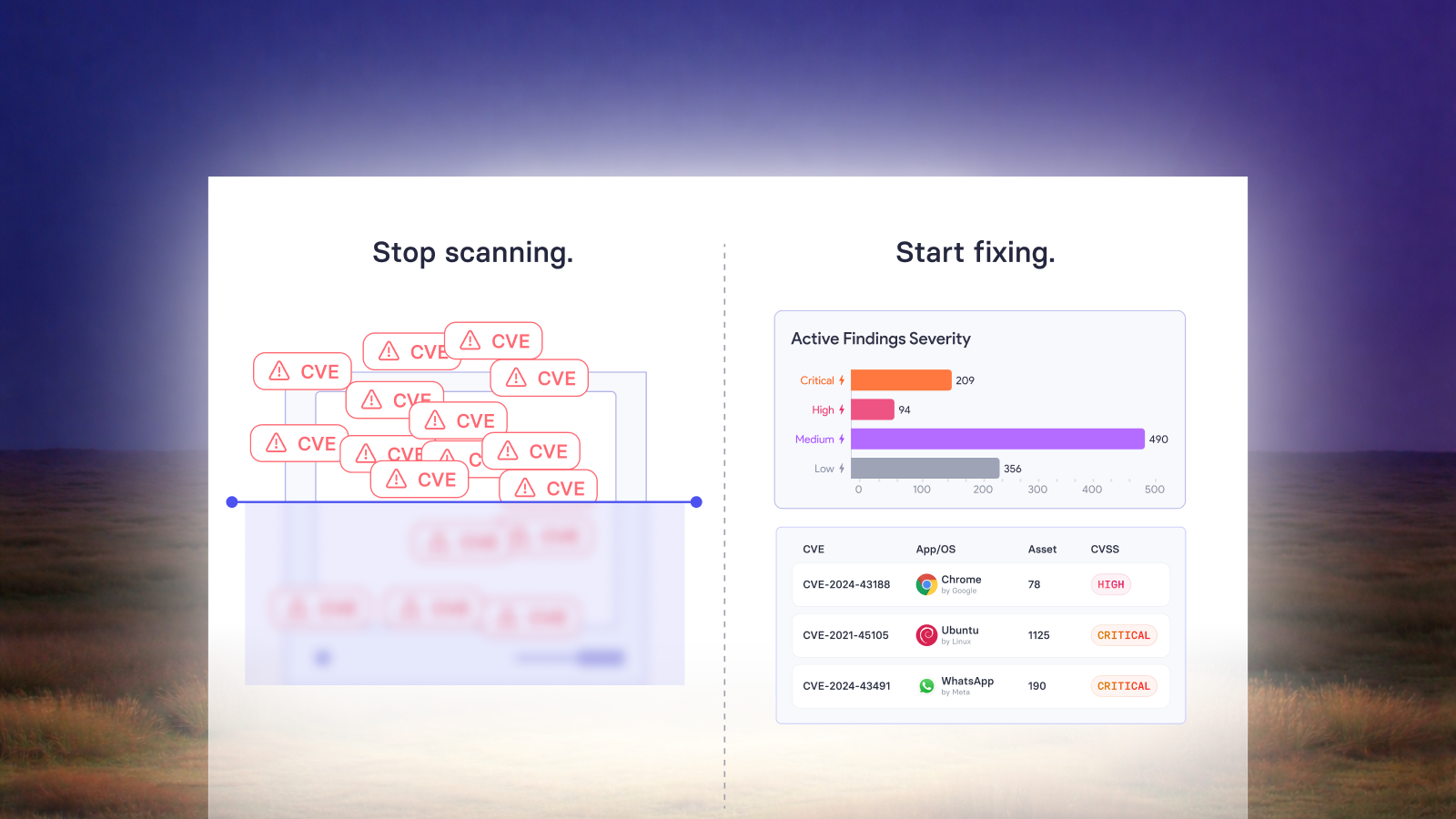
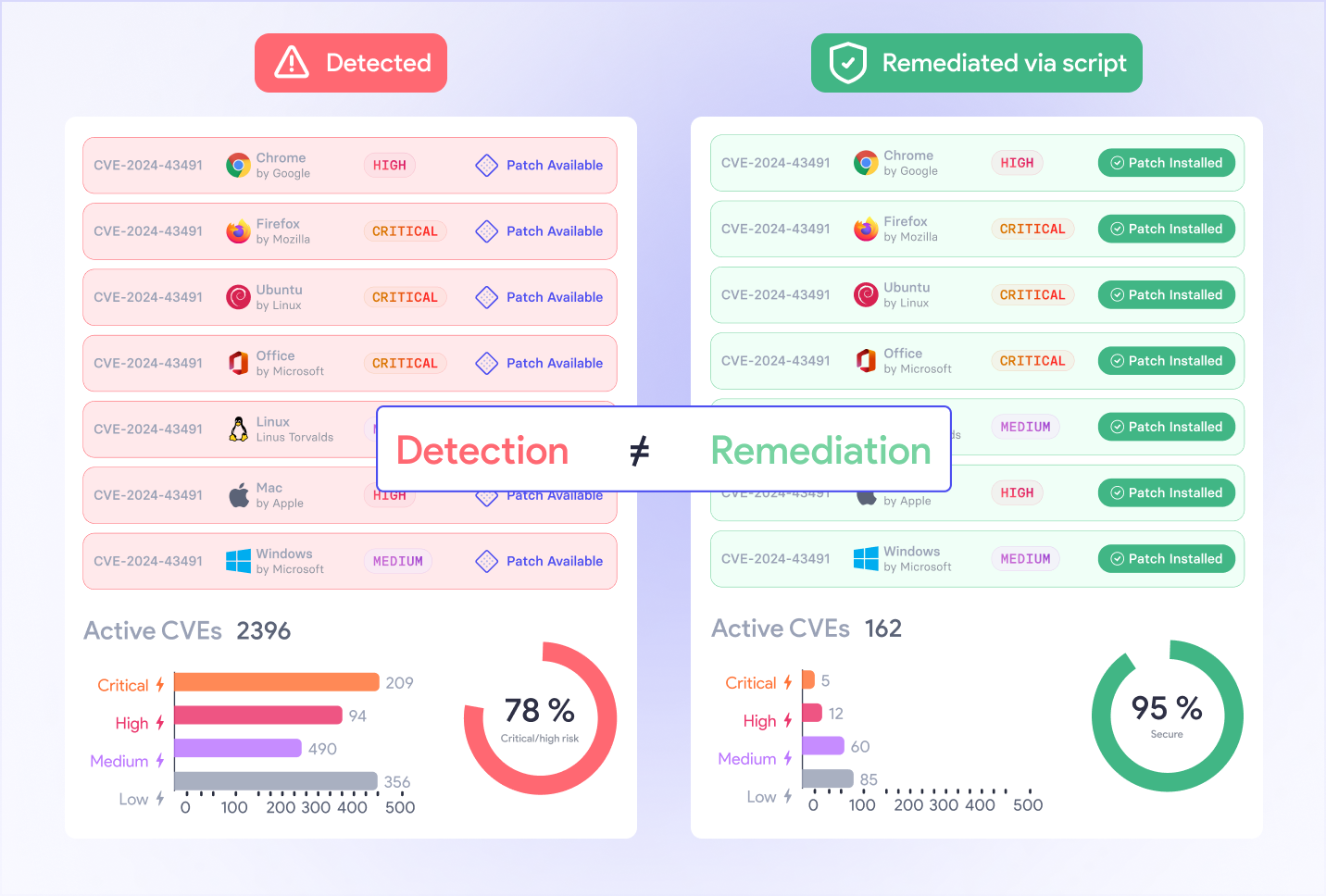
There's a dirty secret in vulnerability management, most tools are great at telling you what's broken and terrible at helping you fix it.
That's what makes the vRx scripting library different, and why it consistently ranks among the most loved features by vRx users. It's not just a library. It's an ecosystem where community researchers, an internal research team, and an AI engine called vuln_GPT converge to produce actionable detection and remediation scripts often within hours or days of a vulnerability going public.
The Problem the Scripting Library Solves
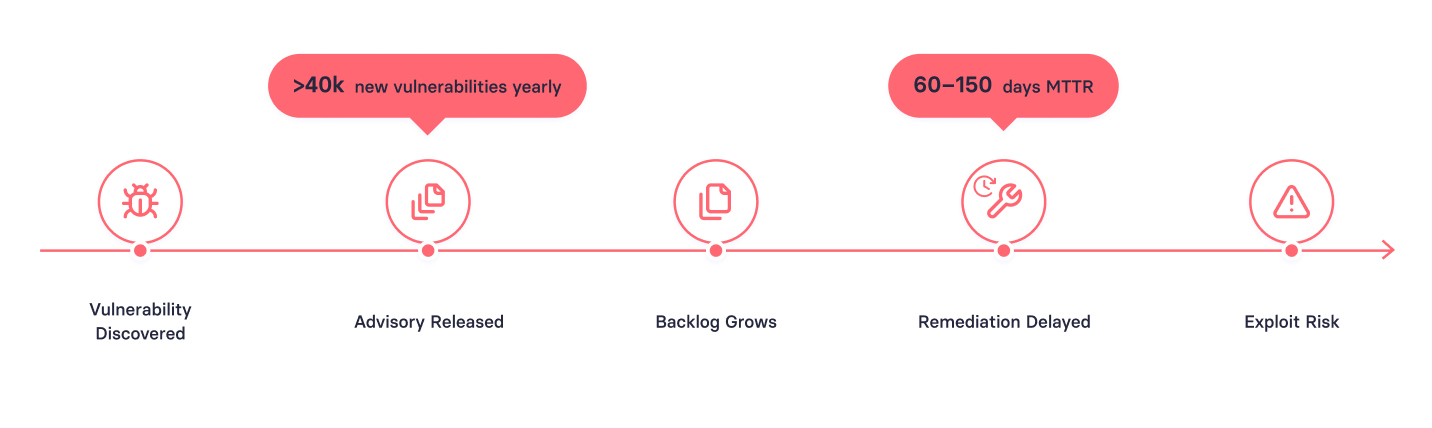
Over 200,000 known vulnerabilities exist in the wild, with roughly 20% discovered in the last year alone. The average MTTR for critical vulnerabilities? Between 60 and 150 days. And patching doesn't cover everything configuration-based issues, registry-level flaws, and protocol weaknesses require something more surgical.
That gap between "we know about it" and "we've actually fixed it" is where the scripting library lives.
How the Ecosystem Works: Three Sources, One Library
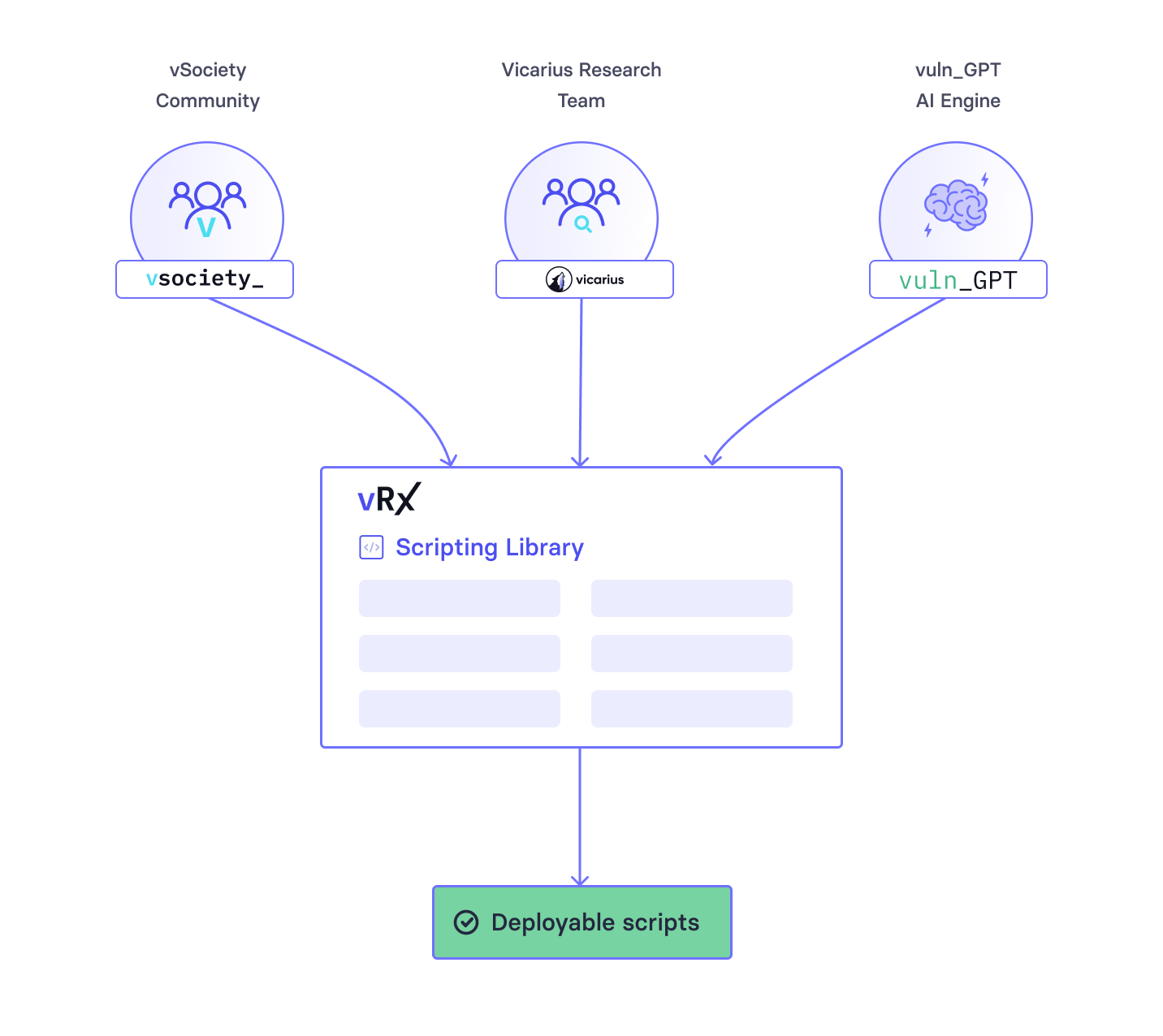
The scripting library isn't a static repository updated quarterly. It's fed by three distinct sources, each contributing verified scripts available directly in the vRx dashboard.
The vsociety Community. Launched at Black Hat USA 2022, vsociety is Vicarius' open research community where security researchers collaborate and contribute scripts. With over 4,000 active members and a thriving Discord, it operates like a social network built for actionable security research. Researchers earn vcoins based on contribution quality, redeemable through the vstore for security hardware and tools.
The incentive model is clear: develop a detection or remediation script with a video walkthrough and earn up to $100 per publication. Thorough CVE analysis with reproduction steps? Up to $500. Discover a vulnerability with no assigned CVE or publish a novel exploit? Up to $650.
The Vicarius Research Team. Internally, Vicarius maintains a dedicated research team that creates detection and mitigation scripts for trending CVEs the ones making headlines and keeping security teams up at night. When a high-profile vulnerability drops, this team mobilizes to get scripts into the library fast.
vuln_GPT. Announced at Black Hat 2023, vuln_GPT is Vicarius' purpose-built LLM trained to generate remediation scripts for software vulnerabilities. When a user queries the system something as simple as requesting a remediation script for a specific CVE vuln_GPT first searches Vicarius' vector database for existing solutions. If none exist, it generates a new script. Every script goes through validation before publishing, with human oversight catching hallucinations or non-functional outputs before they reach users.
All three sources feed into the same library, all scripts are verified, and all are deployable across Mac, Windows, and Linux directly from vRx.

Speed That Actually Matters
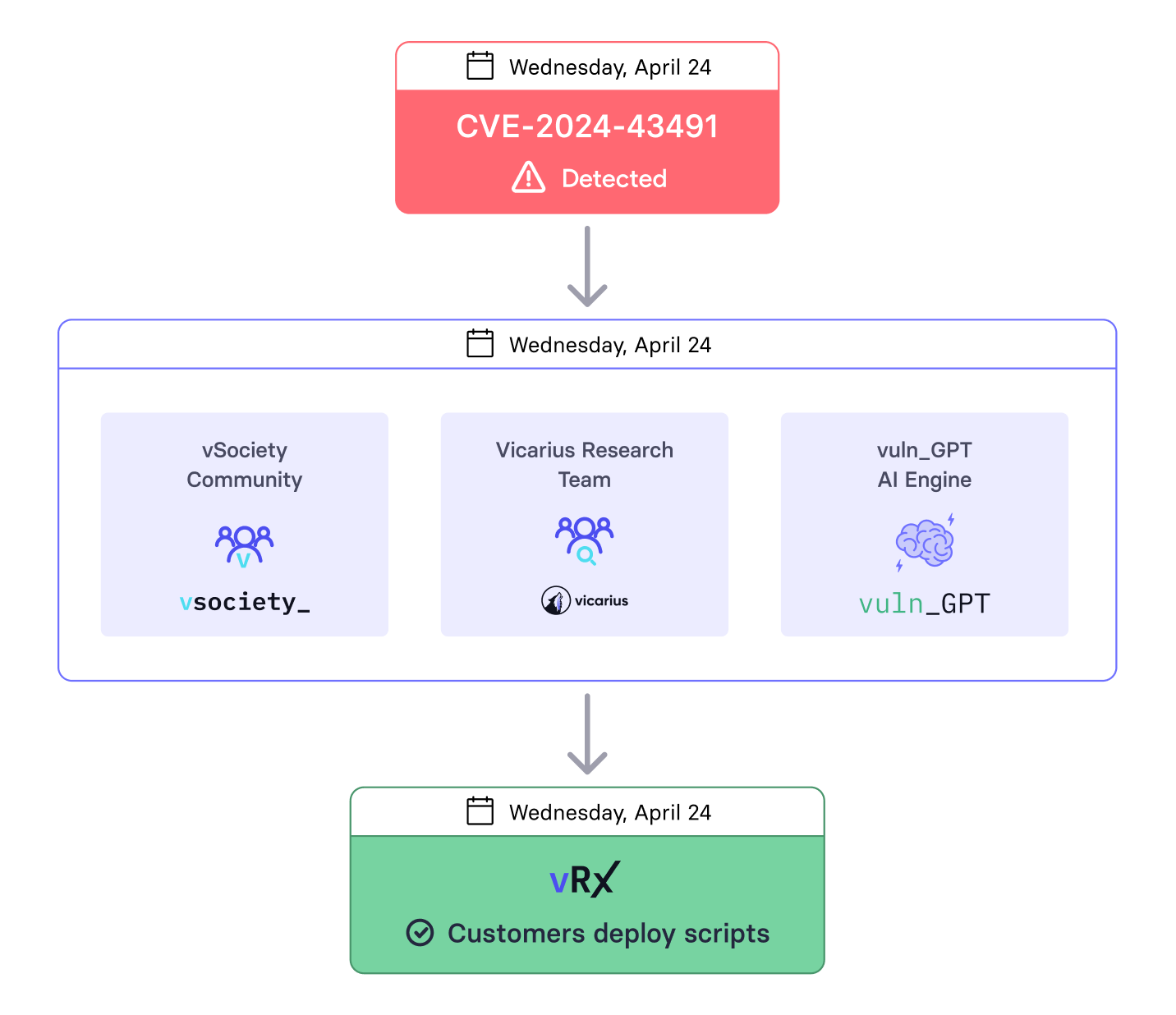
Here's where the scripting library earns its reputation: response time.
When the XZ Utils backdoor (CVE-2024-3094) was discovered in March 2024, it was a supply chain nightmare malicious code embedded in upstream tarballs of xz starting with version 5.6.0, compromising liblzma and creating a backdoor with a critical 10.0 CVSS score affecting Linux distributions globally.
The vsociety response was immediate. Both detection and remediation scripts were published covering *NIX and macOS environments. Multiple researchers contributed from version checking and service disabling to full remediation workflows. For vRx users, that meant detecting and mitigating the threat from within their existing platform while the broader community was still assessing scope.
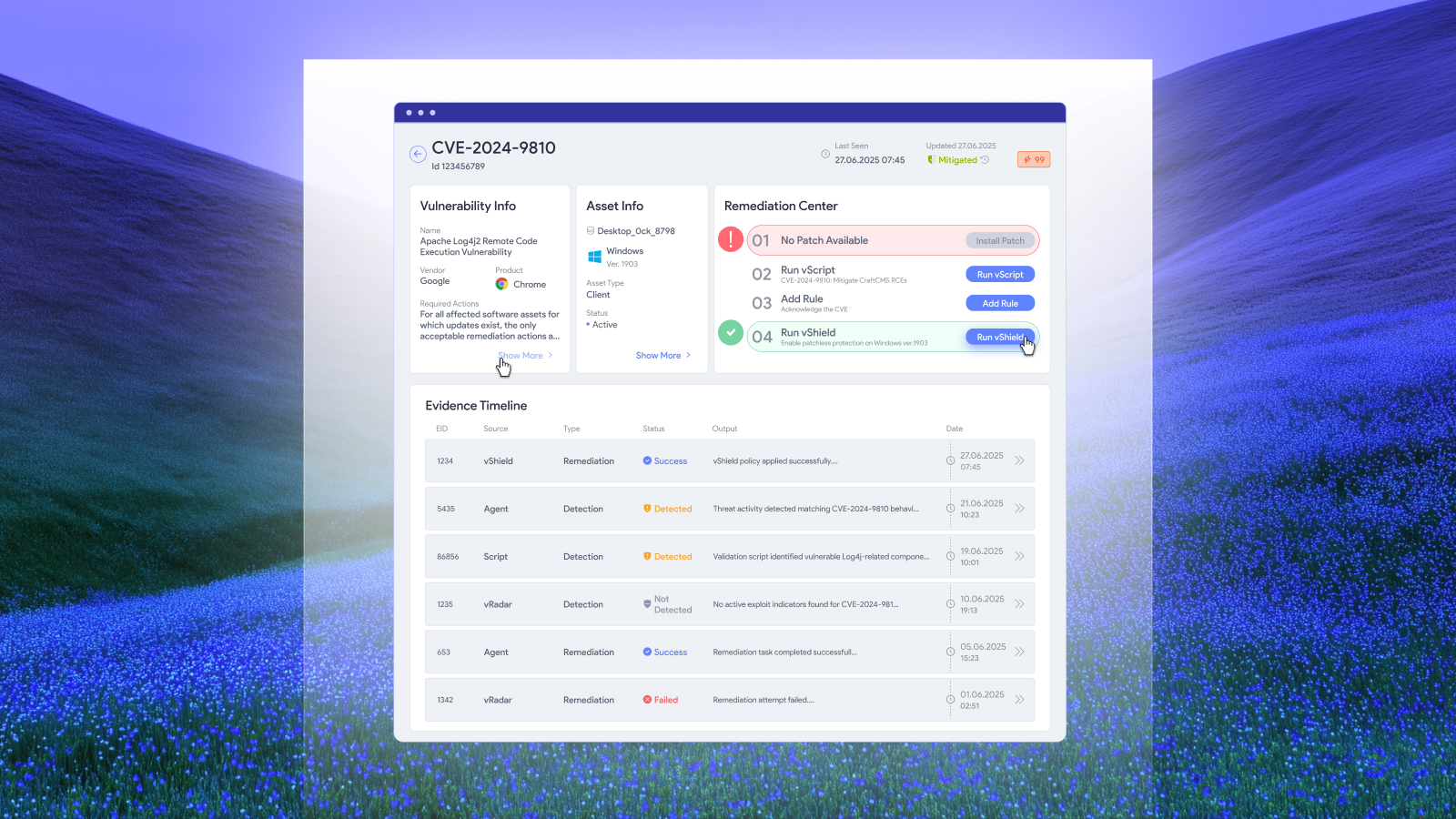
This pattern repeats. When CVE-2025-21399 a 7.4 CVSS privilege escalation in Microsoft Edge's update mechanism surfaced, the library already had detection and mitigation scripts that disabled Edge update services, renamed vulnerable executables, blocked automatic updates via registry, and applied ACL restrictions. The matching detection script verified installed versions against the vulnerable range and confirmed each mitigation was in place.
This speed isn't accidental. It's the compound effect of a community, an internal team, and an AI engine all working in parallel all pushing scripts through a verification pipeline into the same library.
Finding What You Need: Script Categories
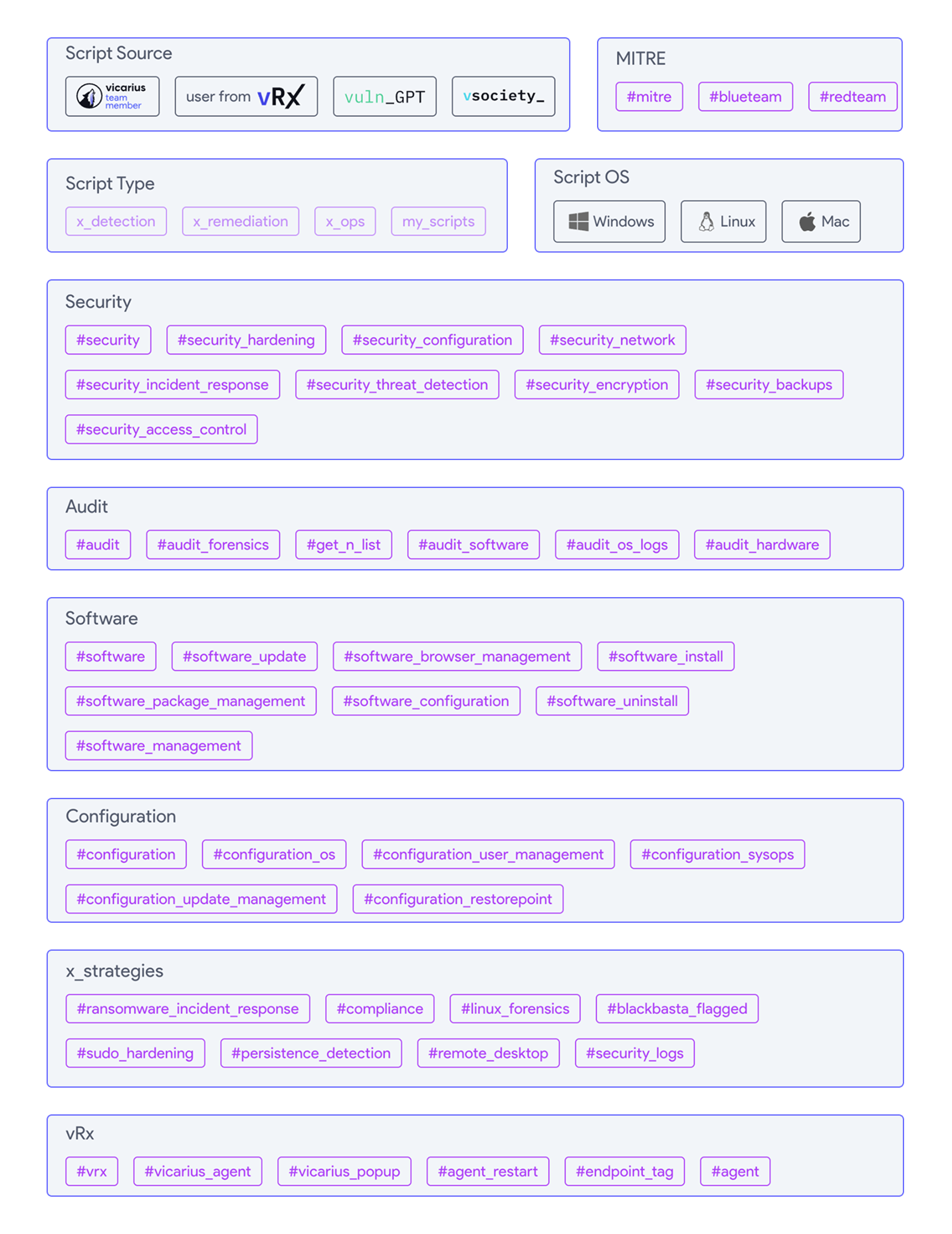
One of the understated strengths of the scripting library is how it's organized. Scripts are tagged so both security engineers and IT admins can find what they need without digging through noise.
The primary categories include x_detection scripts that identify whether a vulnerability exists in your environment; x_remediation scripts that apply fixes from closing ports and disabling protocols to modifying configurations; x_ops scripts for operational tasks like system audits and user management; and x_translation scripts that translate vulnerability data into actionable context.
Beyond these, vSociety content is tagged by research depth: CVE analysis for thorough vulnerability breakdowns, novel exploit analysis for previously-unpublished PoC work, and vulnerability with no assigned CVE for flaws vendors haven't formally recognized.
For each CVE listed in vsociety, the page invites contributions "suggest your own xdetection," "suggest your own xremediation" making the library a living resource, not a locked archive. This means multiple script options often exist for the same vulnerability, covering different environments and mitigation strategies.
What Users Are Actually Saying
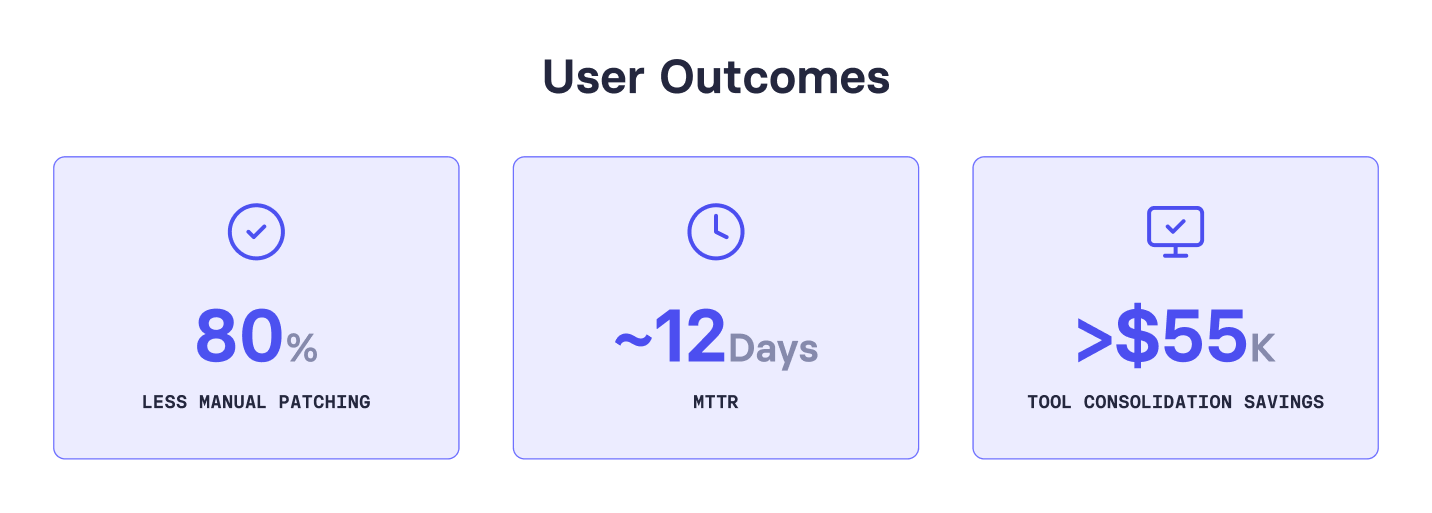
The numbers tell a clear story: vRx users report an 80% reduction in time spent on manual patching, an average MTTR of 12 days (against an industry average stretching into months), and over $55K in savings from consolidating tools.
On the qualitative side, feedback consistently points to the scripting engine as a differentiator. One IT Manager reported MTTR dropping 60% to 70%. A VP of Managed Technology & Services saw 80% improved efficiency after automating third-party patching. A Security Analyst shared that patching Windows Server went from three hours to under one.
The community angle is what makes this sticky. A vulnerability researcher shared that his growth on vSociety surpassed the professional development of his previous three years combined calling the platform's rigorous approach to reproduction steps, proof-of-concept, and exploit analysis what makes every contribution trustworthy enough for production. Researcher Basant Singh described vSociety as a close-knit family of security professionals who hunt down vulnerabilities and cultivate cutting-edge research together.
Why This Approach Works (When Others Don't)
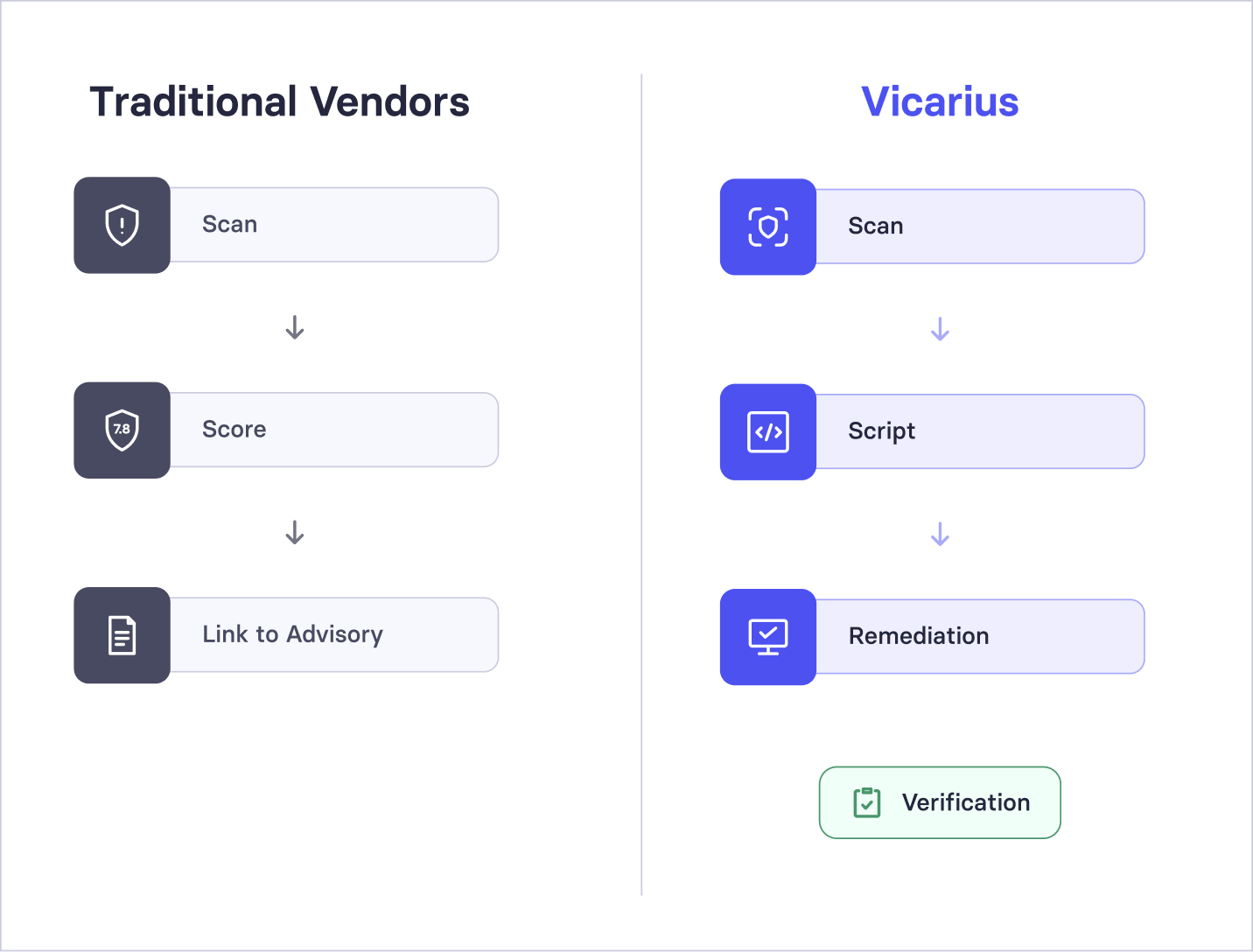
Most vulnerability management vendors treat remediation as someone else's problem. They scan, score, and prioritize but when it's time to actually fix something, you're on your own with a link to a vendor advisory, that not “True Remedition”
Vicarius flipped this by making remediation the core of the platform. The community ensures coverage breadth thousands of researchers covering vulnerabilities no single internal team could keep up with. The internal research team ensures coverage depth targeted scripts for the highest-priority CVEs. And vuln_GPT ensures coverage speed AI-generated scripts that bridge the gap while human-written solutions are developed.
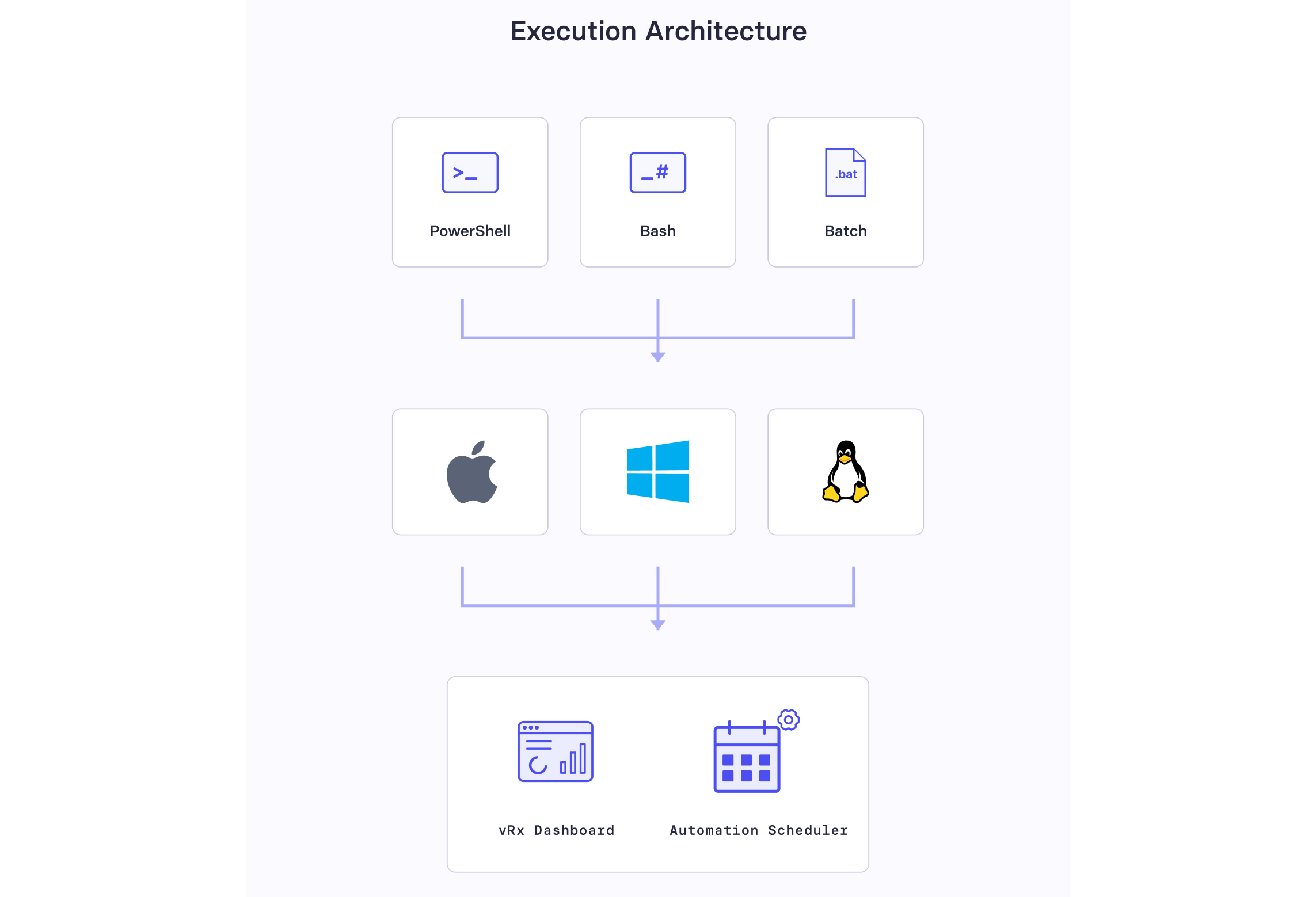
The scripting engine supports PowerShell, Bash, and Batch execution across Mac, Windows, and Linux. Scripts can be run manually or automated through vRx's scheduling tools. An IT admin can run a detection script across their fleet, identify exposed assets, then deploy the corresponding remediation all from the same dashboard, without switching tools or writing anything from scratch.
For security teams that are short-staffed (which is nearly all of them), this is the difference between a vulnerability sitting in a backlog for weeks and getting addressed in days.
The Bigger Picture

The scripting library doesn't exist in isolation. It's part of a broader remediation strategy that includes automated patching across 10,000+ applications, patchless protection for when no patch is available, and risk prioritization powered by contextual intelligence. The scripts handle what patches can't the configuration changes, registry modifications, and compensating controls that make up a significant portion of real-world remediation.
That's why users love it. Not because it's flashy. Because when a critical vulnerability drops, they're not starting from zero. They're deploying a script that someone has already written, tested, and verified often before the vendor has even released a patch.
Ready to see the scripting library in action? Join the vsociety community to explore the latest scripts and research, or request a demo of vRx to see how the full remediation platform works in your environment.