Tenable tells you what's vulnerable. Qualys gives you a list. Rapid7 adds some context. Then it's your problem.
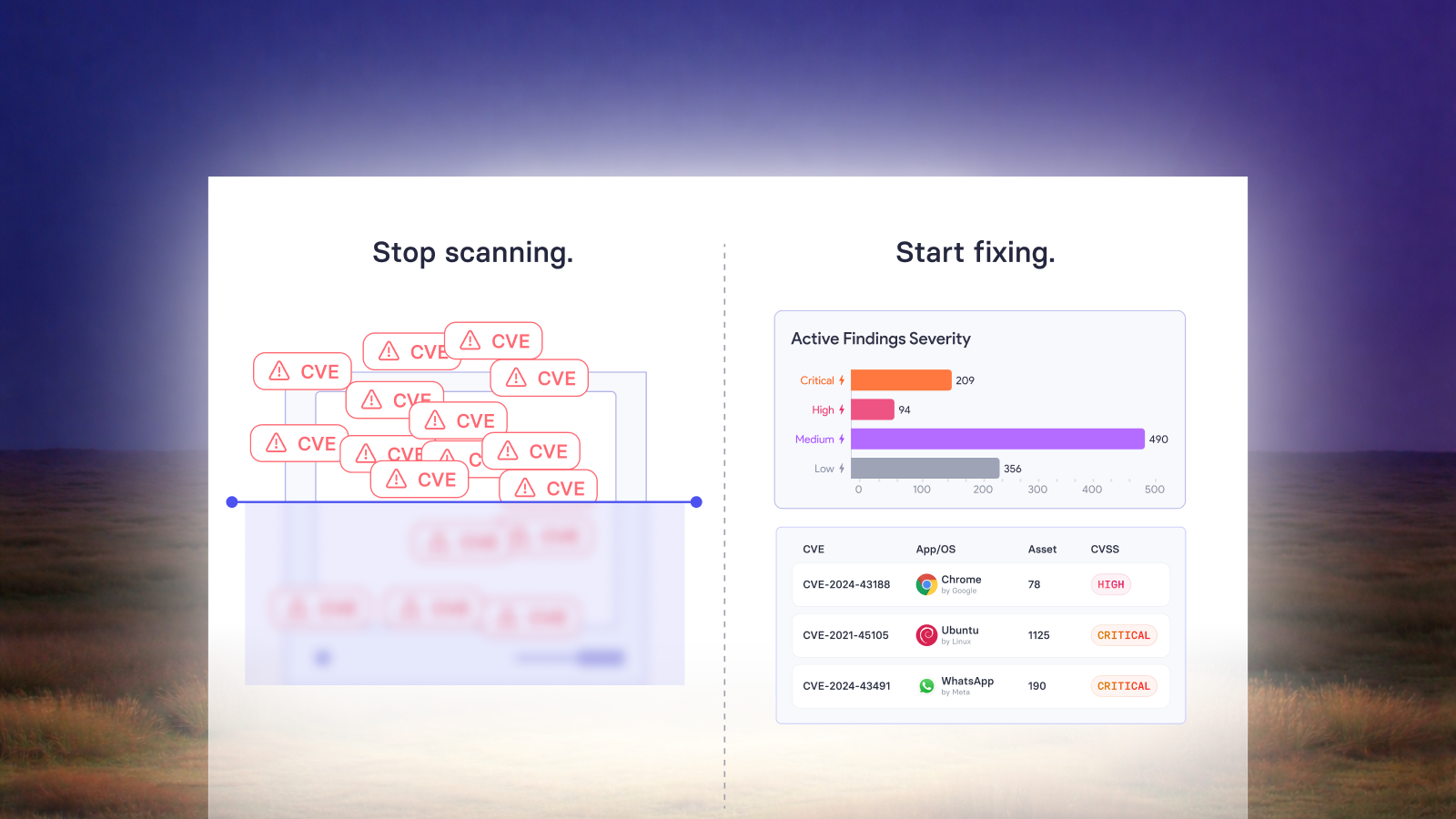
You get a report with 4,000 CVEs ranked by CVSS score. You have a team of three. And your CISO wants an update by Friday.
This is the state of vulnerability management for most security teams today. Platforms built around scanning and reporting not around reducing risk. You end up doing the hard work manually: triaging, prioritizing, writing tickets, chasing engineers, building reports from scratch.
Vicarius was built to automate the parts that eat your week. Here are six of them.
1. Figuring out which CVEs actually matter
Most platforms rank vulnerabilities by CVSS score. The problem: CVSS measures theoretical severity, not real-world risk. A CVSS 9.8 with no public exploit and no exposure to your environment is less urgent than a CVSS 6.5 that's actively being weaponized and sitting on an internet-facing server.
Triaging that difference manually for thousands of vulnerabilities takes hours. And if you get it wrong, you're patching the wrong things while the actual threats sit open.
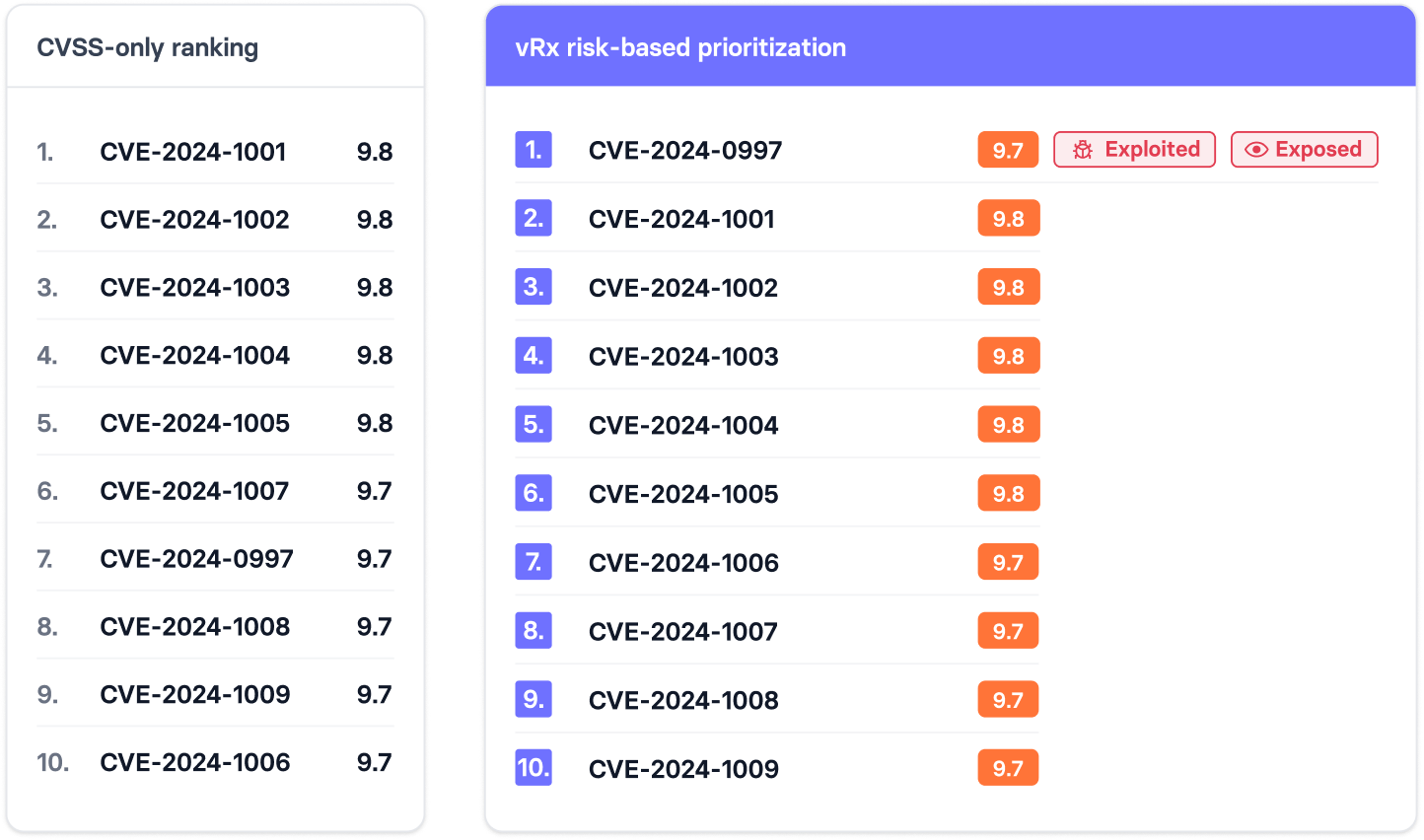
What vRx does:
Automatically cross-references every vulnerability against active exploit data, threat intelligence feeds, and your actual environment context. It surfaces what needs fixing now not what scores highest on paper. The prioritized list your team gets is short enough to act on, not long enough to ignore.
2. Deploying patches without a ticket queue
The average time from vulnerability discovery to patch deployment in enterprise environments is over 100 days. The bottleneck isn't usually the security team it's the process. Security finds it, creates a ticket, ops team picks it up when they can, patch gets tested, patch gets scheduled, patch gets deployed. Weeks pass. Meanwhile, the CVE you reported is in the news.
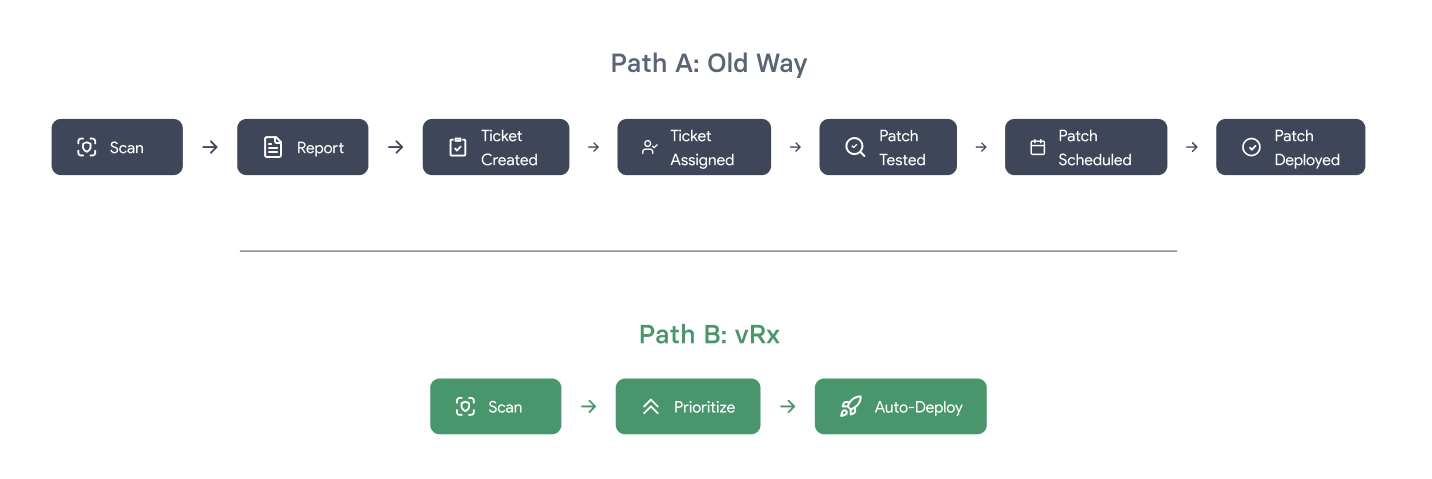
What vRx does:
Pushes patches directly without waiting for a ticket to move through a queue. For supported systems, you set the policy, vRx handles the deployment. Patch windows, rollback options, exceptions all configurable. The fix happens on your timeline, not whoever's turn it is to process the backlog.
3. Mapping vulnerabilities to active exploits in the wild
CISA's Known Exploited Vulnerabilities catalog is one of the most useful signals in threat intelligence. If a CVE is on that list, it's being exploited right now by real attackers. It should move to the top of your queue immediately.
Most platforms don't do this automatically. You have to check manually, cross-reference your asset list, and figure out if you're exposed. That's a process that doesn't happen consistently under pressure which is exactly when it matters most.
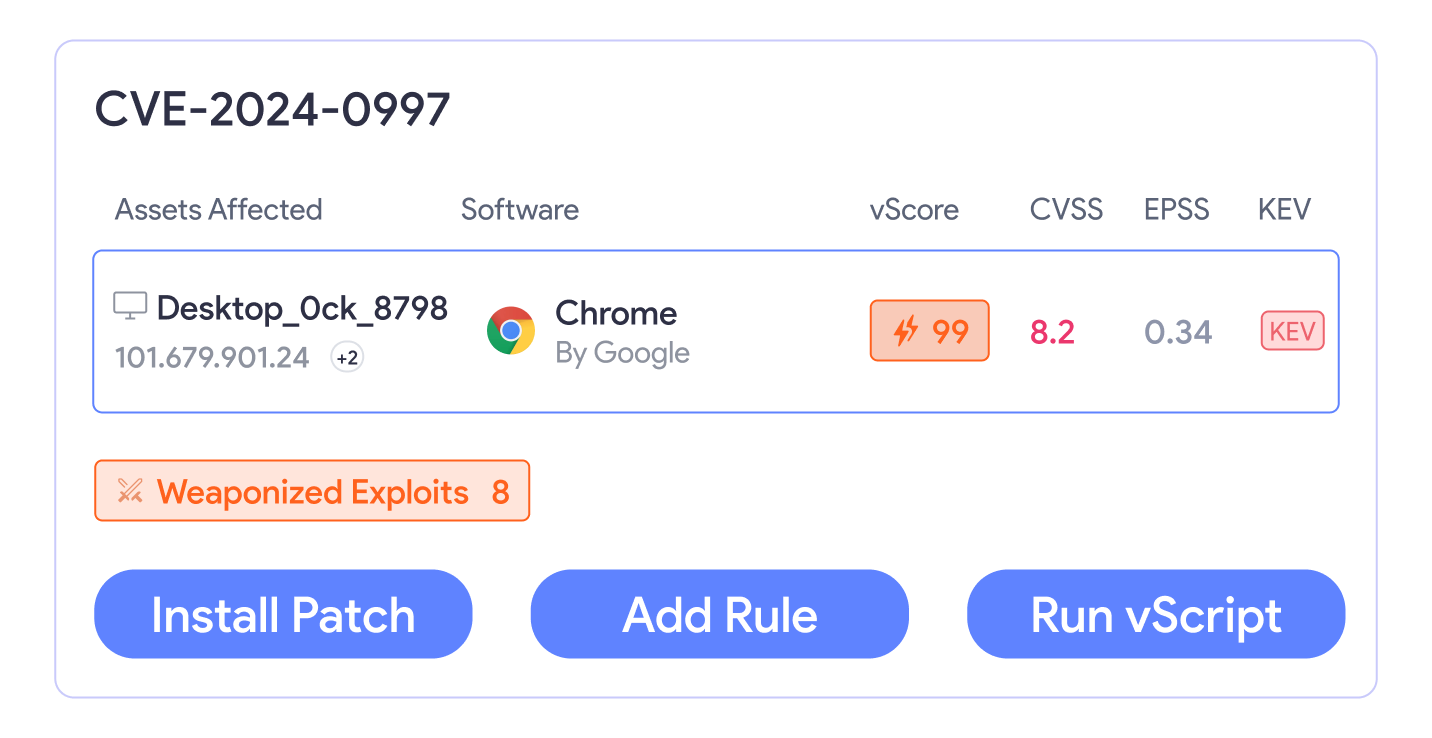
What vRx does:
Maps your environment against the CISA KEV catalog and other active exploit sources continuously. When a CVE affecting your assets appears on the list, it gets flagged automatically no manual cross-referencing required. You find out before you read about it on security Twitter.
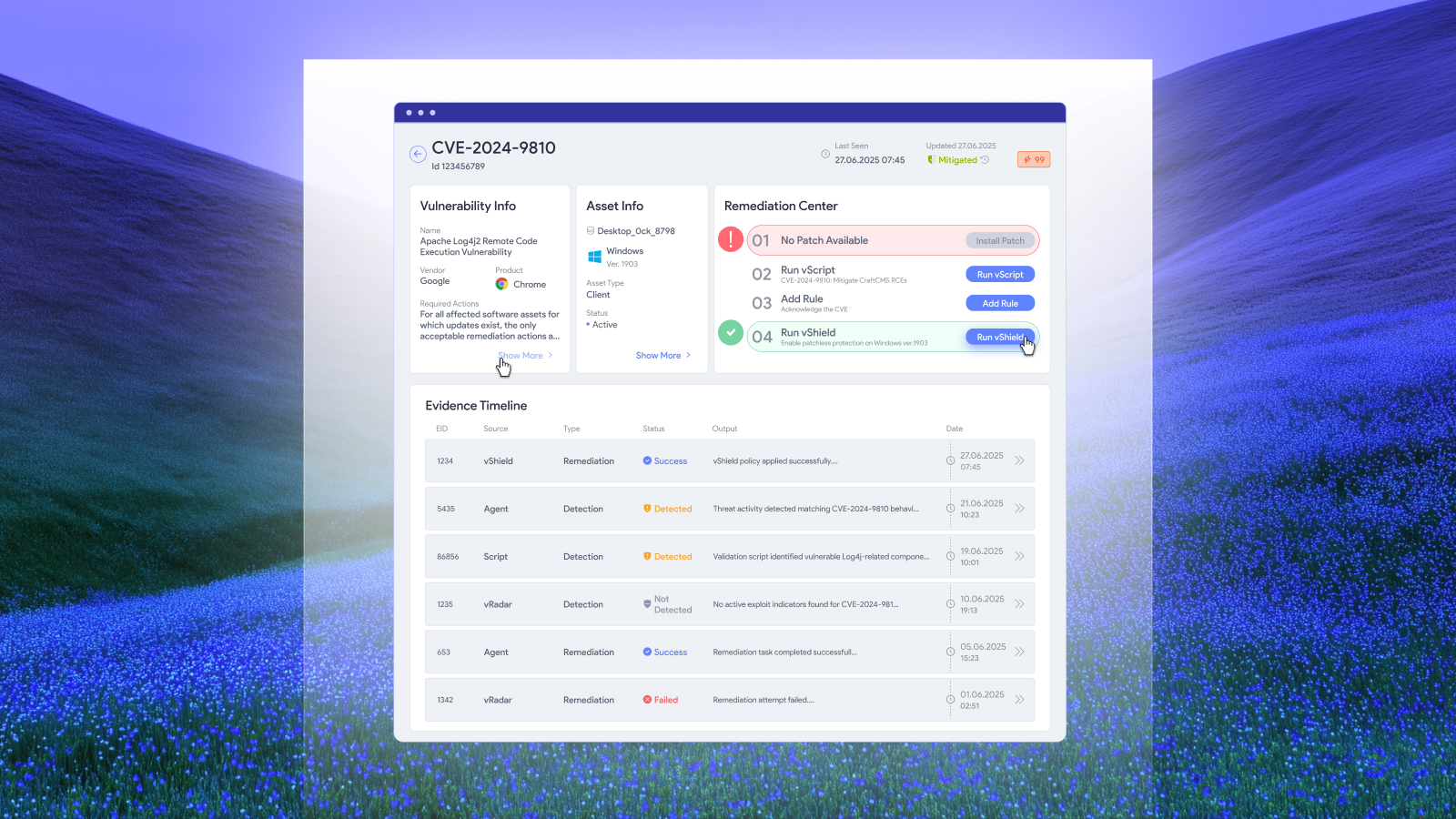
4. Generating remediation scripts on the spot
Not every vulnerability has a patch. Some need a configuration change, a service restart, a registry edit, or a workaround script. Finding the right fix, writing it, testing it, and deploying it that's work that falls to your team on top of everything else.
For one CVE, maybe 30 minutes. For 50 CVEs that need custom fixes? You do the math.
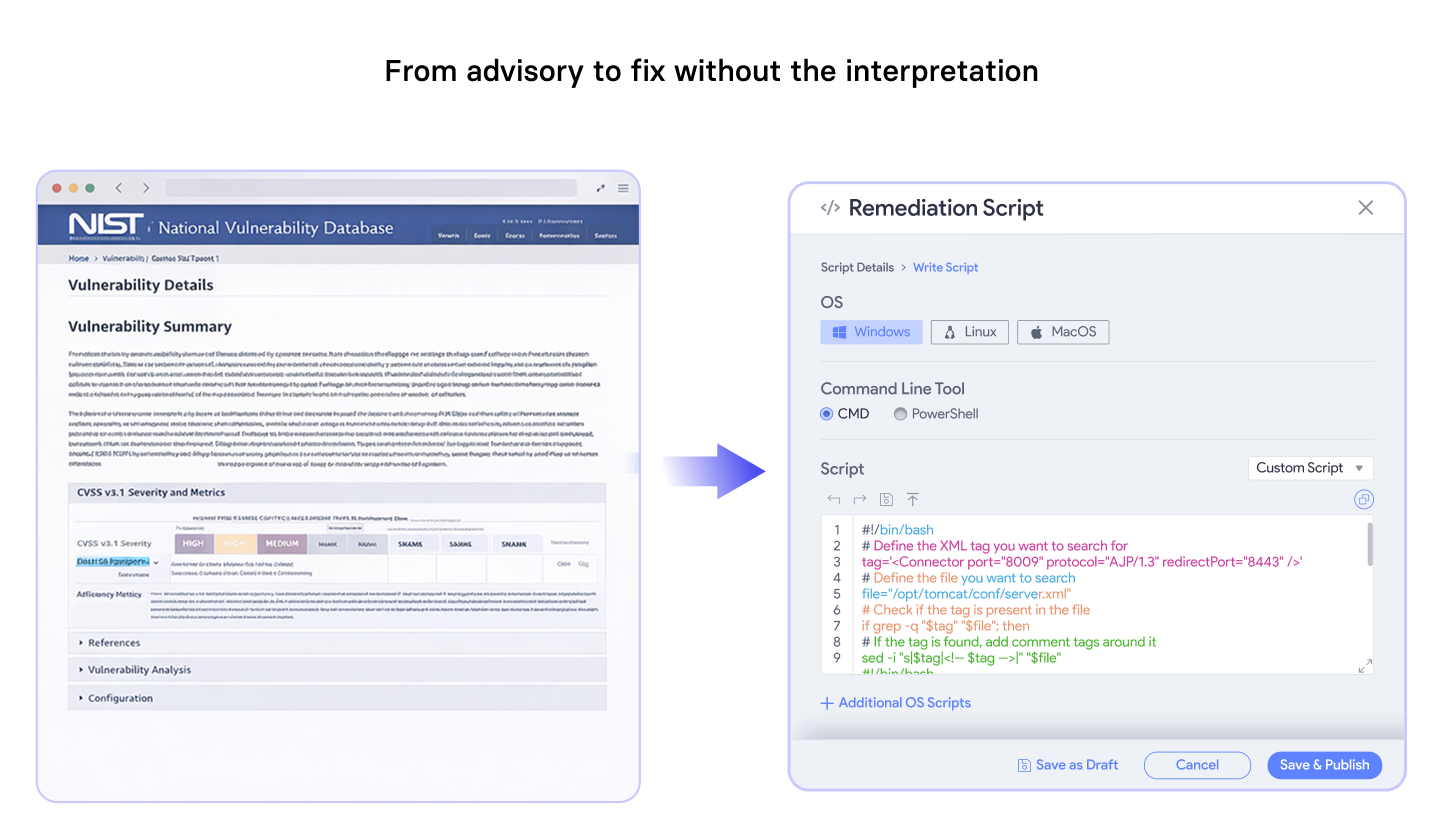
What vRx does:
Generates remediation scripts automatically for vulnerabilities that don't have a standard patch. Your team gets a ready-to-run fix not a NIST advisory that requires an hour of interpretation. You review it, approve it, and deploy. The script writing happens in the platform, not in someone's terminal at 11pm.
5. Tracking SLA compliance and remediation progress
Your security policy probably says critical vulnerabilities get patched within 15 days. High within 30. That sounds reasonable until you try to actually track it across 500 assets, multiple owners, and overlapping patch cycles.
Tenable will tell you the vulnerability is open. It will not tell you it's been open for 23 days and is about to breach your SLA. That report you have to build yourself.
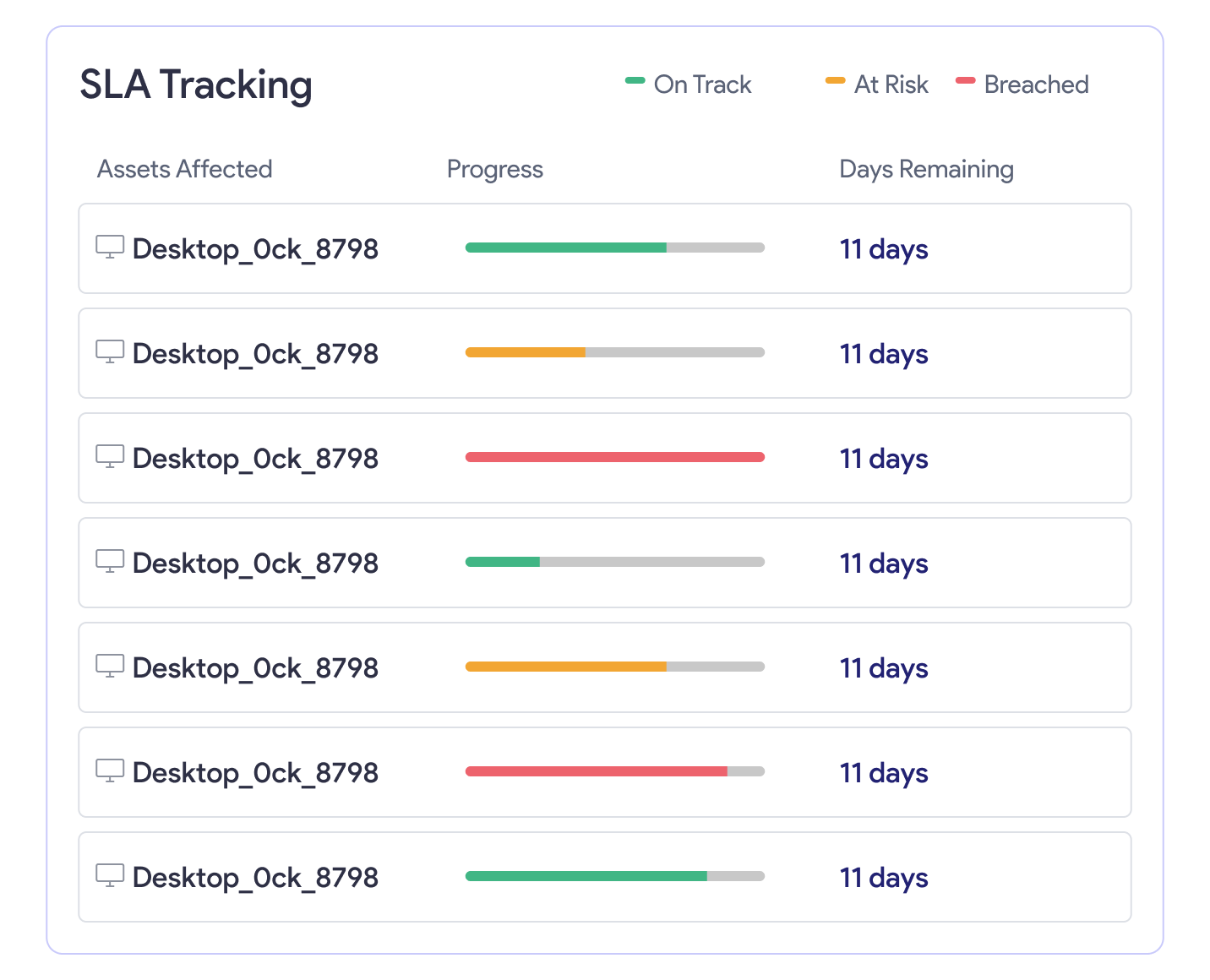
What vRx does:
Tracks every open vulnerability against your defined SLA thresholds automatically. You see what's on track, what's at risk, and what's already breached. Owners get notified before deadlines, not after. You stop finding out about SLA violations when someone asks why a critical CVE has been open for 6 weeks.
6. Building reports for leadership without the spreadsheet work
Every security team knows the Friday afternoon ritual: pulling data from the scanner, copying it into a spreadsheet, formatting it, adding context, writing an executive summary, and hoping the numbers make sense to someone who doesn't speak CVE.
It takes hours. It happens every week. And the output is often a 40-slide deck that gets skimmed for 90 seconds.
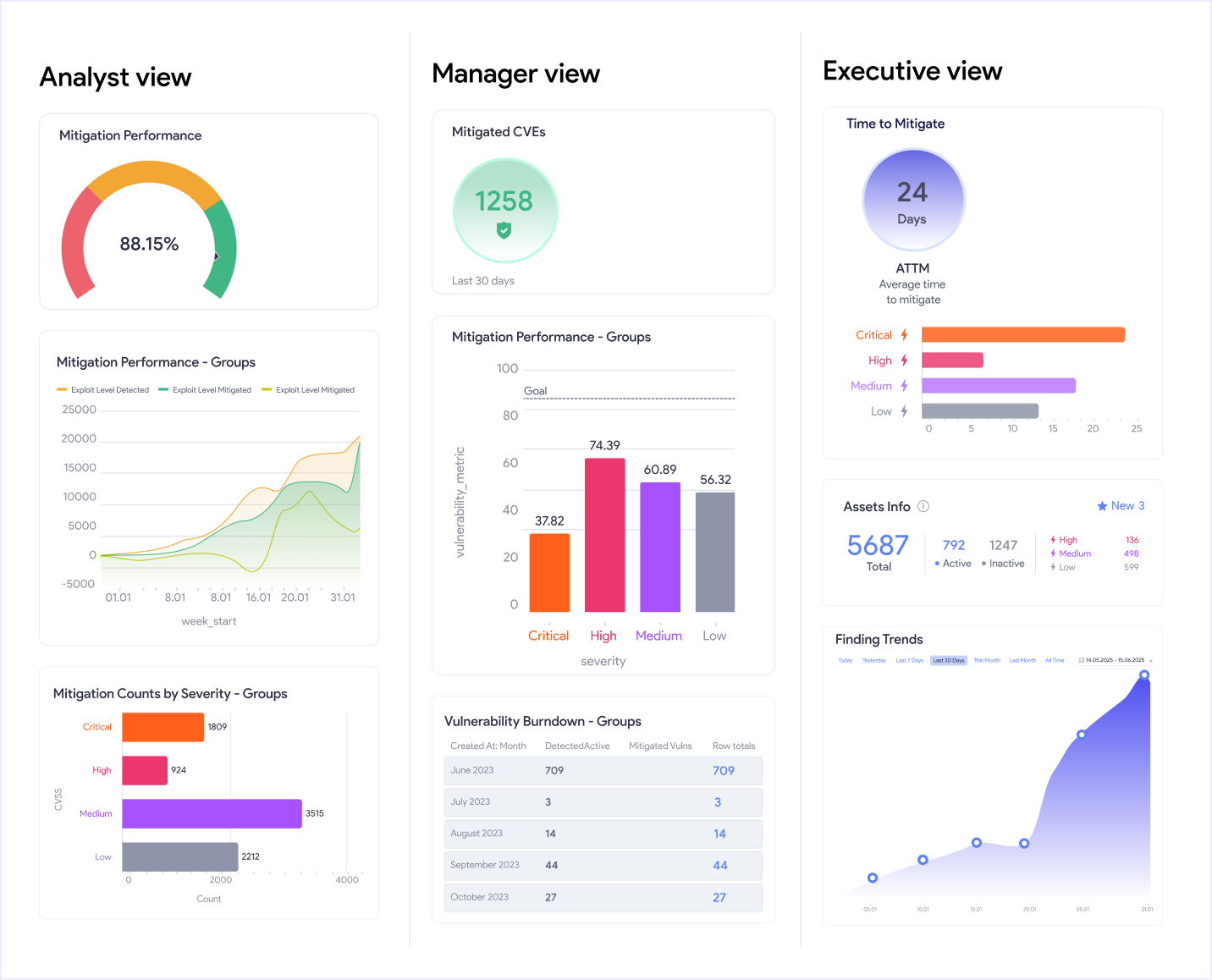
What vRx does:
Generates reports automatically tailored for the audience. Your analyst gets a technical breakdown. Your manager gets remediation status by team. Your CISO gets risk trend over time with business context. No manual data pulls. No formatting. You set the template, the platform generates the report.
The difference isn't features. It's what you stop doing.
Tenable, Qualys, and Rapid7 are scanning platforms with reporting layers on top. They were built to tell you about risk. What you do with that information is largely up to you.
Vicarius was built around a different question: how much of this can we take off your plate entirely?
The six tasks above are the ones that consume the most time for security teams with the least strategic value. Your job isn't to triage CVEs by hand. It isn't to write remediation scripts or chase SLA spreadsheets. Those are logistics problems and logistics problems should be automated.
When those tasks run in the background, your team works on what actually requires human judgment: architecture decisions, response planning, risk conversations with the business.
That's the shift vRx is built to create.
Ready to see it in action?
Book a 30-minute demo and we'll show you exactly how vRx handles your current environment, not a generic walkthrough.
Also read:
How Vicarius patchless protection brings unpatchable assets to acceptable risk levels
When patching isn't enough: how vRx's scripting engine closes the remediation gap