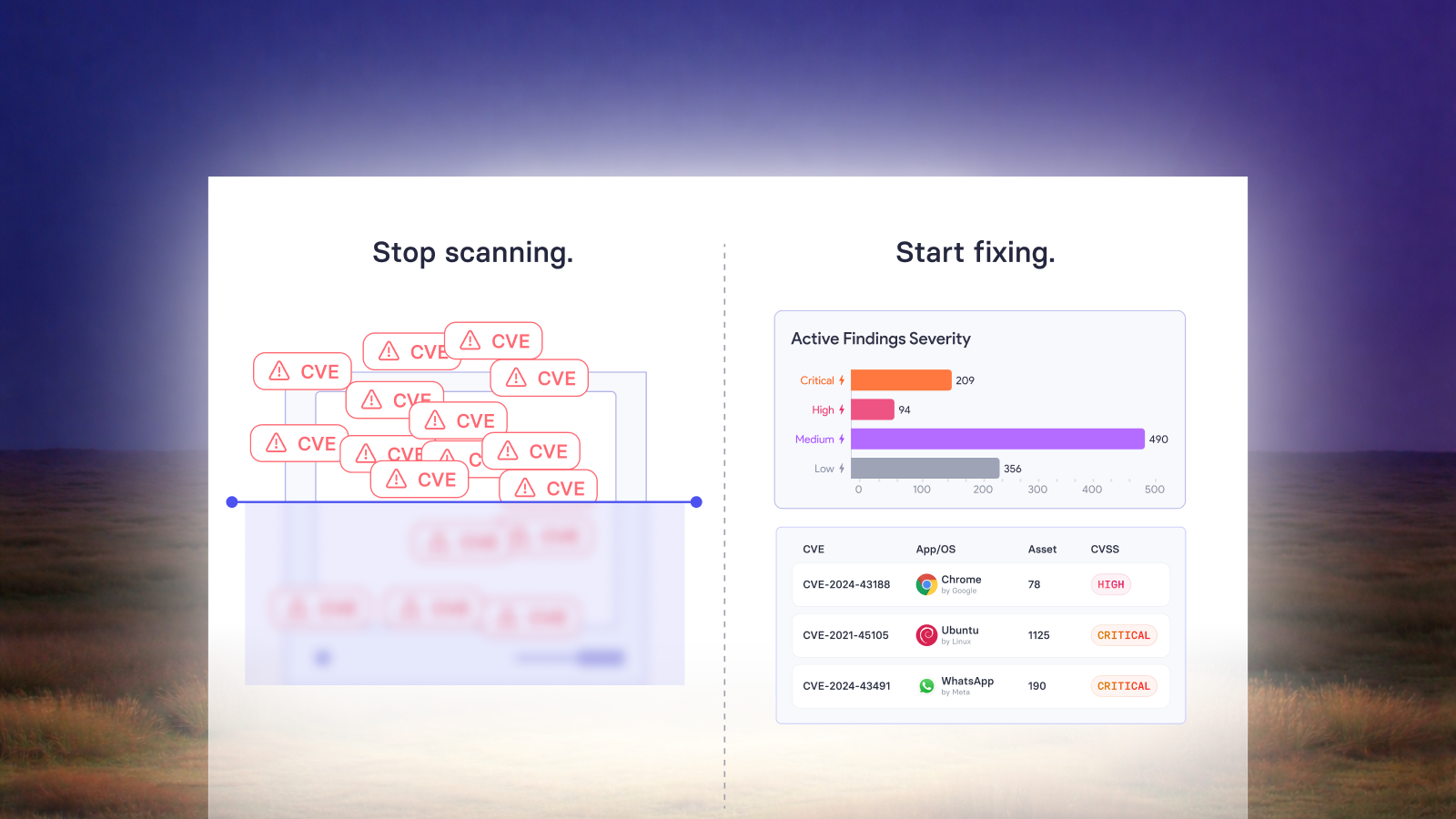
Not every vulnerability has a patch. And not every patch is one you can deploy right now.
Configuration-based CVEs, registry-level exposures, embedded vulnerable libraries like Log4j, end-of-life software on production systems these are the gaps where traditional patch management fails silently. The vulnerability is flagged, the ticket is opened, and then it ages in a backlog because no automated patch path exists.
This is the problem vRx's scripting engine was built to solve.
The Remediation Methods, and Where Scripting Fits
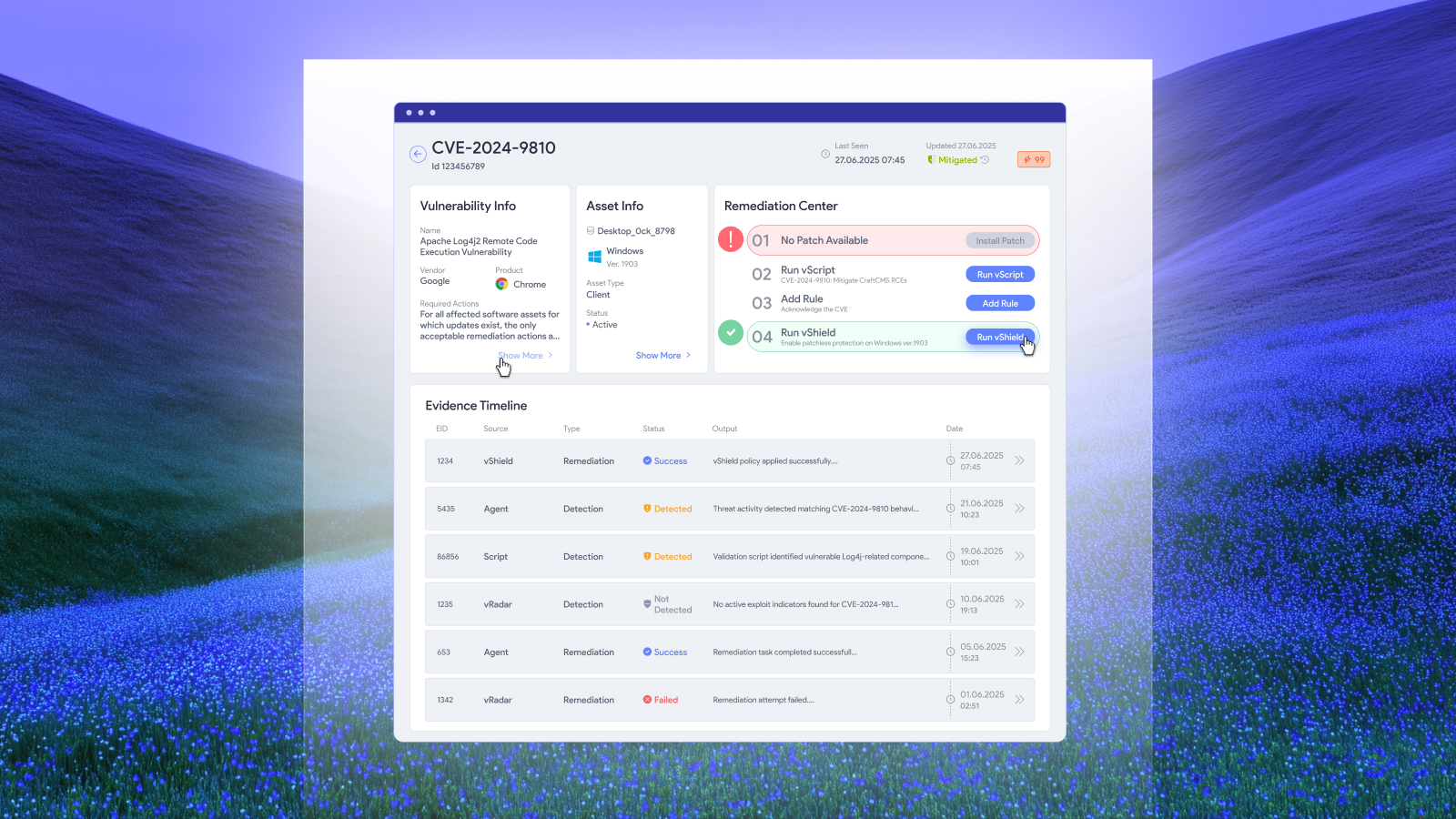
vRx provides three distinct remediation paths for vulnerabilities across Windows, macOS, and Linux:
Native Patching (vPatch)handles the standard case identifying missing patches across 10,000+ applications and OS versions, then deploying them on schedule. This is the high-volume, automated path that covers the majority of CVEs.
Patchless Protection (vShield) acts as a compensating control when a patch doesn't exist or can't be applied. It wraps an application's legitimate executables at the memory level, restricting access to sensitive API memory space. This bridges the window between disclosure and patch availability without changing system files or requiring restarts.
Scripting (vScript) addresses everything that falls outside those two categories of vulnerabilities that require specific configuration changes, registry modifications, file-level operations, or custom logic to remediate. This is where the scripting engine operates.
These three methods aren't alternatives to each other. They're complementary. A single environment will use all three simultaneously, applied to different vulnerability classes based on what each CVE actually requires.
What the Scripting Engine Actually Does
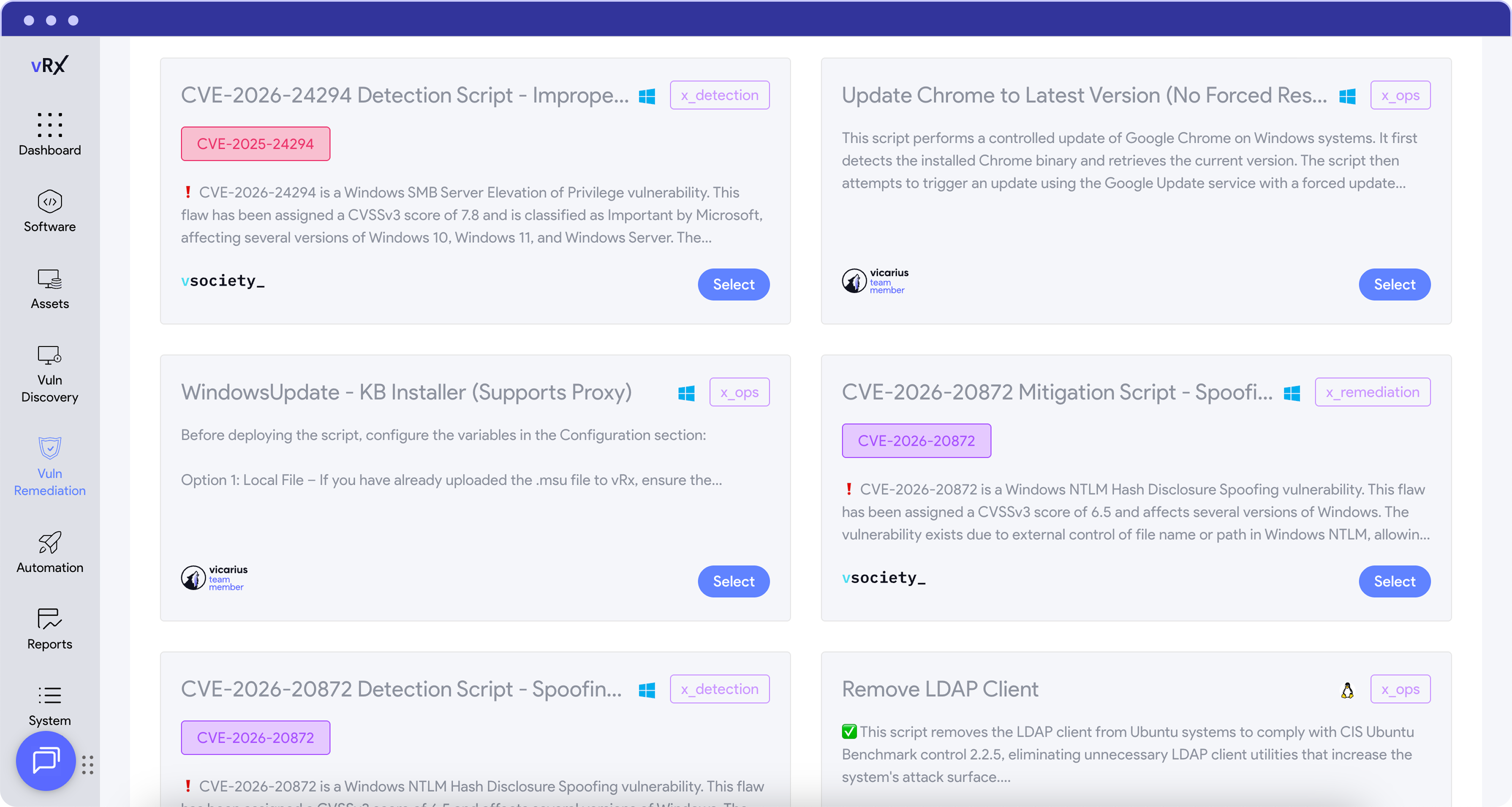
The vRx scripting engine executes scripts in PowerShell, Bash, and Batch across managed endpoints, with Windows, Mac and Linux operating systems. It supports both pre-built scripts from a curated library and custom scripts written by your own team.
Functionally, it handles operations like:
- Modifying Windows registry keys to disable vulnerable protocols or features
- Locating and updating vulnerable JAR files (the Log4j remediation pattern finding every instance of a vulnerable library embedded across disparate systems)
- Removing or replacing vulnerable components without uninstalling the parent application
- Closing specific ports or disabling services exposed by a CVE
- Applying hardening configurations that go beyond what a vendor patch addresses
- Creating system restore points before executing changes
- Uninstalling and reinstalling specific software versions from within the platform
- Running detection scripts that audit systems for misconfigurations or policy drift
- Enforcing PowerShell Constrained Language Mode or disabling legacy PowerShell v2.0 across endpoints
Scripts can be executed manually, on approval, or fully automated through policy-based rules tied to risk severity, asset type, compliance requirements, or maintenance windows.
Every script execution is logged and tracked. The platform records which vulnerabilities were addressed, how, and when producing an audit trail for compliance reporting.
Where Scripts Come From: Three Sources
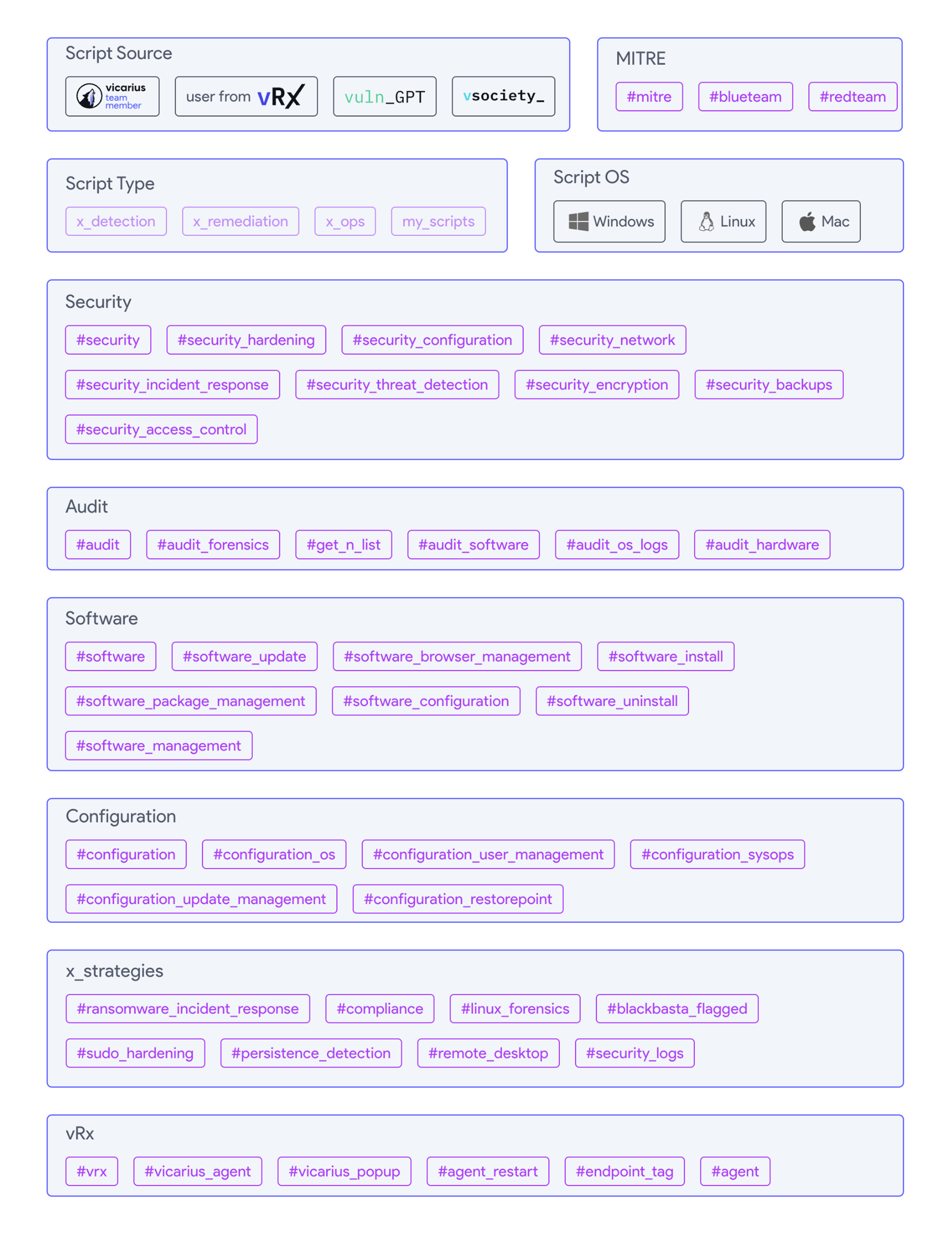
The script library in vRx is populated from three distinct channels:
The Vicarius Research Team produces detection and mitigation scripts for trending CVEs. When a high-profile vulnerability surfaces, the internal team builds and publishes validated scripts that vRx customers can deploy directly. These cover both x_detection (identifying whether the vulnerability is present) and x_remediation (applying the fix).
vsociety and vRx users, Vicarius is an open community platform for security researchers and analysts. Researchers publish new scripts including CVE analyses, exploit assessments, and remediation code which Vicarius verifies before making them available in the vRx dashboard. The community has grown to over 4,000 active members contributing across categories like x_detection, x_remediation, x_ops, CVE analysis, and exploit analysis.
vuln_GPT is an LLM-based engine trained specifically to generate remediation scripts for software vulnerabilities. It can produce scripts that close ports, delete files, disable protocols, or apply compensating controls actions that serve as interim fixes while a vendor patch is developed or tested. All vuln_GPT-generated scripts go through a validation step before being published to the commercial platform. The engine supports Windows, Linux, and macOS targets and is available for free within vsociety.
This three-source model means the script library isn't static. It's continuously updated by internal research, community contribution, and AI-generated content all with a verification layer before production deployment.
The Practical Use Cases
The scripting engine matters most in scenarios where patching either doesn't exist or isn't operationally viable.
Embedded library vulnerabilities. Log4j is the canonical example. The vulnerability didn't live in a single application binary; it was embedded in JAR files scattered across thousands of systems, inside applications that had no centralized update path. Remediation required scanning file systems for vulnerable library versions and applying targeted fixes per instance. That's a scripting problem, not a patching problem.
Configuration-based CVEs. Many vulnerabilities are rooted in how software is configured, not in the software version itself. A registry key that enables a deprecated protocol, a service running with excessive permissions, a default setting that exposes an attack surface. These require configuration changes, not binary updates.
Legacy and end-of-life systems. Production environments running software that no longer receives vendor patches still need risk reduction. Scripts can apply hardening measures, disable vulnerable features, or restrict attack surface without requiring an upgrade that may not be operationally possible.
Zero-day response. When a CVE is disclosed but no vendor patch exists yet, scripting provides the mechanism to deploy compensating controls across the fleet immediately. Close the port, disable the protocol, restrict the access path reduce exposure while the patch is developed.
Post-incident hardening. After a security event, scripting enables rapid deployment of forensic analysis (enabling PowerShell logging, collecting system state) and hardening actions (enforcing constrained execution modes, disabling legacy protocol versions) across affected systems.
Compliance enforcement. Auditing systems against security baselines checking that configurations match organizational or regulatory requirements is a detection scripting function. When drift is found, remediation scripts bring systems back into compliance.
How It Integrates Into the Workflow
The scripting engine isn't a standalone tool. It operates within vRx's broader remediation architecture:
A vulnerability is discovered through vRx's scanning engine. It's prioritized using contextual risk scoring that accounts for asset criticality, exploitability, and business impact, not just CVSS. If the vulnerability maps to a patch, native patching handles it. If no patch is available or applicable, the platform presents scripting and patchless protection as alternative remediation paths.
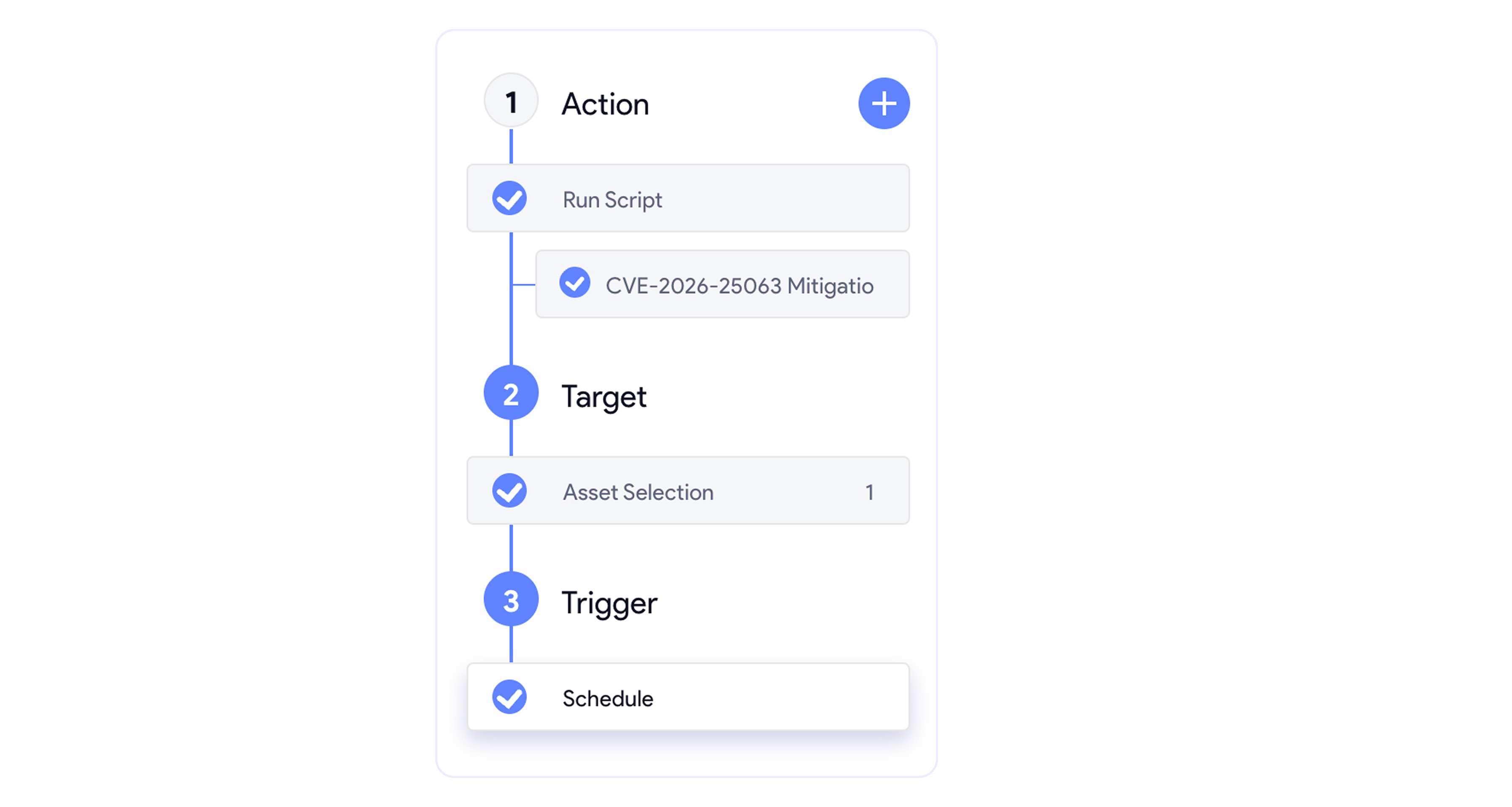
For scripting, the operator can select from the pre-built library, deploy a vuln_GPT-generated script, or upload a custom script. Execution can be immediate or scheduled. Policy-based automation allows scripts to run automatically when conditions are met for example, auto-remediating any critical configuration-based CVE on production endpoints during the next maintenance window.
All actions feed back into vRx's dashboards, updating remediation status, risk scores, and compliance posture in real time. SIEM integrations push this data into the broader security operations workflow.
What This Changes Operationally
The typical vulnerability management workflow breaks at the handoff between "identified" and "fixed." A scanner finds the vulnerability. A ticket is created. An engineer researches the fix. The fix is tested. The fix is deployed. This process can take weeks or months for non-patchable vulnerabilities.
The scripting engine compresses that timeline by providing a direct execution path from detection to remediation within a single platform. The research step is shortened by the pre-built library and vuln_GPT. The testing step is reduced by validated scripts. The deployment step is automated by the execution engine.
This doesn't eliminate the need for human judgment. But it does eliminate the operational gap where vulnerabilities sit unaddressed because no one had time to write the PowerShell script, test it in a lab, and figure out how to push it to 3,000 endpoints.
That gap is where attackers operate. Closing it is the point.
Also read:
From Alert Overload to Closed-Loop Security: Introducing vIntelligence
Why the vRx by Vicarius Scripting Library is one of the most loved capabilities