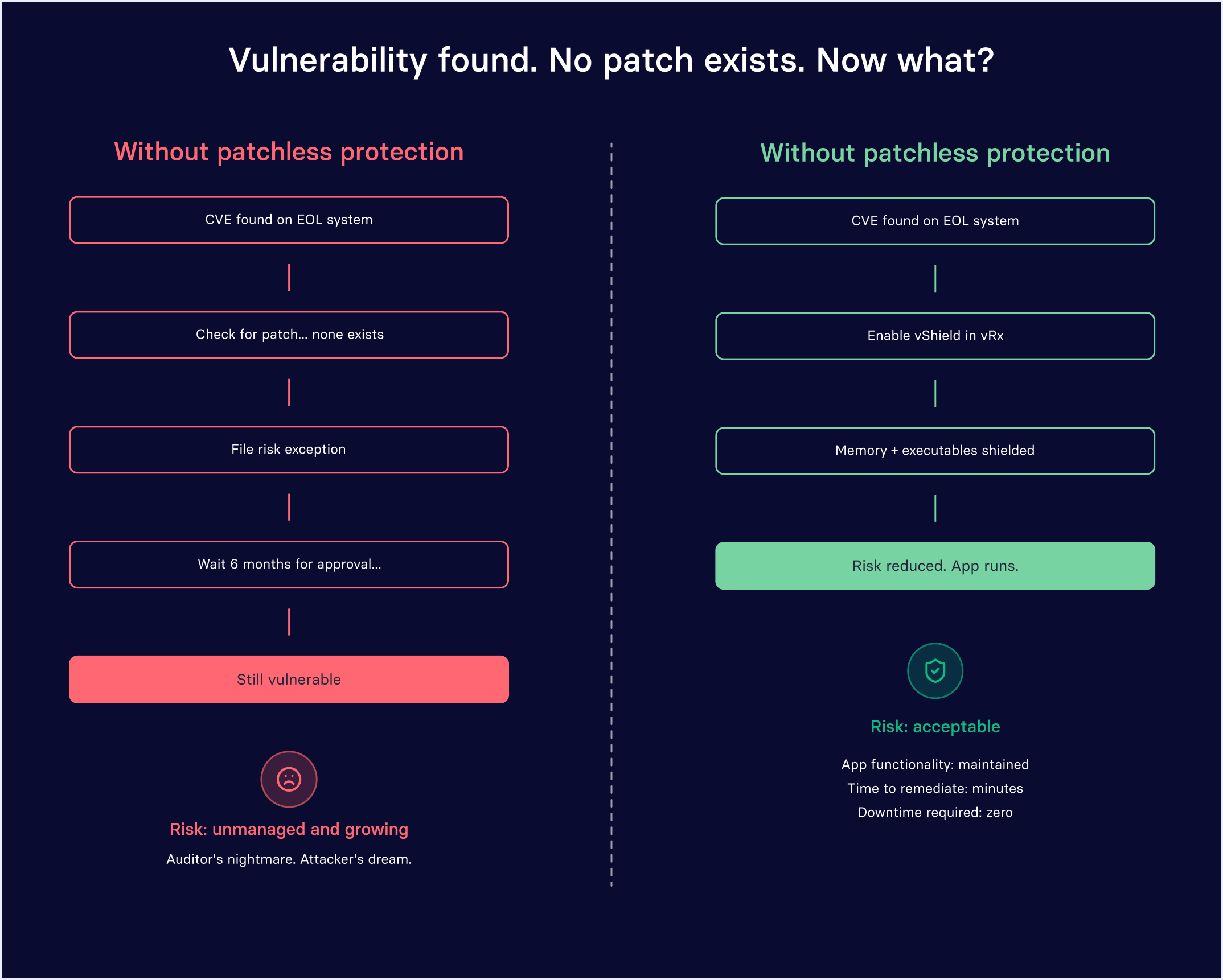
When patching isn’t an option, your risk doesn’t have to stay unmanaged. Here’s how in-memory protection turns your biggest liability into a controlled variable.
The uncomfortable truth about your environment
Let’s cut to the chase, you have systems in your environment that cannot be patched. Maybe it’s a Windows Server 2012 instance running a mission-critical application that nobody wants to touch. Maybe it’s a third-party application whose vendor went dark two years ago. Or maybe it’s a legacy Java version that an entire internal workflow depends on, complete with a list of known CVEs that grows longer every quarter.
You’re not alone. The average enterprise runs hundreds of applications across its endpoints, and a meaningful percentage of those are either end-of-life (EOL), end-of-support (EOS), or simply waiting on patches that may never arrive. These aren’t hypothetical edge cases. They’re the operational reality for security and IT teams in manufacturing, finance, healthcare, government, and virtually every other sector.
The question isn’t whether unpatchable assets exist in your environment. The question is: what are you doing about them?
Understanding the patch gap (and why it’s getting worse)
The “patch gap” is the window of time between when a vulnerability is disclosed and when a validated patch is actually deployed on your endpoints. For standard software from responsive vendors, this window can still stretch 60 to 120 days once you factor in testing, change control, and deployment cycles. For EOL operating systems and abandoned third-party apps, that gap stretches to infinity.
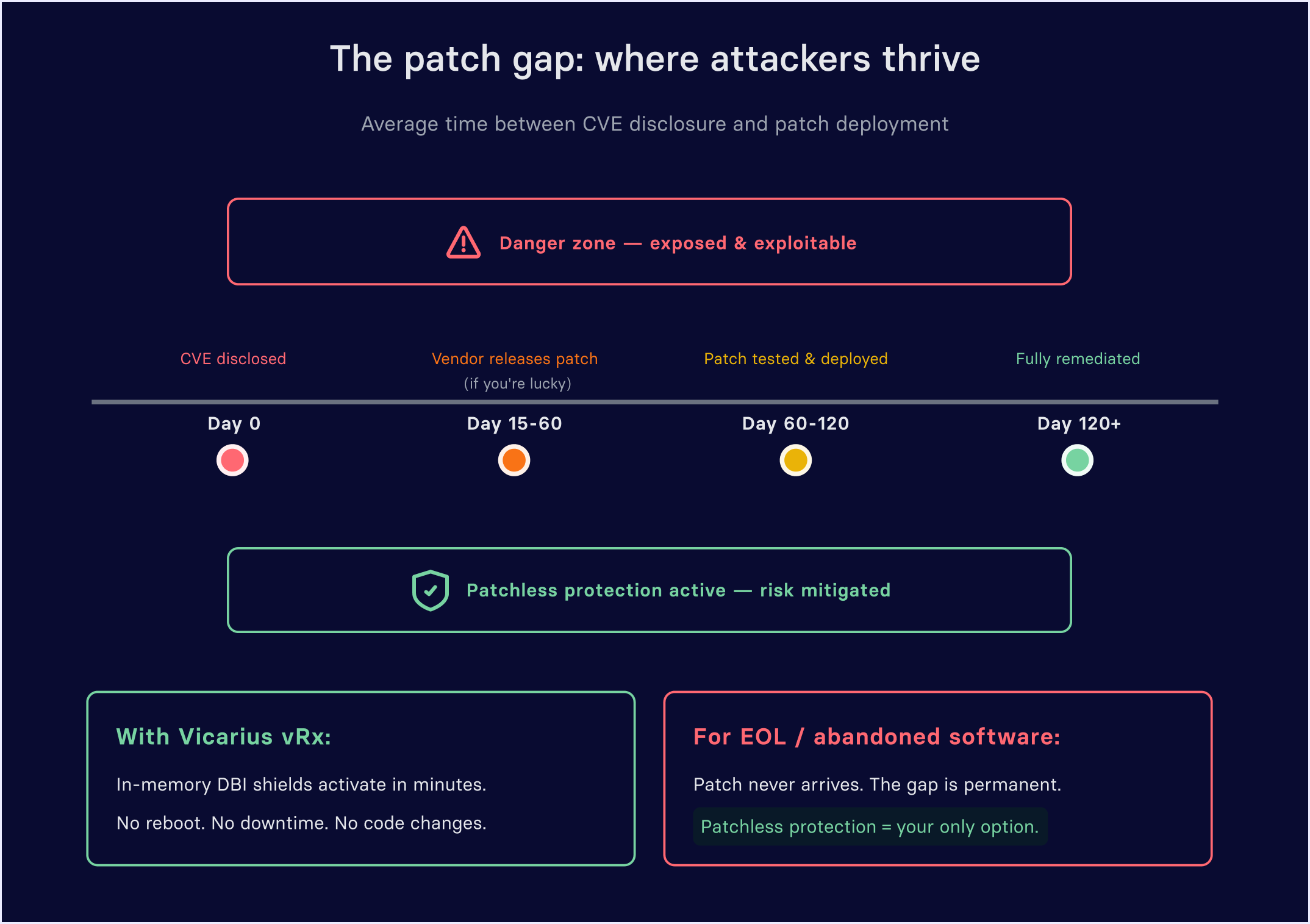
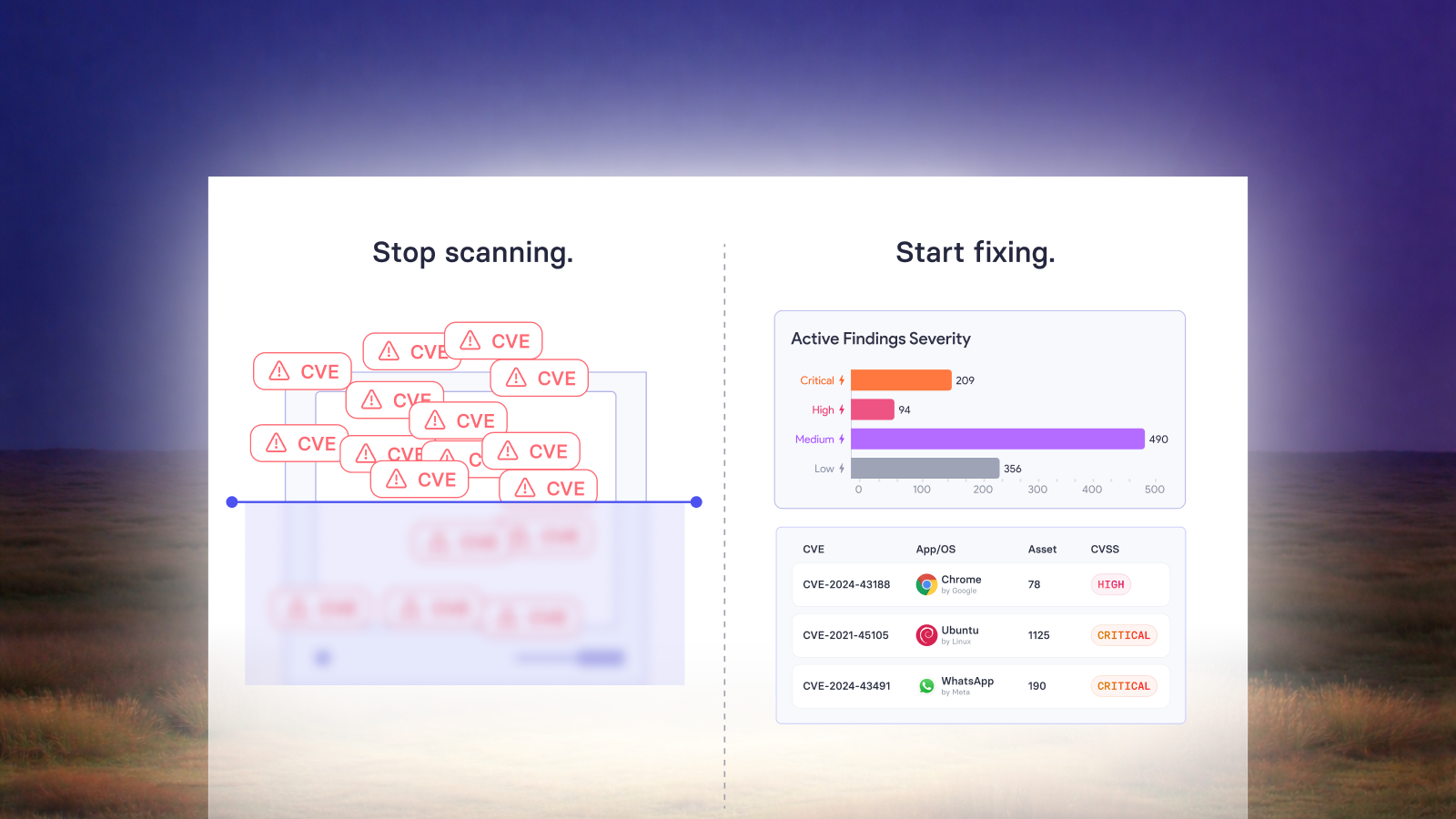
During this window, attackers have a published playbook for exploiting your systems. Meanwhile, your vulnerability scanner dutifully reports the same critical finding every scan cycle, and your risk register grows a little longer. If you’re relying solely on traditional patch management, you’re stuck in a loop with no exit condition.
This is the exact problem that Vicarius’s Patchless Protection (vShield) was designed to solve.
How Patchless Protection works: a technical overview
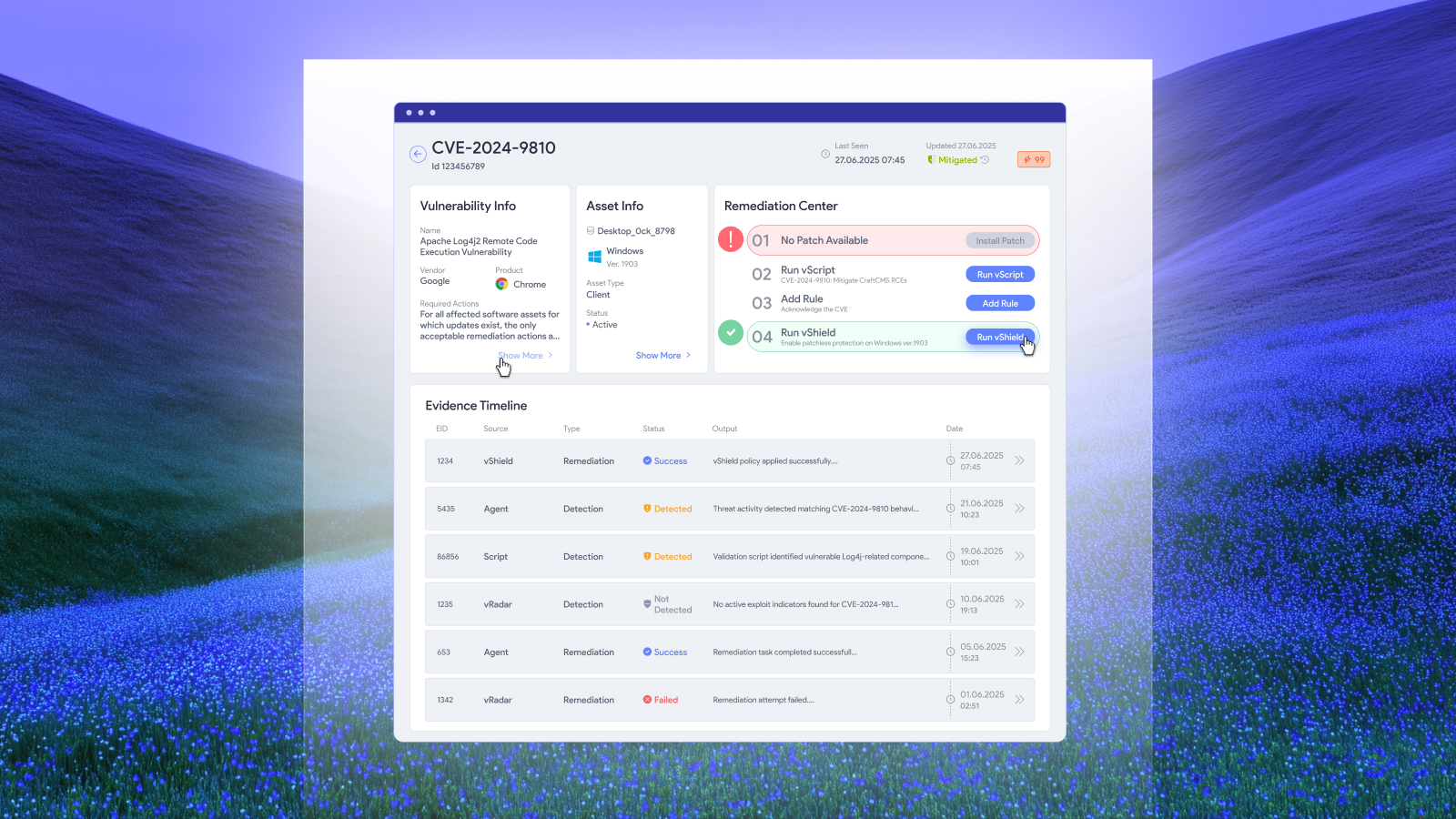
Patchless Protection is a proprietary compensating control built into Vicarius vRx. It doesn’t modify the vulnerable application’s code or require you to swap out components. Instead, it operates at the memory level, creating a protective barrier around the application’s executables and sensitive API surfaces.
Here’s what happens under the hood:
1. Executable Wrapping: vRx identifies the legitimate executables associated with the vulnerable application and wraps them in a secure memory envelope. The application continues to function normally, but its memory space is now monitored and protected.
2. Dynamic Binary Instrumentation (DBI): Using DBI technology, vRx tracks vulnerable functions as they’re loaded into the application’s memory space. This allows the platform to intercept exploitation attempts at runtime rather than relying on signature-based detection.
3. Sensitive API Access Restriction: The platform identifies and restricts access to memory regions associated with exposed APIs commonly targeted by exploits. This limits the attack surface without disabling the application’s core functionality.
4. Configurable Response: When an exploitation attempt is detected, vRx can either notify the administrator or actively block the system call in memory, depending on your configuration. This gives you the flexibility to run in monitor-only mode during initial rollout and switch to active blocking once you’ve validated the behavior.
The result: the vulnerable application continues to run, your business process stays operational, and the exploitable pathways are neutralized. No reboots. No downtime. No code changes.
Where Patchless Protection fits in your Remediation strategy
Patchless Protection isn’t a replacement for patching, it's a critical complement to it. Vicarius vRx provides three built-in remediation methods that work together to close gaps across your entire environment:
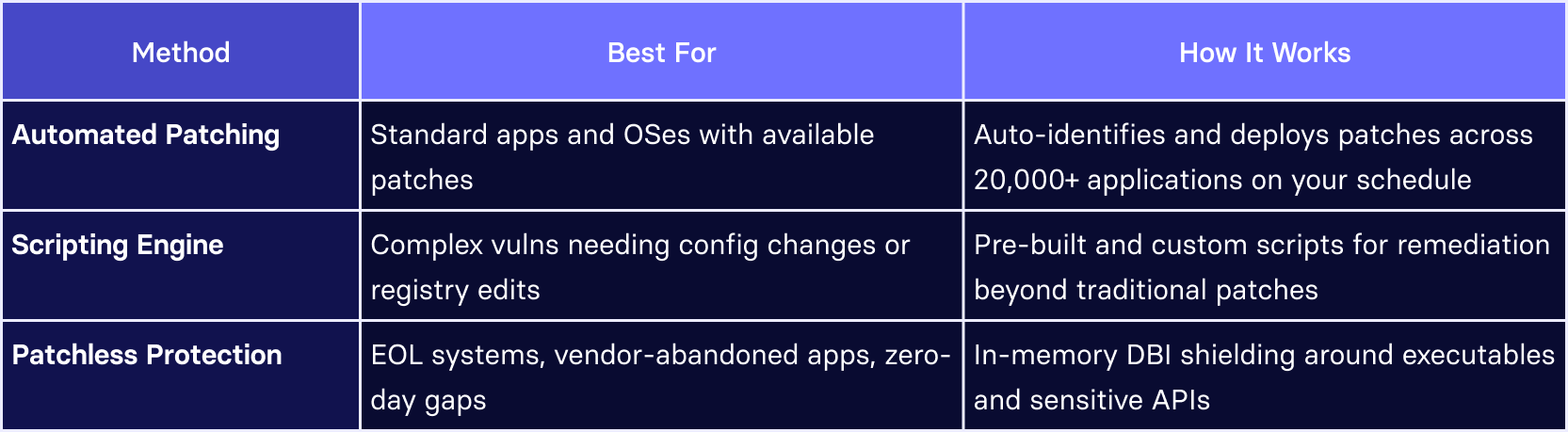
The power of this approach is that remediation decisions are no longer binary. You’re not choosing between “patch it” and “accept the risk.” You have a third path: reduce the risk to an acceptable level while maintaining operational continuity.
Real-world scenarios where this matters
Legacy OS that can’t be migrated yet: Your Windows Server 2012 R2 instance runs a business-critical ERP module. Migration is planned for Q3, but three new critical CVEs were published last month. Patchless Protection shields the server’s vulnerable services in-memory while your migration project proceeds on schedule.
Third-party app with no vendor support: That niche industry application your finance team depends on? The vendor was acquired two years ago and the product is in maintenance mode with no security updates. Rather than ripping it out (and the workflows that depend on it), you deploy vShield and bring the risk profile down to a level your CISO can live with.
Zero-day waiting on a vendor patch: A critical CVE drops on a Tuesday. Your vendor confirms they’re working on a fix, but the ETA is “weeks.” Instead of living with the exposure or taking the application offline, Patchless Protection acts as a bridge, mitigating the exploitable surface until the official patch is available and tested.
From scanner noise to measurable risk reduction
One of the most frustrating aspects of managing unpatchable assets is the audit and compliance loop. Your vulnerability scanner flags the same systems every cycle. You file the same risk exceptions. Your compliance team asks the same questions. Nothing changes, but everyone is busy.
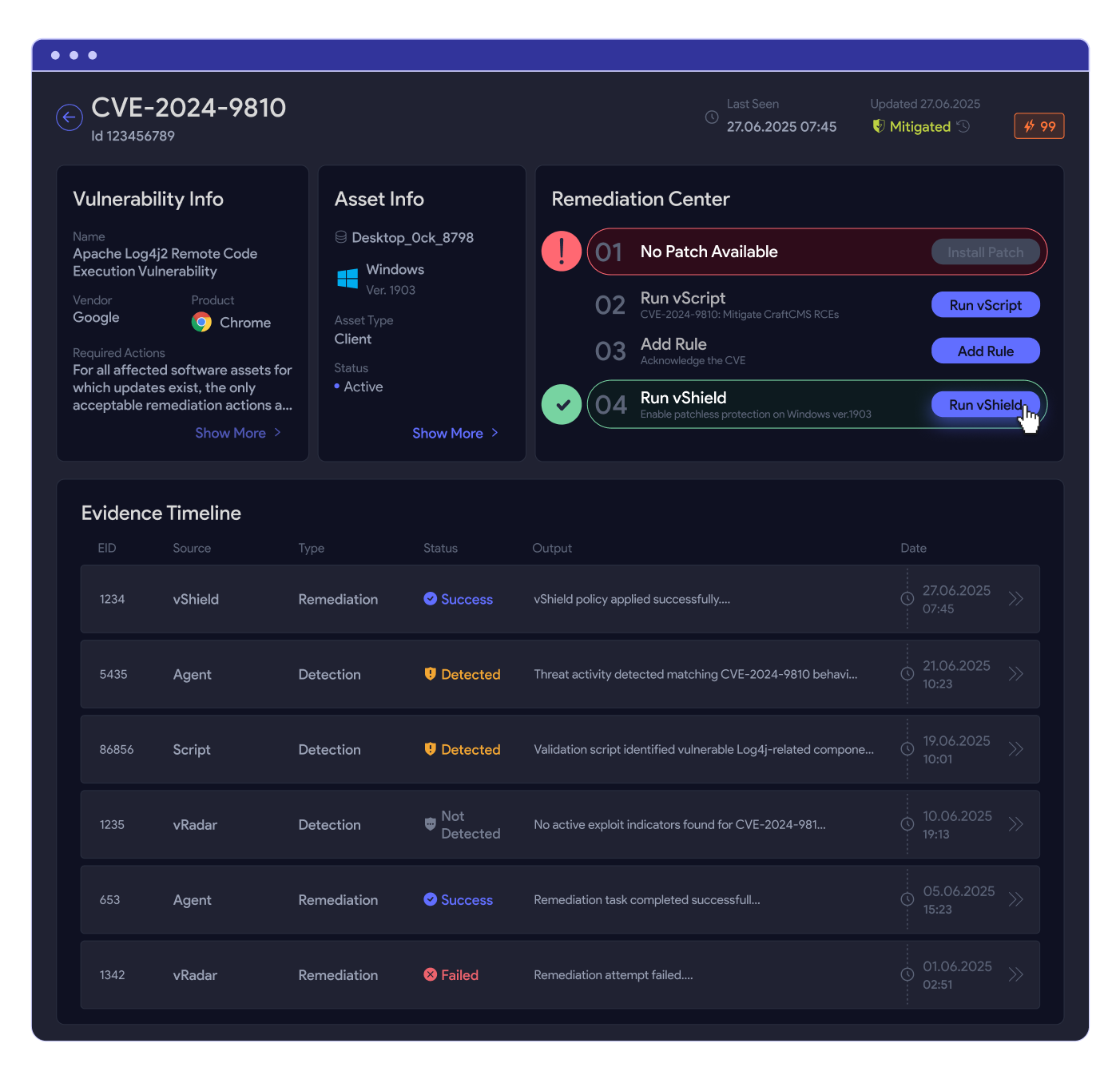
Patchless Protection breaks this cycle by giving you a documentable compensating control. When you activate vShield on a vulnerable asset, vRx reflects the reduced risk posture in its dashboard and reporting. Your audit trail shows a deliberate mitigation action not just an exception form. You’re demonstrating that you’ve reduced the exploitability of the asset, even if the underlying CVE still technically exists.
For organizations tracking Mean Time to Remediate (MTTR), this is significant. Vicarius customers report a substantially lower MTTR average and an 80% reduction in manual patching effort. That’s not just efficiency that’s a fundamentally different risk posture.
Getting started: what to expect
Deploying Patchless Protection through vRx is straightforward. The vRx agent runs on Windows, Linux, and macOS endpoints, providing real-time asset inventory and vulnerability discovery. Once your environment is scanned and prioritized, you can enable Patchless Protection on specific applications directly from the vRx dashboard with no additional agents, no complex configuration.
Most teams start by identifying their highest-risk unpatchable assets, the ones that keep showing up in audit findings or that their risk committee has flagged. From there, enabling vShield is a targeted action that immediately reduces the risk score for those assets.
Vicarius offers a two-week free trial with a guided onboarding session to validate that vRx fits your environment. It’s a low-friction way to see the impact on your specific unpatchable assets before committing.
Ready to close the gap on unpatchable risk?
See how Vicarius vRx brings your unpatchable assets to acceptable risk levels without downtime, without code changes, and without waiting for patches that may never come.
Also read:
When Patching isn't enough: how vRx's Scripting Engine closes the Remediation gap
From Alert Overload to Closed-Loop Security: Introducing vIntelligence