlessly evading detection by automated Chrome Web Store scanners and legacy network security tools.
Hidden supply-chain risks
Organizations must also contend with severe, often invisible supply-chain risks associated with the browser extension ecosystem. A common and highly effective scenario involves reputable, widely used marketing tools being quietly purchased by threat actors. These new owners then weaponize the tool by pushing a malicious update to the existing install base, immediately turning a trusted corporate asset into a silent insider threat without requiring the user to accept any new permissions or download a new application.

Implementing browser-level security for unmanaged extensions
To counter these sophisticated threats, organizations must embrace a fundamental paradigm shift in enterprise security governance. Browser extensions - particularly those utilized by marketing and administrative teams - can no longer be viewed as harmless, user-managed utilities. They must be explicitly categorized and managed as unmanaged SaaS applications, to be subject to the same rigorous procurement, auditing, and lifecycle management processes as any core enterprise software. This requires a decisive move away from outdated, reactive security measures towards implementing proactive defenses directly at the point of interaction.
Browser-level security requires transitioning to modern, automated controls:
- Real-time behavioral monitoring: Moving beyond manual whitelisting, organizations must deploy automated systems that provide real-time risk scoring and behavioral monitoring at the browser layer to catch "living-off-the-browser" attacks that easily bypass traditional endpoint signatures.
- Browser isolation: Implementing the principle of "least privilege" for web browsing by utilizing browser isolation technologies to separate high-risk web activity from the underlying corporate network.
- Dedicated secure profiles: Establishing heavily restricted extension environments and dedicated, secure browser profiles specifically for accessing high-value platforms like Meta Business Manager, ensuring that administrative tasks are isolated from everyday web browsing.
Close the visibility gap on your most critical endpoint
The web browser has undeniably become the modern operating system, serving as the primary interface for our most critical business applications. As the discovery of the CL Suite extension perfectly illustrates, malicious browser add-ons have evolved into the primary vector for bypassing traditional MFA and compromising critical business platforms like Meta Business Manager. Treating the browser as a simple application leaves the front door to your enterprise data wide open.
It is imperative that security leaders take immediate action to audit their organization's browser health and close this dangerous visibility gap. Gain immediate insight into the unmanaged extensions lurking on your corporate network by requesting a free personal demo of vRx by Vicarius, and take the first step toward securing your most critical enterprise endpoint today.